security token
What is a security token?
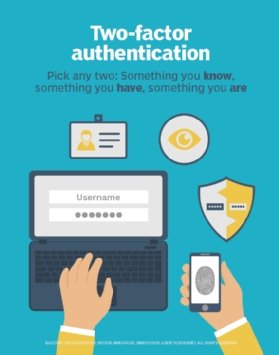
A security token is a physical or wireless device that provides two-factor authentication (2FA) for users to prove their identity in a login process. It is typically used as a form of identification for physical access or as a method of computer system access.
A token can be an item or a card that displays or contains security information about a user and can be verified by the system. Security tokens can be used in place of, or in addition to, traditional passwords. They are commonly used to access computer networks but also can secure physical access to buildings and act as electronic signatures for documents.
How do security tokens work?
A security token provides authentication for accessing a system through any device that generates a password. This could be a smart card, USB key, mobile device or radio frequency identification card. The device generates a new password every time it's used, so a security token can be used to log in to a computer or virtual private network by typing the password the token generates into the prompt.
Security token technology is based on the use of a device that generates a random number, encrypts it and sends it to a server with user authentication information. The server then sends back an encrypted response that can only be decrypted by the device. The device is reused for every authentication, so the server doesn't have to store username or password information, making the system less vulnerable to hacking.
Types of security tokens
Multiple types of security tokens are used to secure a variety of assets and applications. These include the following:
- One-time passwords (OTPs). A form of digital security token, OTPs are valid for only one login session and can't be used again. After the initial use, the authentication server is notified that the OTP shouldn't be reused. OTPs are typically generated using a cryptographic algorithm from a shared secret key composed of two unique and random data elements. One element is a random session identifier, and the other is a secret key.
- Disconnected tokens. This is a form of digital security token that doesn't connect physically or logically to a computer. The device may generate an OTP or other credentials. A desktop application that sends a text message to a cellphone, which the user must input in the login, is using a disconnected token.
- Connected tokens. A connected token is a physical object that connects directly to a computer or sensor. The device reads the connected token and grants or denies access. YubiKey is an example of a connected token.
- Contactless tokens. Contactless tokens form a logical connection with a computer without requiring a physical connection. These tokens connect to the system wirelessly and grant or deny access through that connection. For example, Bluetooth is often used as a method for establishing a connection with a contactless token.
- Single sign-on (SSO) software tokens. SSO software tokens store digital information, such as a username or password. They enable people who use multiple computer systems and multiple network services to log in to each system without having to remember multiple usernames and passwords.
- Programmable tokens. A programmable security token repeatedly generates a unique code valid for a specified time frame, often 30 seconds, to provide user access. For example, AWS Security Token Service is an application that generates 2FA codes required for IT administrators to access some AWS cloud resources.
- Smart cards. Commonly used for many secure transactions, smart cards look like a traditional plastic credit card but have an embedded computer chip that acts as a security token. Some cards also have a magnetic strip that can slide through a reader. They can be part of a 2FA scheme in which the user inserts the card into a physical card reader that establishes a secure connection and then enters a password to validate the connection. Smart cards can also be used in multifactor authentication schemes. The smart card and user password are supplemented by another factor, such as biometrics, where a fingerprint or retina scan is used for added security.
Security token advantages
Passwords and user IDs are still the most widely used form of authentication. However, security tokens are a more secure option for protecting networks and digital systems. The trouble with passwords and user IDs is that they aren't always secure. Threat actors continue to refine methods and tools for password cracking, making passwords vulnerable. Password data can also be accessed or stolen in a data breach. In addition, passwords are often easy to guess, usually because they are based on easily discoverable personal information.
Security tokens, on the other hand, use a physical or digital identifier unique to the user. Most forms are relatively easy to use and convenient. Smart cards provide greater security as the embedded chip can be programmed to invalidate itself if damaged.
Security token vulnerabilities
While security tokens offer a variety of advantages to users and organizations, they can introduce disadvantages as well. The main problem with physical security tokens is they are subject to loss and theft.
For example, a security token could be lost while traveling or stolen by an unauthorized party. If a security token is lost, stolen or damaged, it must be deactivated and replaced. In the meantime, an unauthorized user in possession of the token may be able to access privileged information and systems. This is also true of smart cards.
Security token best practices
Take the following steps to ensure that security tokens are effective:
- Begin due diligence by defining how the tokens are used and what level of functionality is needed.
- Check out security token offerings from selected providers, and try devices out before making a decision.
- The devices should be compatible with an existing security ecosystem, whether it is centralized or decentralized.
- Perform testing before rolling out the tokens.
How tokens work in cryptocurrency
Tokens play an important role in the functioning of cryptocurrencies and the blockchain technology they're built on. In the crypto world, tokens are digital assets that represent a certain value or utility. They are created and distributed through initial coin offerings, which are similar to initial public offerings in traditional financial markets. The creation of tokens is based on smart contracts, which are self-executing contracts with predefined rules.
Tokens serve various purposes within a cryptocurrency ecosystem. They can be used as a means of exchange or as a store of value. Investors may hold tokens, hoping that their value increases over time.
Tokens also have utility within a specific blockchain network. For example, in decentralized applications built on platforms like Ethereum, tokens let users access and utilize specific features and services. These utility tokens grant users certain privileges or rights within the ecosystem, such as voting on governance issues or receiving discounts on platform fees.
Learn more about the various ways to authenticate users and the protocols behind the authentication methods.







