What are IoT devices?
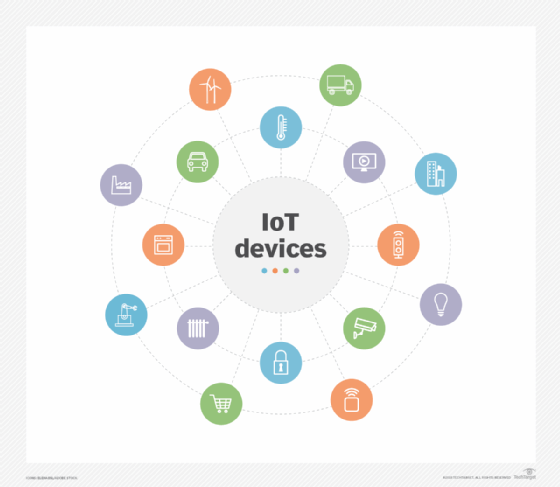
Internet of things (IoT) devices are nonstandard computing hardware -- such as sensors, actuators or appliances -- that connect to a wired or wireless network to transmit data.
IoT extends internet connectivity beyond desktop computers, laptops, smartphones, tablets and other typical computing devices. It lets a range of traditionally non-internet-enabled devices and everyday objects connect to networks and the cloud. Embedded with IoT technology, these devices continue to deliver their primary function, but they also can communicate and interact over the internet and be remotely monitored and controlled.
IoT devices have industrial and consumer uses, and they're typically integrated into tools such as mobile devices, industrial equipment and medical devices. They are also used in smart cities, where they send data or interact with other IoT devices over a network.
IoT and IoT devices provide real-time data for industrial or enterprise use cases. They also make daily activities faster, easier and more convenient for consumers.
Examples of IoT devices
Connected devices are part of an ecosystem in which every device talks to other related devices in the environment to automate home and industry tasks. As part of this, they transmit sensor data to users, businesses and other intended parties. The devices can be categorized into three main groups: consumer, enterprise and industrial.
Consumer-connected devices
These devices include smart TVs, smart speakers such as Google Home's Nest, toys, wearables and smart appliances. In a smart home, IoT devices are designed to sense and respond to a person's presence or physical contact with the device.
In this setup, when a person arrives home, the car communicates with the garage to open the door. Once inside, the thermostat is already adjusted to a preset temperature, and the lighting is set to a comfortable intensity and color.
Other smart home devices include sprinklers that adjust the amount of water the lawn needs based on the weather and robotic vacuum cleaners that learn which areas of the home must be cleaned most often. Smart security devices, such as front door cameras, link to a security system that might also include motion detectors, cameras and smart door locks.
Enterprise IoT devices
There is a variety of edge devices designed for businesses available. They vary in capabilities but tend to be geared toward maintaining a facility or improving operational efficiency. Some options include smart locks, smart thermostats, smart lighting and smart security. Consumer versions of these technologies are also available.
In the enterprise, smart devices can help with meetings. Smart sensors located in a conference room can help an employee locate and schedule an available meeting room, ensuring the proper room type, size and features are available.
Likewise, retailers can use radio frequency ID tags to track their goods, increasing inventory accuracy. IoT devices are also used to keep track of inventory as it moves along in the supply chain for supply chain management.
Industrial IoT devices
Factories or other industrial environments rely on industrial IoT (IIoT) devices. These are often sensors used to monitor an assembly line or other manufacturing processes. Sensor data is transmitted to monitoring applications that ensure key processes are running optimally. These same sensors can predict when parts need to be replaced, preventing unexpected downtime. Links to systems using artificial intelligence (AI) enhance IIoT devices.
If a smart sensor detects an abnormal condition, indicating a problem has occurred, the system can send a notification to service technicians informing them what's wrong and what parts they need to fix the problem. This saves the technician from coming on-site to diagnose the problem and then having to travel to a warehouse to get the part needed to fix the problem.
