Top 15 email security best practices for 2025
Attackers exploit email every day to break into corporate networks, but the risk can be reduced by adhering to these 15 email security best practices.
Email security best practices haven't changed much over the years: Use strong passwords, block spammers, don't trust offers that are too good to be true and verify requests even from trusted entities.
These longstanding practices, however, have not stopped email from being a significant security vulnerability.
To contain the risks, organizations must follow a stronger set of email security best practices. They can be summarized as follows:
- Train employees on email best practices.
- Create strong passwords.
- Don't reuse passwords across accounts.
- Consider changing passwords regularly -- or not.
- Use MFA.
- Take phishing seriously.
- Be wary of email attachments.
- Don't click email links.
- Don't use business email for personal use and vice versa.
- Only use corporate email on approved devices.
- Encrypt email, communications and attachments.
- Avoid public Wi-Fi.
- Use email security protocols.
- Use email security tools.
- Log out.
Let's explore each best practice in further detail.
1. Train employees on email security best practices
Regularly scheduled security awareness trainings inform employees about security best practices and keep users up to date with not only corporate security policies and their role in keeping their organizations secure, but also threats they might encounter. Be sure to discuss email during security awareness trainings and explain the company's email security policy, common email security threats and recommended email security best practices.
2. Create strong passwords
One of the most important email security best practices is to use strong passwords. Password security advice has changed in recent years, however. Previous thinking was that complex equaled strong. But forcing employees to create complex passwords, such as }m}{4p#P@R9w, usually ends with users writing their passwords on a sticky note or saving them in an insecure file on their desktops.
Current NIST recommendations maintain that password length, not complexity, is the key to password strength. Passphrases -- the stringing together of a few words, such as kittEnsarEadorablE -- are one method to make longer, easy-to-remember yet difficult-to-guess passwords that help defend against attackers who use dictionary attacks to target weak passwords.
If you plug these two examples into Security.org's How Secure Is My Password? tool, you will find that }m}{4p#P@R9w would take 400,000 years for a computer to crack, while kittEnsarEadorablE would take 6 trillion years. Stronger passphrases include a string of unrelated words. For example, per Security.org's calculator, the passphrase kittEnsmErryvisitortrEE would take 2 sextillion years for a computer to guess.
A company password policy should be created to communicate password requirements and expectations.
3. Don't reuse passwords across accounts
Password reuse is a major email security threat. If an attacker compromises one account that uses the same credentials as other accounts, the attacker can easily gain access to those other accounts. Attackers know that trying a reused password associated with a person's account on a breached system often unlocks other accounts. Password reuse is especially dangerous when employees use the same passwords for corporate and personal accounts.
Encourage employees to follow password hygiene best practices, such as using strong, unique passwords for each account. This is a pain point for many users, especially those with dozens or hundreds of logins to remember. Using single sign-on or a password manager can help alleviate the challenge.
4. Consider changing passwords regularly -- or not
Guidance around the frequency of password changes has been debated in recent years. Changing passwords every 90 days used to be the norm. The assumption was that frequent password changes help keep systems secure, but they often lead to user frustration and the use of less secure passwords. More often than not, Password1 will turn into Password2 after 90 days.
NIST recommends against forcing periodic password changes unless you see signs of a suspected compromise or data breach. In addition, some compliance regulations, such as PCI DSS, require frequent password changes.
Companies must weigh the benefits of regular password changes with users' tendencies to use weaker passwords that are easier to remember and therefore easier for attackers to exploit.
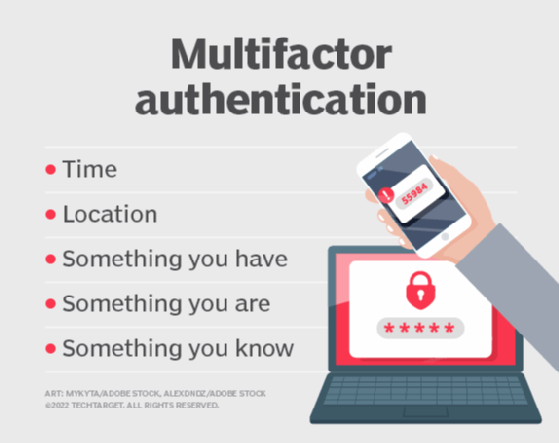
5. Use MFA
MFA involves using more than one method to authenticate a user's identity. For example, a username and password in combination with a one-time password or fingerprint biometric. Adding a second -- or third, or more -- factor to the authentication process adds an additional layer of defense and defends against common email threats, such as brute-force attacks and password cracking.
Companies should mandate the use of MFA. Employees should also protect their personal accounts by using MFA wherever available.
