blended threat
What is a blended threat?
A blended threat is an exploit that combines elements of multiple types of malware and usually employs various attack vectors to increase the severity of damage and the speed of contagion. These attacks often inject malicious code into an executable file stored on a target device.
A blended attack may contain zero-day exploits that are executed one after the other, causing a trickle-down effect that can be deadly for network systems. Although they may be identified as computer viruses, worms or Trojan horses, most current exploits are blended threats.
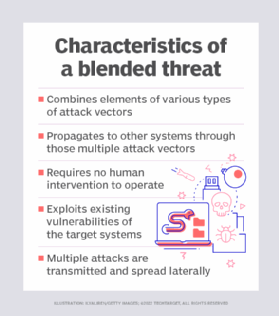
Characteristics of a blended threat
A blended threat is a type of cybercrime that exploits the vulnerabilities related to the complex requirements in modern-day software applications. Most large-scale software projects undergo extensive software testing, but even so, they often have some bugs. Developers must compromise between network security and usability of an app and timely deployment. This means software goes into use with some vulnerabilities.
In addition, software packages from a variety of vendors are often installed on a single machine, leading to complex and hard-to-manage interactions. This leaves an open backdoor for blended threats to pit software against software through a series of attacks. Since many programs are affected simultaneously, it can be difficult to contain a blended threat once it begins.
Blended threats are typically characterized by the following attributes:
- More than one means of propagation. For example, this can include sending an email with a hybrid virus or worm that self-replicates and infects a web server so that contagion spreads through all visitors to a particular site.
- Exploitation of vulnerabilities. These may be preexisting vulnerabilities, or they may be malware distributed as part of the attack.
- Intent to cause real harm. Blended threats do this by launching a denial of service (DoS) attack against a target or delivering a Trojan horse that will be activated at a later date.
- Automation. With automation, the contagion can spread without requiring any user action.
How does a blended threat work?
Blended threats fuse multiple methods and techniques for attacks in a single payload. The aim is to impair several areas of a computer system and its functionality simultaneously.
To understand how a blended attack works, here's an example of the steps followed:
- A threat actor launches a phishing campaign or sends an email containing a malicious link.
- Unsuspecting users click on the malicious link, and it redirects them to an infected website that has a hidden payload.
- Once the users click on a link on the infected website, the payload is triggered and installs a Trojan worm, which acts as a backdoor for system infiltration and creates a botnet.
- This botnet launches a distributed DoS (DDoS) attack to bring down another website or network using the originally infected resources and other endpoints.
- While the security team scrambles to deal with the DDoS attack, the cybercriminals install a rootkit on the web server that gives them even more access to the company's network and sensitive data.
The above blended threat example uses a combination of two attack vectors to carry out the attack. The first vector is the phishing email, which is a means of getting users to the infected website. The second one is the hidden payload on the infected website.
To prevent blended threats, experts recommend network administrators take proper security measures and be vigilant about patch management. Security measures include using good firewall products and server software to detect malware and educating others about proper email handling and online behavior.
What is the most common type of blended attack?
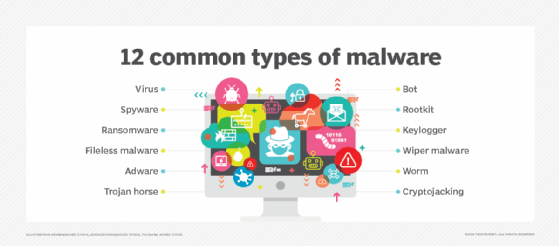
The most common types of blended attacks combine phishing emails or instant messages, malware, worms, spyware, viruses and social engineering tactics that lure unsuspecting users to click on malicious code and links on infected websites.
A blended attack can propagate through both wired or wireless networks and can exploit existing or unknown vulnerabilities. Worst of all, a blended threat can mutate rapidly to avoid detection. For example, in April 2011, a large-scale blended cyberthreat carried out in the form of an Structured Query Language injection attack compromised several thousand websites, including a few catalog pages from the Apple iTunes music store.
Notable examples of blended threats
Blended threats date back to November 1988 when the Morris worm was introduced. Hackers exploited flaws in the standard Berkeley Software Distribution system to use remote shell commands to access target machines and attempt to crack encrypted passwords.
Since then, other blended security threats and attacks have occurred, including the following examples:
- Code Red. The Code Red worm was the first of its kind to target wide-scale enterprise networks. It was observed on July 15, 2001. It attacked computers running Microsoft's Internet Information Services web server and defaced the targeted websites through a DoS attack. Code Red is thought to have caused billions of dollars in damage.
- Nimda. Also categorized as a computer worm, Nimda originated in China and was first released on Sept. 18, 2001. It affected computers running Windows 95, 98, NT and 2000/XP, along with Windows NT and 2000 servers. It was classified as a blended threat because of its five infection chain vectors. It mainly spread through victims opening the emails, browsing malicious websites and connecting to infected shares. It also exploited vulnerabilities and backdoors that Code Red had left open.
- Bugbear. This virus emerged in early October 2002 and infected thousands of computers through a multipronged cyber attack. Its mode of operation was to first spread through an email attachment that was 50,688 bytes long. If the first attempt was unsuccessful, Bugbear tried to distribute itself through network shares. Once a system was infected, the virus added itself to a subdirectory in a Windows folder and then added itself to the Startup folder. This malicious virus had Trojan capabilities that could terminate firewalls, antivirus and antimalware.
- Zeus Panda. This is a variant of the original Zeus Trojan, which has been used as a banking Trojan worm in recent times. Attackers carry out this attack by poisoning the Google search results in hopes of stealing user credentials. The attack specifically targets keyword searches related to finance and the banking industry. When users click on the fake search result, they are taken to websites that have malicious documents. Once these documents are opened, the malware gets installed on end users' devices.
Various attack vectors, including blended threats, are responsible for the rapid expansion of the cybersecurity threat landscape. Learn about the top five cybersecurity vulnerabilities and how to fix them.








