What is a third-party cookie?
A third-party cookie is a cookie that's placed on a user's device -- computer, cellphone or tablet -- by a website from a domain other than the one the user is visiting. Third-party cookies are also known as trackers or cross-site cookies.
Third-party cookies are most frequently used for online advertising. These cookies track a user's browsing history and activities so they can present them with personalized ads for products and services. These ads are more likely to garner conversions compared to generic spray-and-pray ads.
For example, if a user searches for party décor, their screen might pop up with party décor ads on multiple websites, especially social media websites such as Facebook. The user is now seeing these ads because their web browser stored a third-party cookie and is using this information to send them targeted ads.
With the exception of Google Chrome, browsers such as Apple's Safari and Mozilla's Firefox block third-party cookies by default.
First-party cookies vs. third-party cookies
In general, a cookie is a small file of information generated by a web server and sent to a user's web browser. It typically stores user-specific data, such as their web surfing habits, personalization preferences and tracking information. Cookies are also referred to as HTTP cookies, web cookies, and browser cookies.
Both first-party and third-party cookies are text files made up of bits of information that websites use to collect user data. The main difference between these two types of cookies is who uses that cookie data and for whom the cookie collects data.
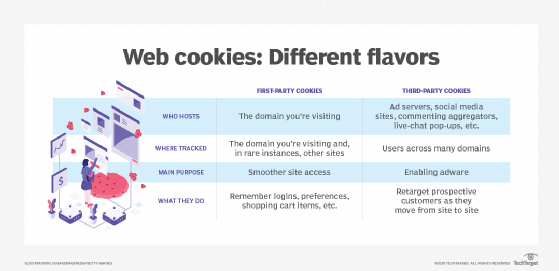
First-party cookies. The website owner places a first-party cookie on a website to collect user data that they can then use to do the following:
- Improve user experience by remembering user preferences and settings.
- Store information, such as items a user has added to their online retail shopping cart, and then use that data to remind the user to complete the purchase and not abandon the cart.
- Remember user information, like usernames, passwords and language preferences.
- Provide add-on services, such as live chat.
Third-party cookies. A third-party cookie is placed on a website by someone other than the owner -- a third party -- to collect user data for the third party. As with standard cookies, third-party cookies are placed so that a site can remember something about the user. Third-party cookies are often set by advertising networks that a website might subscribe to in the hopes of driving up sales or page views. Unlike first-party cookies, which only gather user data when users interact with the owner's website, third-party cookies track users across several websites, providing a more comprehensive picture of user behavior.
Example
If a user visits a website named news.com, a cookie placed on this domain by news.com is a first-party cookie. A cookie placed by any other site, such as an advertiser or social media site, is a third-party cookie.
Why third-party cookies are used and who uses them
Third-party cookies are so named because they come from a website other than the one a user is currently on. It's important to note that the third party might or might not own the website the user is on. However, the term doesn't make this clear, so another term -- cross-site cookie -- is also used to eliminate any confusion.
Advertisers, digital marketers and social networks often use third-party cookies to track users and understand user intent and preferences across domains and monitor their online activities. This is useful for advertisers because specific user data can enhance their success at target marketing. These parties rely heavily on the user data to inform the content they curate and generate.
By creating user profiles from user data, advertisers tweak the way they create and present information to users, ensuring that their advertisement pop-ups or social media feeds are relevant to each user.
Third-party cookies are also used in affiliate marketing and to enable single sign-on (SSO) on related sites for users. Another common use is to collect user analytics across multiple sites and then leverage those insights to guide decision-making in digital marketing.
Use of third-party cookies
Example 1: Targeted advertising
Say, a user searches for the term "party décor" on Google. Their screen might pop up with party décor ads on multiple websites, especially social media sites, like Facebook. The user will see these ads because their web browser stored a third-party cookie and is using this information to send them targeted ads.
