ERM implementation: How to deploy a framework and program
Enterprise risk management helps organizations proactively manage risks. Here's a look at ERM frameworks that can be used and key steps for implementing a program.
All businesses must manage risks. However, their ability to do so effectively and efficiently hinges in large part on whether they have an enterprise risk management program. An ERM program is a formal strategy for tracking and managing the various types of business risks that could affect an organization.
ERM programs help ensure that organizations adopt a deliberate, systematic approach to identifying and mitigating risks across the enterprise, as opposed to attempting to address risks in a haphazard fashion. The latter approach tends to be inefficient and lead to major gaps -- and failures -- in risk management initiatives.
This article provides details on what an ERM program involves, external ERM frameworks that organizations can use as playbooks for implementing a program, and key ERM implementation steps. It also covers common challenges that chief risk officers (CROs) and other risk management leaders should be aware of upfront.
Why do organizations need an effective ERM program?
Developing an ERM program that effectively identifies, tracks and mitigates relevant risks is critical to risk management -- and business -- success. Again, all organizations face various risks. Businesses typically are subject to financial risks, such as cash flow shortfalls or missed revenue goals. They're also at risk of cybersecurity incidents and other technology-related issues. Reputational risks could reduce customer trust in their brand. And so on.
Without an ERM program, businesses typically end up attempting to manage risks reactively. It's only when something goes wrong -- when a cyberattack occurs, for example, or when a quarterly report shows an unexpected operating loss -- that business leaders take action to correct the underlying problem.
This reactive approach is bad for two key reasons. First, it means that risks often end up causing more harm than necessary when problems arise. For example, if an organization waits until after a cyberattack has occurred to identify and address the risks that led to the attack, it misses an opportunity to minimize the business impact -- or, ideally, to remediate the problems before any damage occurs.
Second, reactive risk management is usually less efficient because the organization must scramble to respond to risks as they arise. Resources can be used more effectively if risk mitigation plans are made in advance as part of an ERM program. For example, proactive risk management can help position a company to manage cybersecurity risks on its own by hiring adequate security staff. But if it waits for an attack to occur before doing so, it could end up having to hire an outside cybersecurity firm to clean up a data breach and put new security protections in place.
Well-managed ERM programs help organizations avoid such pitfalls through a forward-looking, consistent approach to risk management at the enterprise level.
Which ERM frameworks are available to use?
Businesses don't have to start from scratch when they implement an ERM program. They can use existing ERM frameworks, which define the core risk management process that organizations should deploy. The frameworks don't specify how to manage different types of risks; each business must decide that for itself based on unique factors, such as its risk appetite levels and operational resources. However, ERM frameworks outline the key requirements a business should meet to manage risks effectively. That helps organizations avoid blind spots when creating an ERM program.
The following are popular ERM frameworks that risk management teams could consider using to streamline and structure the program implementation process. The first two are the most widely used frameworks for full-fledged ERM implementations, while the others are more narrowly focused but can be applied as part of ERM deployments.
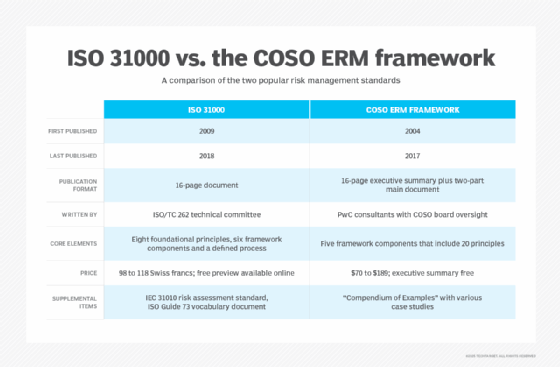
COSO ERM framework
The COSO ERM framework was developed by the Committee of Sponsoring Organizations of the Treadway Commission, a thought leadership group, commonly known as COSO, that has also created a widely used internal control framework. The ERM one, first published in 2004 and revised in 2017, is a broad and flexible risk management framework rooted in five key risk-related components:
- Governance and culture.