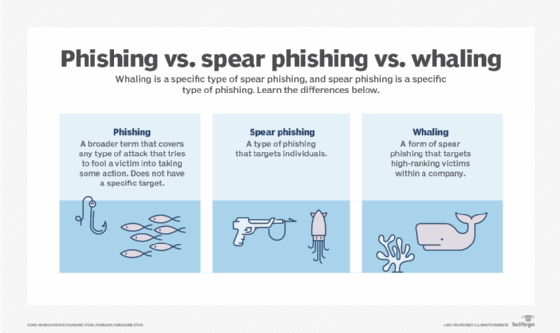
6. Take phishing seriously
While email security products prevent many spam emails from reaching a user's inbox, a good amount of spam still gets through. These unwanted messages can contain increasingly sophisticated phishing schemes, which include standard phishing emails, along with spear phishing or whaling attacks. Users should be on the lookout for phishing scams and use caution when opening any potentially malicious emails. Don't open, respond to, click links in or open attachments from emails that appear suspicious.
More and more organizations include phishing awareness training in their security awareness training programs to help employees identify problematic messages and to teach them how to avoid clicking on the wrong links or opening the wrong attachments.
7. Be wary of email attachments
Many email attacks rely on the ability to send and receive attachments that contain malicious executable code. Email security gateways and antimalware software can detect malicious sources and block most malicious attachments. These attachments, however, can also come from trusted sources that have been exploited by attackers.
Whatever the source, employees should beware of attachments even when the organization uses email-scanning and malware-blocking software. Use extra caution before opening an attachment that has an extension associated with an executable program, such as EXE (executable file), JAR (Java application file) or MSI (Windows Installer). Files such as Word documents, spreadsheets and PDFs can also carry malicious code, so be careful handling any type of attached file. Scan files with an antimalware program or avoid opening them altogether.
8. Don't click email links
Hyperlinks in emails can often connect to a web domain different from the one they appear to represent. Some links might display a recognizable domain name -- such as www.amazon.com -- but, in fact, direct the user to a different, malicious domain. Attackers also use international character sets or misspellings to create malicious domains that appear to be those of well-known brands.
Always review link contents by hovering the mouse pointer over the link to see if the actual link is different from the displayed link. Note that even this can be spoofed -- though most modern email programs should catch such links. When in doubt, type domains directly into browsers to avoid clicking links in emails.
9. Don't use business email for personal use and vice versa
While it might be tempting and convenient for employees to use a corporate email account for personal matters, an enterprise email security best practice is to prohibit this. Likewise, don't send work-related emails from personal accounts. Mixing business and personal matters can result in threats such as spear phishing. Outline acceptable email use policies and any restrictions in a corporate email policy.
10. Only use corporate email on approved devices
People can access email from practically anywhere and on any internet-connected device. While convenient for employees, this could become a security disaster for an organization. If company email is opened on devices that don't have the proper security controls, attackers could exfiltrate users' credentials, email and data. Require employees to only access email on company-approved and trusted devices.
11. Encrypt email, communications and attachments
It has been said that email is like a postcard: Every person and system that it comes in contact with can see what is written. This is why email encryption is so important. Encryption, the process of converting plaintext into ciphertext, ensures that anyone who intercepts the email cannot read its contents. This helps prevent many email security issues, such as man-in-the-middle and business email compromise attacks. Most major email services have encryption capabilities.
Encrypting the message isn't enough, however. Also encrypt communications between the organization and the email provider. Encrypt attachments as well, even if the email they are attached to is encrypted.
12. Avoid public Wi-Fi
Employees might see public Wi-Fi as a blessing, but they should be reminded that these connections are ripe for attacks. If employees log into corporate email on public Wi-Fi, anyone on that network could also access their email. Malicious actors can use open source packet sniffers, such as Wireshark, to monitor and gain access to personal information via email. Even if users don't actively check email on public Wi-Fi, almost every system is set to automatically update inboxes when a device connects to a network. If users are on Wi-Fi, then so is their email, putting account credentials at risk.
Only use secure, known Wi-Fi networks to check email.
13. Use email security protocols
The following three email security standards are key to filtering spam messages:
- DomainKeys Identified Mail. The DKIM standard uses asymmetric cryptography to prevent email spoofing. A digital signature added to an email verifies the message was not altered after it was sent. If the signature doesn't match the email domain's public key, it is blocked. If it does match, it is delivered.
- Sender Policy Framework. SPF verifies an email came from its source and is authorized to send an email from that domain. If verified, the email gets delivered. If not, the email is blocked.
- Domain-based Message Authentication, Reporting and Conformance. The DMARC protocol extends DKIM and SPF. Using DMARC, domain owners can publish their DKIM and SPF requirements, as well as specify what happens when an email fails to meet those requirements, such as reporting back to the sending domain.
While these technical controls prevent spoofed emails, they do not stop all unwanted messages.
14. Use email security tools
Beyond implementing the proper protocols, email security strategies should include multiple tools that help maintain email security. Antimalware, antispam, antivirus, email filtering, email security gateways, email monitoring systems, firewalls and endpoint protection should be considered.
15. Log out
Leaving email open on devices that are accessible to others is a security risk. Urge employees to log out of their email when it's not in use and when they have finished work for the day.
Editor's note: This article was updated in January 2025 to reflect changes in cybersecurity and email best practices.
Sharon Shea is executive editor of TechTarget Security.
Peter Loshin is a former TechTarget senior technology editor.