Or, they might browse a yoga website looking for some information about asanas to lose weight. When they move on to YouTube, they might see ads for a paid yoga course, a free yoga masterclass or imported yoga mats, even though they didn't search for these terms on YouTube.
Example 2: Affiliate marketing
A user is on Website A which has a link to a Website B. Website B is an affiliate partner of Website A. The user follows the link to Website B from Website A and sees a banner ad that specifies a discount if they purchase Product P from Website B. Once they complete the purchase, Website A, who is the referrer receives a commission from Website B.
Example 3: SSO
Websites (or domains) A, B, C, and D all belong to one company. The company has embedded a sign-in widget that shares a cookie across all these sites to enable SSO for users. Thus, when a user signs into Website A, the widget and cookie ensure that they are automatically signed into Websites B, C, D without having to sign in again to each site individually.
How third-party cookies work
Third-party cookies embed JavaScript from one website into another website. A website hosts the third-party cookie by incorporating third-party JavaScript. HTTP, the protocol that's used for web browsing, is a stateless protocol, meaning information isn't saved in between browsing sessions. However, cookies remember stateful information -- or information that's saved between sessions -- in the stateless HTTP environment.
When creating a cookie, cookie attributes are specified in the HTTP response header that determines whether the cookie is a first- or third-party one. The SameSite attribute lets the creator of the cookie determine whether the cookie becomes a third-party cookie or a first-party (same-site) cookie. Browsers also use the SameSite attribute to determine how to handle the different cookie types. When a user makes a request to the browser or performs any action on the site, the cookie attributes and scenario determine if and when cookies are sent along with the response.
Example
If a website requests an image from the same site domain, the cookie with the SameSite attribute records user information. But if it requests an image from a third-party site (different domain name), a cookie with the SameSite attribute determines that the cookie will be first-party and it won't collect user information across sites.
Within SameSite, there are these descriptors:
- If the cookie creator sets SameSite to "Strict," the cookie is strictly first-party and won't ever be sent on cross-site requests. It's activated when the domains of both parties in the exchange come from the same web domain. This setting works well for remembering user preferences on the site but won't work for a request coming from an external link. For example, if the user clicks on a site link in an email from a friend, the cookie won't be sent because the user is coming from a different domain.
- If the cookie is set to "Lax," it will be sent on certain cross-site requests. Lax means the cookie is sent with secure, top-level navigation, which means the URL does change. Lax doesn't allow third-party sites to POST, or load, information on the original user site. This means that a third-party cookie set to Lax can be sent when a user clicks a link to the cookie's site but can't load advertisements from another site in an inline frame (iframe), for example, as this uses the HTTP command POST, which is considered less secure.
- If no specification is made, all requests are subject to cookies, and the cookie is by definition a third-party cookie. It doesn't restrict POST requests, which advertisers, social networks and other third parties can use to load information from their site. This lack of specification makes cookies useful for advertisers because they often use methods that don't fit the criteria of "SameSite = Strict" and "SameSite = Lax." For example, an external site makes a GET request that doesn't change the URL as a top-level navigation. This action -- which could be an <iframe> or <img> request -- is blocked by both Lax and Strict. Having no specification allows that type of communication, in which a page is loaded inside another page. This is a common way for advertisements to appear on web pages.
How to tell a website uses third-party cookies in Mozilla Firefox, Google Chrome and Microsoft Edge
Here's how to determine which websites are using third-party cookies:
1. Firefox
- Click the Firefox menu button in the top right (three vertically stacked lines) and select Settings.
- Select the Privacy & Security panel.
- Scroll down to the Cookies and Site Data section.
- Click Manage Exceptions.
- The Exceptions - Cookies and Site Data dialog box will open.
- It will show if you have blocked any sites from storing cookies.
- To unblock any sites, click Remove Website.
- To save any changes, close the Settings page.
2. Chrome
- Open Chrome.
- At the top right, click on the Chrome overflow menu (three vertical dots) and then Settings.
