
creative soul - Fotolia
Security awareness training best practices for MSPs
Human error is the root of many IT security catastrophes. Use these security awareness best practices to craft programs that users will actually learn from.
Most breaches, and even ransomware, begin with a simple email. We all know this. But how do we get users to change the risky behaviors they take part in with their technology?
Whether it's clicking on emails, installing random apps on their phones or simply giving out information freely, users are a major threat to any organization. Obviously, we can't get rid of the users, so we must train them. Establishing a security awareness training journey is a great place to start.
Begin with a security policy
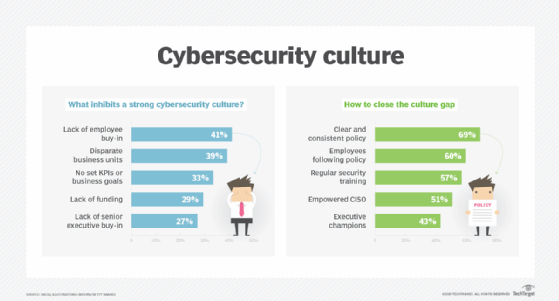
Your users' educational journey should start with an IT security policy. This policy will tell users what the expectations are for their behavior and how they use tech. It will also outline how users will be continually trained. Additionally, the policy will tell users that you are making security a priority.
Train the users on the policy itself and have them sign it. Any organization faces real risks of data loss, breaches and ransomware, which all have costs associated with them. Be sure your IT policy states what can happen to your employees if they are not following the policy as per your local, state or federal laws and regulations.
 Dawn R. Sizer
Dawn R. Sizer
Provide a baseline user education
All employees should then receive a baseline course delivered online. The course should cover the basics, such as how to do the following:
- avoid phishing emails and other types of social engineering cyberattacks;
- spot potential malware behaviors;
- report possible security threats;
- follow company IT policies and best practices; and
- adhere to any applicable data privacy and compliance regulations.
That may seem like a lot, but remember: Security awareness isn't once and done; it's continual.
When users complete the initial course, begin testing them on a recurring basis. Send emails designed to fool the user at first glance, delivered a few times a month at random intervals on various and trending topics. They will need to use the skills they learned or else they will be fooled. If they are fooled, be sure to follow up with remedial training based on the type of phishing email sent.
Deliver additional training and testing
In addition to the phishing emails, your security awareness training best practices should include further training. You will want to cover topics that include the following:
- Scams
- Malware
- Password security/multifactor authentication
- Removeable devices
- Safe surfing
- Social networking and catfishing
- Physical security
- Clean desk
- Data management
- BYOD
Test users on those topics, as well. When it becomes second nature to a user, the risky behaviors drop off. A mature security posture doesn't mean you should end the training, however. Your training and testing should evolve along with the different types of threats. Make the training harder as your users get smarter.
Whatever product you use for security awareness training, make sure it can report on the users. You will want to track the users who fail topics repeatedly, as well as the ones who do well. Retrain the ones who do poorly. Some may need in-person training to readily understand what they are doing wrong. Reward your users who do well with positive reinforcement, such as with badges or certificates.
Don't let your training stagnate. Change up the testing and training now and then with tips and tricks to help them in their jobs, a fun training on something unrelated to security or a reward. Gamification works well in the workplace. Friendly competition adds incentive to do well and learn, and it can lead to an overall reduction in risk for an organization.
Different employee roles, different training
Lastly, as you craft a security awareness training journey, take into consideration your users' different roles. You will want at least three levels of training.
- General training path for all users to follow that covers the topics already mentioned.
- Decision-maker training for those who have increased access to information and technologies.
- Specialized roles and C-suites to prevent whaling and getting the keys to the kingdom.
Your security awareness training best practices should start with an IT security policy and never stop evolving. The training program should address a wide range of topics and employees from the CEO down and report on the success or failure of each user. It should also offer remedial training and gamification to add incentive to the employee to participate and do well. Whatever journey you take the user on, be sure it can be fun, as well as educational.
About the author
Dawn R. Sizer is CEO of 3rd Element Consulting Inc., a managed service provider based in Mechanicsburg, Pa. Sizer is also a member of The ASCII Group, a North American IT community for MSPs, solution providers and systems integrators.