- Strategy and objective-setting.
- Performance.
- Review and revision.
- Information, communication and reporting.
Because the COSO framework doesn't focus on specific types or categories of risk, it can accommodate virtually any risk management scenario for any business or industry. However, a potential downside is that it's so generic that it can be difficult to follow. For example, the framework includes very little in the way of risk management guidance tailored for individual industries.
ISO 31000
ISO 31000 was developed by the International Organization for Standardization, which is known globally by the acronym ISO. Created in 2009 and updated in 2018, it's also a broad and flexible framework that breaks ERM strategy into three primary components:
- Principles, or the guiding ideas and philosophies behind ERM.
- Framework, which covers the organizational commitments necessary to manage risk.
- Process, which addresses the various risk management processes an organization should implement.
ISO 31000 divides each of these high-level components into subparts. This approach provides ERM guidance with a relatively high degree of specificity while still retaining enough flexibility to support various types of businesses and industries. A common criticism of ISO 31000, though, is that it can sometimes breed a false sense of security because simply implementing its tenets doesn't mean a business is effectively mitigating all risks.
CAS ERM framework
The Casualty Actuarial Society (CAS) is a credentialing and education organization that focuses on property and casualty risks. Outlined in 2003, its conceptual framework for ERM is distinguished by an emphasis on ensuring that risk management is a holistic process. Rather than expecting each department in a business to separately manage the risks that affect it, the CAS framework aims to integrate risk management seamlessly across the organization through a set of seven steps.
When done effectively, this approach can increase ERM's efficiency and turn it into a truly organization-wide strategy. A potential downside of the CAS framework is that it's geared primarily toward managing financial risks. That said, it's flexible enough to accommodate any type of risk management scenario.
COBIT
Short for Control Objectives for Information Technologies, COBIT is an information and technology governance framework that supports IT risk management. Initially developed by the ISACA professional association in 1996 and most recently updated in a COBIT 2019 release, the framework aims to keep IT systems and processes in alignment with risk tolerance levels. Since IT touches virtually every part of most businesses today, COBIT can serve as an effective foundation for developing an ERM program. However, it doesn't explicitly address risk categories that aren't directly related to IT.
NIST Risk Management Framework
Developed in 2010 and revised in 2018, the NIST Risk Management Framework (RMF) outlines a seven-step process focused primarily on risks related to cybersecurity and data privacy. As such, the RMF isn't ideal for organizations seeking a comprehensive ERM framework, but it can be helpful for those aiming to adopt a proactive approach to managing security and privacy risks.
10 key steps to implement an ERM program
The exact process for developing an ERM program can vary from one organization to the next. But in general, the key implementation steps to take include the following:
1. Get business buy-in
First, individuals or groups seeking to create an ERM program must obtain buy-in from business stakeholders. To do this, they need to demonstrate the value an ERM program can bring to the business -- even for organizations that already believe they're managing risks effectively. Focusing on the potential benefits of an ERM program described previously can help gain the required support.
2. Establish an ERM steering committee
Typically, it makes sense to appoint a steering committee to oversee the ERM program implementation process. The committee will ideally include representatives of various parts of the business, such as finance, IT, HR, operations and executive leadership, in addition to the CRO or another risk management leader.
3. Identify relevant risk categories
The steering committee should perform a comprehensive assessment of the types or categories of risk the ERM program should address. Relevant risk types differ from organization to organization, even in the same industry, so each business needs to determine which risks it will prioritize managing as part of the program.
4. Assess the organization's risk appetite
To define the requirements of an ERM program, it's helpful to first define the organization's risk appetite, meaning the level of risk it's willing to accept in pursuit of its strategic goals. Creating a risk appetite statement that specifies those levels for different types of risk can be useful for this purpose -- and for managing risks after the program is implemented. At this stage, the steering committee can also define key risk indicators. KRIs are metrics designed to warn of potential business risks that exceed related risk appetite levels.