- Click on Privacy and Security > Third-party cookies.
- Scroll down to the section on Sites allowed to use third-party cookies.
- If you see No sites added, it means that all sites will be able to create or store third-party cookies.
3. Edge
- Open a browser in Edge.
- At the top right, select Settings and more (three horizontal dots).
- Select Settings > Cookies and site preferences.
- Select Manage and delete cookies and site data > See all cookies and site data.
How to enable or disable (block) third-party cookies in Mozilla Firefox, Google Chrome, and Microsoft Edge
Blocking third-party cookies usually doesn't create login issues on websites, which can be an issue after blocking first-party cookies. Rather, it usually results in the user seeing fewer targeted ads on third-party sites. But blocking all cookies can sometimes lead to problems, as some websites rely on first-party cookies to function properly.
Here's how to check for or block third-party cookies:
1. Firefox
- Click the menu button in the top right (three vertically stacked lines) and select Settings.
- Select the Privacy & Security panel.
- If the Standard radio button is selected, all cookies, including third-party cookies are allowed.
- If Strict is selected, third-party cookies are blocked. To enable these cookies, select Standard or Custom.
- If Custom is selected, uncheck Cookies to allow all cookies, including third-party cookies.
- To apply the new setting, select the Reload All Tabs button.
2. Chrome
- Open Chrome.

- At the top right, click on the Chrome overflow menu (three vertical dots) and then Settings.
- Click on Privacy and Security and then Third-party cookies.
- If the Allow third-party cookies radio button is selected, the cookies are enabled and sites can use them to see user browsing activity or to improve the user browsing experience.
- To disable third-party cookies, select Block third-party cookies. In this case, no third-party site will be able to use third-party cookies to see user browsing activity.
- Another option is to selectively block third-party cookies only in Chrome's Incognito mode. In this case, sites will be unable to see user browsing activity across sites (including related sites) or to use user activity information to show personalized ads.
3. Edge
- Open a browser in Edge.
- At the top right, select Settings and more.
- Select Settings and then Cookies and site preferences.
- Select Manage and delete cookies and site data
- Enable the toggle Allow sites to save and read cookie data.
- This setting will allow all cookies, including third-party cookies.
- To allow cookies (including third-party cookies) from specific sites, after selecting Manage and delete cookies and site data:
-
-
- Navigate to the Allow section
- Select Add to allow cookies for a specific site by entering its URL.
-
- To block third-party cookies, after selecting Manage and delete cookies and site data, enable Block third-party cookies.
- To block all cookies (including third-party cookies) from specific sites, after selecting Manage and delete cookies and site data:
-
-
- Navigate to the Block section
- Select Add to block cookies for a specific site by entering its URL.
-
Third-party cookies and risks to data privacy and cybersecurity
Third-party cookies and cookies in general pose a significant data security risk and are viewed as infringing on user privacy rights. This is because cookies enable site owners to build up detailed user profiles that may include users' personal information such as their gender, religion or sexuality.
This information can potentially be used to invade user privacy or spread misinformation. Threat actors who get access to this information might use it to blackmail individuals, steal their identities or perpetrate fraud against them. They might also sell the information on the dark web to other bad actors who might use the data for malicious or nefarious purposes.
Authentication-related cookies normally include a security flag that instructs the browser to only access the cookie using secure channels, such as Secure Sockets Layer or Transport Layer Security. However, malicious actors can hijack and use these cookies to gain user information if they are not transmitted securely.
For example, in 2020, researchers at cybersecurity firm Kaspersky discovered two cookie-stealing malware modifications in Android that allow hackers to control their victims' social media accounts and use them for malicious purposes. These cookies include unique session IDs that are used to identify users and allow them to log into websites in the future without having to provide their credentials multiple times.
Some other common attacks that might also involve the misuse of cookies are the following:
- Cross-site request forgery.
- Cross-site scripting.
- Session hijacking.