In the medical industry, IoT devices monitor patient health and track vital signs. If a patient needs attention, these monitors send notifications to the relevant healthcare workers.
How do IoT devices work?
IoT devices vary in terms of functionality, but they do have some similarities in how they work. First, IoT devices are physical objects designed to interact with the real world in some way. The device might be a sensor on an assembly line or an intelligent security camera. In either case, the device senses what's happening in its surrounding environment.
The devices typically include an integrated central processing unit, firmware and a network adapter. In most cases, IoT devices connect to a Dynamic Host Configuration Protocol server and acquire an Internet Protocol (IP) address that they can use to function on the network. Some IoT devices are directly accessible over the public internet, but most are designed to operate exclusively on private networks.
Although not an absolute requirement, many IoT devices are configured and managed through a software application. Some devices have integrated web servers, eliminating the need for an external application.
Once an IoT device has been configured and begins to operate, most of its traffic is outbound. A security camera, for example, streams video data; likewise, an industrial sensor streams sensor data. Some IoT devices, such as smart lights, accept inputs.
IoT gateways
Connecting IoT devices with the computing resources they need to perform their activities often requires the use of an IoT gateway. Typically used in cloud-enabled environments, an IoT gateway is a physical device or software application that provides the connection point between the cloud and IoT devices, such as the types described in this article.
IoT gateways operate like network routers, moving data between IoT devices and the cloud. They support two-way traffic: Outbound data traffic goes to the cloud, while incoming traffic might be used for various administrative tasks, such as updating firmware or patching applications.
Gateways with added intelligence can perform computing tasks in addition to routing data traffic. This is an important distinction between gateways and Wi-Fi routers. Such gateways can perform preprocessing activities at network edges before sending data to the cloud. They also can handle multiple IoT protocols.
What is IoT device management?
Several challenges can hinder the successful deployment of an IoT system and its connected devices, including security, interoperability, power and processing capabilities, scalability and availability. Many of these problems can be addressed with IoT device management, either by adopting standard protocols or using services offered by a vendor.
Device management helps companies integrate, organize, monitor and remotely manage internet-enabled devices at scale, offering features critical to maintaining the health, connectivity and security of the IoT devices along their entire lifecycles.
IoT device management contains separate categories, including onboarding devices, configuration, maintenance, diagnostics and end-of-life management.
Device management typically follows a pattern such as the following:
- Registration and activation.
- Authentication and authorization.
- Configuration.
- Provisioning.
- Monitoring and diagnostics.
- Troubleshooting.
- Firmware updates and patching.
Some examples of standardized device management protocols include the Open Mobile Alliance Device Management for remote management of mobile devices and OMA Lightweight Machine to Machine for sensor networks. IoT device management services and software are available from vendors, including Amazon, Google, IBM and Microsoft.
IoT device connectivity and networking
The networking, communication and connectivity protocols used with internet-enabled devices largely depend on the specific IoT application deployed. Just as there are many different IoT applications, there are many different connectivity and communication options, including the following:
- Constrained Application Protocol, or CoAP.
- Datagram Transport Layer Security, or DTLS.
- MQ Telemetry Transport, or MQTT.
- Data Distribution Service, or DDS.
- Advanced Message Queuing Protocol, or AMQP.
Wireless protocols include the following:
- IPv6.
- Zigbee Bluetooth Low Energy.
- Z-Wave.
Cellular, satellite, Wi-Fi and Ethernet can also be used.
Connectivity options have tradeoffs in terms of power consumption, range and bandwidth. All of these must be considered when choosing connected devices and protocols for an IoT application. These options include high range, power consumption and bandwidth; low range, power consumption and bandwidth; or high range, low power consumption and bandwidth.
In most cases, IoT devices connect to an IoT gateway or to another edge device where data can either be analyzed locally or sent to the cloud for analysis. Some devices have integrated data processing capabilities that minimize the amount of data that must be sent to the cloud or data center. This type of processing, which often uses AI and machine learning capabilities built into the device, continues to grow in popularity as IoT devices create more data.
