What is cyberstalking and how to prevent it?
Cyberstalking is a crime in which someone harasses or stalks a victim using electronic or digital means, such as social media, email, instant messaging (IM), or messages posted to a discussion group or forum. Cyberstalkers take advantage of the anonymity afforded by the internet to stalk or harass their victims, sometimes without being caught, punished or even detected.
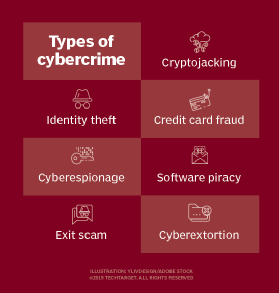
The terms cyberstalking and cyberbullying are often used interchangeably. Cyberstalking, however, is actually a form of cyberbullying, which -- along with cybersquatting and cyberterrorism -- is among the growing number of computer- and internet-related crimes, collectively referred to as cybercrime.
As digital communication expands, cyberstalking has evolved to include more sophisticated methods, such as geotracking, spoofing and hacking to target victims.
Types of cyberstalking
Although cyberstalking is a general term for online harassment, it can take many forms, including the following:
- Slander and defamation: Posting false or harmful statements about the victim.
- False accusations: Making baseless claims to damage the victim's reputation.
- Trolling: Provoking or harassing the victim through inflammatory comments.
- Doxing: Revealing private information about the victim, such as their address or financial details, to intimidate or endanger them.
- Threats: Sending intimidating or harmful messages to the victim or their loved ones.
Cyberstalkers often start small. In the beginning, they might send a few strange or somewhat unpleasant messages to their intended victim. Then, later, they might brush off these messages as funny, annoying or mildly weird and ignore them without taking any action.
Over time, the messages might become systematic, sustained and repetitive and take on an increasingly intimidating or frightening tone.
Emerging technologies in cyberstalking
Advances in technology have given rise to new forms of cyberstalking:
- Geotracking tools. Perpetrators use GPS-enabled devices and apps to monitor victims' real-time locations.
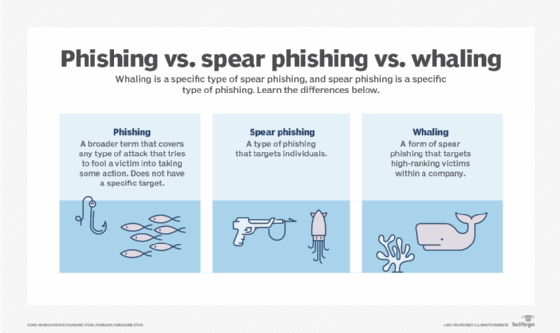
- Social engineering. Cyberstalkers manipulate victims into revealing sensitive information through phishing emails or fake accounts.
- Deepfake technology. Manipulating videos or images to create fake content aimed at defaming or blackmailing victims.
- IoT exploitation. Smart home devices, such as cameras or voice assistants, are hacked to monitor victims' activities.
These technologies increase the complexity of cyberstalking cases and demand advanced cybersecurity measures for protection.
Direct and indirect cyberstalking
Cyberstalking can be direct or indirect.
Direct cyberstalking
Perpetrators might directly email their victims or flood their inboxes with emails. Or they might harass them through IM, voicemail, texting or other forms of electronic communication. They might use technologies to surveil or follow their victims or continuously view their pages -- often without their knowledge.
Indirect cyberstalking
In indirect attacks, perpetrators might infect devices with ransomware to lock victims' files and demand payment or install keystroke loggers to steal sensitive data. They might also post false or malicious information online to harm victims' reputations or impersonate victims by creating fake profiles on social media or forums.
Indirect methods often go unnoticed initially, making them particularly insidious.
Cyberstalking: Victims and criminals
Often, cyberstalkers pursue their victims over a sustained period. An overwhelming majority of cyberstalkers are men, while victims are usually women. However, cyberstalking cases where women were the perpetrators are not unheard of. For instance, following the 2006 Megan Meier suicide case in Missouri, a female cyberstalker was indicted and convicted in 2008 of violating the Computer Fraud and Abuse Act. Occasionally, men have been victims in some cyberstalking cases.
