supercookie
What is a supercookie?
A supercookie is a type of tracking cookie inserted into an HTTP header to collect data about a user's internet browsing history and habits. Also known as a unique identifier header (UIDH), a supercookie isn't technically an HTTP cookie, but rather information injected into packets sent from a user's device and the service it is connected to.
A supercookie is a data file containing information about a user's browsing behaviors, history and preferences. Supercookies can be used to collect a wide array of data on users' personal internet browsing habits, including websites visited and times of those visits. It does not matter which web browser is being used or if users switch browsers, which is why supercookies are usually "cross-site" tracking cookies.
Supercookies can also access information collected by traditional tracking cookies, including login information, cached images and files, and browser plug-in data, and store that information even after the traditional cookie has been deleted. Each supercookie can get as large as 100 KB or more.
Also, supercookies are often hidden in the browser cache which users can clear to remove supercookies. However, in doing so, they also lose the benefits of caching data, such as faster browsing, less bandwidth use and improved browsing experiences.
In 2014, Verizon Wireless added supercookies to all of its mobile users as part of its advertising programs, a move that was strongly opposed by privacy advocates such as the Electronic Frontier Foundation (EFF) for all the reasons cited above.
Cookies and supercookies
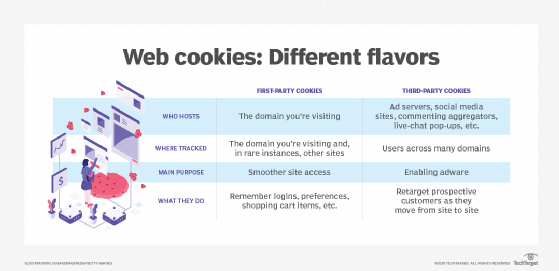
Browser cookies are usually harmless data files downloaded onto a user's computer when the user visits a website. Cookies carry information about the user that can help improve their web browsing experience during future visits to that website.
Supercookies are similar to regular cookies in one way. Both contain information such as browsing history and ad targeting data that allow trackers to understand which websites a user visited and when. But here's where the similarity ends.
For one, supercookies are often not harmless like regular cookies but rather pseudo-malicious. They are often secretly inserted by internet service providers (ISPs), professional tracking companies and technology companies to track user's online behaviors. In doing so, they gain a greater understanding of users and their interests and online habits, which allows them to create more targeted ads and personalized content. On the malicious side, they often also infringe on users' privacy because users don't know that they are being tracked and observed.
Also, supercookies are permanently stored on the user's computer. Users cannot remove supercookies by simply deleting the cache of the web browser. The extra header inserted into the packets after they leave the user's computer or mobile device prevents such easy deletions.
Supercookies and flash cookies
Flash cookies are the most common type of supercookies, and are associated with the use of the Adobe Flash browser plug-in. Also known as local shared objects (LSOs), flash cookies store information about flash objects like videos or games to improve user experiences. If these cookies happen to be malicious, they may be able to collect and report a user's data without their knowledge or explicit consent.
These cookies are stored outside the web browser so they are accessible by all browsers. Often, they are stored on the user's local storage device, so they are harder to remove using normal cookie removal methods like cache clearing. Therefore, simply switching browsers doesn't protect users from the cookie's potentially malicious tracking capabilities.
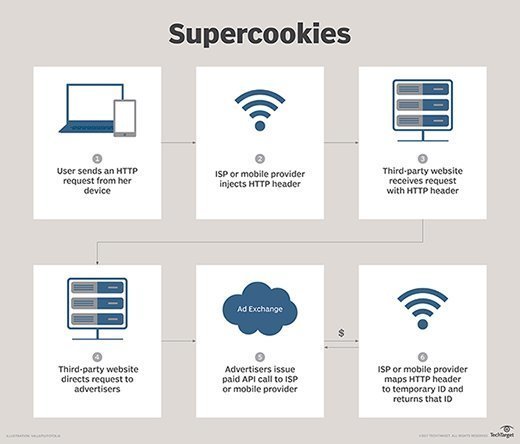
Supercookies inserted by ISPs
The supercookies inserted by ISPs are both insidious and hard to remove. When the ISP detects a user's HTTP traffic, it inserts an extra HTTP header into the packets after they leave the user's computer or mobile device. This supercookie constitutes the ISP's tracking file for each user and is stored on the ISP's servers.
ISP supercookies are associated with the devices used by a user to connect to the web. These files include the device browsing information and a UIDH that allow the ISP to recognize the device and track its (and the user's) online activities. Users cannot delete ISP supercookies since they are not stored locally on the device. Browser cookie deletion tools and antivirus software also cannot always root out ISP supercookies.
Protection from supercookies
Ad-blocking software is often ineffective against supercookies. That said, users can protect themselves from supercookie tracking by using encrypted connections over HTTPS or a virtual private network (VPN).
Flash supercookies can be removed from the Adobe Flash Player Settings Manager page. Adobe also provides a Global Storage Settings Panel, which allows users to prevent new supercookies from being written and added to their browser. In addition, dedicated utilities are available to clean existing flash cookies, although preventing new cookies from getting installed can be a more difficult task.
Some browsers and tech companies have also stepped up efforts to protect users from supercookies. For example, Firefox maintains separate "cookie jars" or caches for every website a user visits. Cookies from one site are locked up in its cookie jar and not shared across sites, minimizing the user's privacy and tracking risks. Similarly, Apple and Google have strengthened controls in iOS and Android OS devices to eliminate the risks of LSOs.
Compare web browser privacy and security features and find out about injection attacks and other web application vulnerabilities and how to avoid them. Learn about five common browser attacks and how to prevent them.






