
sdecoret - stock.adobe.com
Salesforce DNSSEC project aims to boost site security, speed, uptime
Salesforce, which juggles multiple DNS providers to serve customers while complying with global data-privacy regulations, spearheads new DNS models to enable deeper encryption.
Salesforce and domain name system provider NS1 are working together on pushing encryption deeper into DNS to foil hackers and foster data privacy compliance.
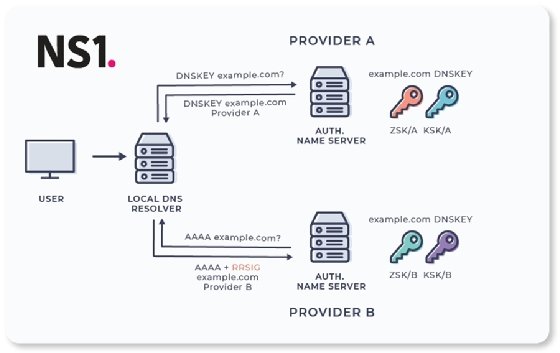
The initiative, two years in the making with a proof-of-concept implementation announced last week, breaks new ground by letting multiple DNS providers use DNS Security Extensions (DNSSEC) to add authentication to their systems when accessing Salesforce pages. The engineers collaborating on the initiative call it "multi-signer DNSSEC models."
DNSSEC is crucial because Salesforce uses multiple DNS providers globally to direct traffic to its cloud servers, said Eric Hanselman, a 451 Research analyst. Also, Salesforce needs to seal vulnerabilities from DNS hackers, who could redirect traffic or spy on cloud vendors' customers.
The DNSSEC model lets each DNS provider use separate encryption keys for the records they serve if all providers agree on the keys they're using. That enables successful validation of authenticity between DNS providers and lets large multinational cloud software vendors, like Salesforce, keep response times down.
The NS1-Salesforce DNSSEC model also enhances compliance with the EU's General Data Protection Regulation (GDPR) and more stringent country-specific laws, such as Germany's mandate that cloud companies keep customer data within its borders.
The security model was made public in a document published on the Internet Engineering Task Force (IETF) site. Any organization on the open source BIND platform can use the model
"Generally, DNSSEC has seen steady, increased adoption as tooling becomes more mature," Kerr said. "Like any security best practice, it just takes time."
Along with security, the Salesforce-NS1 project is also aimed at improving Salesforce.com uptime and response time by routing traffic more efficiently among the many different IP addresses that exist across geographical regions, Hanselman said. For example, European addresses connecting to Salesforce servers in the continent differ from addresses connecting to servers in Asia.
"The address the DNS provider gives you is going to change based on where you are, and in some cases, who you are," Hanselman said.