Victims of cyberstalking could be individuals -- mature adults, young adults and children are all susceptible -- or groups, organizations or even governments. According to the FBI, children and adults are particularly vulnerable to one particular type of cyberstalking: sextortion.
This is when stalkers threaten a victim with the release of private or sensitive information unless the latter can meet the former's demands for sexual favors, nude photos, etc.
Consequences of cyberstalking
As part of a cyberstalking campaign, victims might endure a range of harassment, from nuisance-level annoyances to severe psychological and physical threats.
- Psychological effects: Victims might experience anxiety, depression, paranoia or even post-traumatic stress disorder (PTSD).
- Physical health issues: Stress from cyberstalking can lead to headaches, insomnia, ulcers or other stress-related ailments.
- Career and reputation damage: False accusations or public doxing can harm victims' professional and social lives.
- Financial losses: Ransomware attacks or identity theft can lead to significant financial burdens.
In extreme cases, victims might feel hopeless, leading to thoughts of self-harm or suicide.
Is cyberstalking a crime?
Cyberstalking is a crime is many countries, including the United States. However, legislation varies widely:
- United States: Federal law under the Violence Against Women Act and individual state laws address cyberstalking. Penalties include fines and imprisonment.
- United Kingdom: Covered under the Protection from Harassment Act 1997 and the Malicious Communications Act 1988.
- European Union: The practice of doxing violates Article 8 of the European Convention on Human Rights.
- Other Countries: Nations like Australia, Canada, India and Singapore have established anti-cyberstalking laws to protect citizens.
Despite existing laws, enforcement can be challenging due to the anonymity of perpetrators and jurisdictional issues in cross-border cases.
How to guard against cyberstalking
Individuals can guard against cyberstalking without losing their online independence. One strategy is to stay as anonymous as possible. Of course, complete anonymity is almost impossible on the internet nowadays, so the next best thing is to keep a low profile, especially on social media.
Rather than having an identifiable and traceable online presence, use nicknames and/or gender-neutral names when possible. Avoid posting personal details, such as your email address, home address, phone number or workplace details, online, where anyone can easily access them and use them to cyberstalk. Also, guard photographs, and make sure all private information, like vacation plans, photos and posts, are visible only to trusted individuals.
Use a primary email account only for communicating with known/trusted people and set up an anonymous email account for all other communications. Install email spam filters to minimize spam and the possibility of email-based phishing or cyberstalking attacks.
Other ways to guard against cyberstalking include the following:
- Update all software to prevent information leaks.
- Mask your Internet Protocol address with a virtual private network, i.e., VPN.
- Strengthen privacy settings on social media.
- Strengthen all devices with strong passwords or, better, use multifactor authentication.
- Avoid using public Wi-Fi networks.
- Send private information via private messages, not by posting on public forums.
- Safeguard mobile devices by using password protection and never leave devices unattended.
- Disable geolocation settings on devices;
- Install antivirus software on devices to detect malicious software.
- Always log out of all accounts at the end of a session.
- Beware of installing apps that ask to access your personal information.

What to do if cyberstalked
Should an individual become the victim of a cyberstalker, it's important to take immediate action.
The most effective course of action is to report the offender to the internet service provider (ISP). Should that option be ineffective, a cyberstalker's victim should change their ISP and all online names.
Block the person, even if these messages are not yet threatening. Also, report them to the platform, especially if they're harassing, stalking or threatening. Most social media platforms make it easy to report abusive behavior. These include Facebook, X (formrly known as Twitter) and LinkedIn.
If the stalking has become threatening or frightening, save evidence and contact law enforcement. Also, minimize the amount of information that's available online and/or increase the amount of fake decoy information about you to mislead cyberstalkers.
Learn about the common types of cyberattacks and how to prevent them.