What's happening to third-party cookies?
There has been a general move away from third-party cookies as consumers increasingly demand online privacy and express concerns about the risk of their personal data being mishandled or misused by third parties. Currently, many users are turning to ad blockers and private browsing to prevent third-party cookies from collecting their data.
National regulators have realized the risks of third-party cookies and are taking steps to restrict them. For example, the European Union (EU) passed the Cookie Law, which was adopted by all EU countries in May 2011. It requires websites to get consent from visitors before storing any information to or retrieving information from the visitor's device, whether it is a computer, smartphone, or tablet.
Other privacy regulations also limit the ability of companies to collect and use personal data, including the General Data Protection Regulation (GDPR) and California Consumer Privacy Act (CCPA). These laws make third-party cookies -- that do collect personal data -- unnecessary and their use can cause legal repercussions for digital marketers and advertisers.
While blocking third-party cookies increases user privacy and security, it does create problems for consumer tracking and ad-serving firms, which often place ads that follow users around the web.
The birth of cookies three decades ago launched a $600 billion digital advertising industry. But today, tech companies recognize their risks and are now paying heed to consumers and have pledged to stop supporting them. For example, several browsers now block third-party cookies by default, including Firefox, Chrome and Safari.
In February 2020, Google first revealed its intentions to gradually phase out third-party cookies on Chrome by 2022. The tech giant later postponed this plan to 2024, primarily because it wanted advertisers to have more time to change their advertising tactics and test out new, less-intrusive targeted advertising technology. In April 2024, Google once again postponed the phase-out plan to 2025.
A couple of months later, in July 2024, Google announced it would cancel plans to kill third-party cookies in its browser.
What are some alternatives to third-party cookies?
For years, marketing and customer experience companies have used third-party cookies to follow users and refine their targeting and marketing strategies. To minimize the impact of the phase-out, many are using other alternative techniques such as:
Browser fingerprinting. A browser fingerprint is a collection of details about the user, such as their browser, the contents of the browser cache, location and time zone. It collects this information in a hash value, which the information collector can use to accurately follow users around the web.
Identity solutions. Identification options track website visitors by gathering personal information, such as email addresses, phone numbers or login IDs, which is then provided to an ID provider. The user information is then encrypted or hashed to preserve their privacy before matching to an existing ID or creating a new ID. An ID formed with a persistent user identification, such as an email address, is referred to as a universal identifier because it can be used on various websites, channels and platforms.
Google Topics. In 2019, Google launched the Privacy Sandbox initiative to fulfill rising consumer expectations for more privacy. When it was first introduced, it focused on the Federated Learning of Cohorts (FLoC) algorithm, with the intention of creating groups of users with similar surfing preferences that could be shared with advertisers while preserving individual users' anonymity. Nonetheless, FLoC exploitation methods, such as reverse engineering, quickly emerged, which could allow trackers to create unique digital fingerprints of individual users. FLoC was finally transformed into Google Topics, which also uses the Chrome browser. Google Topics tracks a user's weekly usage to identify a select few topics that best reflect their top interests over the course of three weeks.

Contextual advertising. This refers to online ads that target users depending on the content of the websites they visit. Users don't give up any privacy when navigating between websites because only ads that are pertinent to their interests are aimed at them. For instance, if a user was previously browsing a sports website and then clicked on a clothing website, they would only see sports-related ads on the sports page.
Walled gardens. A walled garden is a closed environment where businesses are permitted to gather and use user data. Google, Facebook and Amazon are common examples. Walled gardens are constructed based on logged-in users, letting them track each individual across devices. Also, they use a first-party platform, so third-party cookies aren't required. Businesses can keep a high level of confidence in the identification and conduct of users by managing the data that goes into and out of their ecosystem.
Many marketing and sales operations depend on third-party cookies, whereas first-party cookies are used to gauge user engagement. Learn what makes the two types of cookies different from one another.