What security risks do IoT devices pose?
The interconnection of traditionally nonintelligent devices raises several questions in relation to security and privacy. IoT technology has moved faster than the mechanisms available to safeguard devices and their users. Fortunately, advances in security technology continue to make these devices secure and resistant to cyberattacks.
The following are some IoT security risks that organizations must address:
- Increased attack surfaces.
- Unsecured hardware.
- Poor asset management.
- Shadow IoT.
- Unencrypted data transmissions.
- Domain name system threats.
- Distributed denial-of-service attacks.
- Malicious node injections.
- IoT ransomware attacks.
- Firmware exploits.
Numerous security breaches affecting IoT devices have occurred, detailed below.
CyberAv3ngers
In 2023, cyberattackers compromised Israeli-made Unitronics Vision Series programmable logic controllers and human-machine interfaces. The group, using the name CyberAv3ngers, targeted water facilities that used the Israel-developed industrial control devices to manage water pressure.
Mars Hydro and LG-LED Solutions
This large data breach was discovered in February 2025. It involved smart grow lamps and climate management systems that had more than 2 billion records in an unprotected database. Among the exposed data were Wi-Fi passwords and IP addresses.
Eleven11Bot
A botnet discovered in early 2025 exploited tens of thousands of unprotected IoT devices, such as webcams, many of which had critical vulnerabilities.
Ransomware attacks on healthcare institutions
To date, dozens of healthcare institutions across the U.S. have faced hundreds of ransomware attacks on unprotected devices, such as patient health monitoring systems. An Ohio-based hospital chain experienced a system-wide technology outage when hackers exploited unpatched patient monitoring systems.
IoT security measures worth considering include the following:
- Implement access confirmation using two-factor and multifactor authentication.
- Use role-based authentication.
- Have strong encryption for routers, such as Wi-Fi- Protected Access (WPA) 2 or WPA3.
- Harden every device.
- Encrypt data at rest and in motion.
- Segment networks, setting up a separate IoT network.
- Use strong passwords that are changed regularly.
- Patch security systems regularly.
- Sign up for automatic updates from manufacturers.
- Turn off unused features.
- Check device logs and track devices.
- Shop smart, looking for reputable brands.
- Look for devices certified by reputable security organizations.
IoT device security standards and legislation
The IoT Cybersecurity Improvement Act of 2020 directed the National Institute of Standards and Technology (NIST) to develop and publish standards and guidelines on the use and management of IoT devices.
NIST developed an IoT device security labeling process for consumers in 2022. Building on that, the Federal Communications Commission in 2023 launched the U.S Cyber Trust Mark program. It provides U.S. consumers with labeled products that meet NIST security criteria.
The following are three key standards for IoT security and design:
- ISO/IEC 30141:2024 Internet of Things -- Reference architecture. This provides IoT reference architecture for secure and scalable systems.
- ISO/IEC 21823-1:2019 Internet of things (IoT) -- Interoperability for IoT systems. This provides guidance on how IoT systems and devices connect and interoperate with one another
- NIST Special Publication 800-213. This describes how to establish cybersecurity protection for IoT devices.
Whether an organization is already using IoT devices or is considering adopting them, it should be prepared to handle the unique security challenges presented by IoT devices.
IoT device trends and anticipated growth
The latest IoT Analytics "State of IoT Summer 2024" report predicted that, by 2030, there will be more than 41 billion connected IoT devices.
Among the key growth drivers are 5G wireless technology, edge technology using AI, smart homes, wearables, IoT in healthcare and environmental protection. Important trends that will impact device growth include AI of things, smart analytics, digital twins, use of low Earth orbit satellite communications and new security regulations for IoT devices.
The key to making effective use of IoT devices is to understand how edge technology and IoT work together.
Sharon Shea contributed to this definition.