5. Choose an ERM framework
To help facilitate the ERM implementation, the steering committee should adopt an ERM framework such as the ones described above. In doing so, it should determine which one is the best fit, based on business priorities and the risk management requirements, as well as the balance between flexibility and specificity that the organization is looking for in a framework.
6. Define risk management processes, procedures and controls
Next, based on guidance from the chosen ERM framework, the steering committee should determine which processes, procedures and controls will be implemented to manage risks. This step should also reflect consideration of strategies for preventing harmful impacts through risk mitigation efforts, as well as how the business will respond to the fallout if it doesn't succeed in fully mitigating risks.
7. Create measurement and review processes for the ERM program
To help determine whether the ERM program is effective, the steering committee should also develop processes for reviewing its progress and metrics for measuring its success. For example, metrics might include the frequency and severity of incidents related to a specific risk category, risk mitigation costs, and mean time to detect and resolve risk-related incidents.
8. Assign risk management roles and responsibilities
With a general ERM plan in place, the steering committee can assign roles and responsibilities for implementing the risk management processes and enforcing the relevant controls and risk mitigation measures. Those tasks are often handled by a combination of risk managers, business executives and risk management specialists.
9. Enable the ERM program
Once the involved stakeholders know what they need to do, the business can declare the ERM program to be in effect. At this point, the program should be fully operationalized. This includes communicating the risk appetite statement and the risk management processes, procedures and controls across the organization so that all business managers and employees are aware of them.
10. Develop plans to regularly revisit and revise the ERM strategy
Because business risks and strategic goals commonly change over time, reviewing the ERM program and updating it when needed are crucial tasks as part of an ongoing implementation. Ideally, a review should occur at least once per year. It's also a best practice to review relevant parts of the ERM program if a new risk emerges, such as possible penalties related to a new regulatory compliance rule, or when an event, such as a cyberattack, shows the current program is inadequate in some areas.
Common ERM implementation challenges and ways to resolve them
Planning and implementing an ERM program is a complex process, and many things can go wrong along the way. Common challenges that risk management leaders and teams face include the following:
- Lack of buy-in from business leadership. Corporate executives and other business leaders might be hesitant to endorse a formal ERM strategy, especially if they believe the organization already manages risks adequately. In response, it's helpful to point out that, although departments and business units might be working separately to keep risks in check, a systematic approach to ERM can help an organization do so more efficiently and predictably.
- Resistance to change. Like virtually any major business initiative, an ERM program will affect workflows and responsibilities across the organization, and some workers might be reluctant to embrace the changes. A company can ease the transition by providing adequate training and resources to help employees understand why ERM is important and ensure that they're equipped to follow the necessary risk management processes.
- Resource shortages. Lack of sufficient resources for supporting an ERM program implementation can be a challenge, especially for organizations whose budgets are already stretched. To work around this issue and get more resources, consider emphasizing that ERM is a way to save money rather than a mere cost center. It's also possible to implement ERM programs incrementally -- for example, by focusing on items that will have the biggest business impact at the lowest relative cost. Doing so might be more financially feasible for businesses that are short on the resources needed to implement a full-scale ERM initiative.
- A disconnect between ERM reporting and reality. Sometimes, an ERM program that looks healthy on paper might be less effective in practice. This can happen when the business tracks the wrong metrics, or when risk reports and audits don't go into enough detail to uncover deficiencies. The best way to avoid this pitfall is to require meaningful data collection and reporting as part of the ERM process.
- Changing requirements. Again, risks evolve constantly, as do strategic goals. An ERM program that was designed to address one set of risks and pursue one set of goals might become ineffective later. To mitigate this challenge, be sure to revisit ERM strategies and procedures on a recurring basis.
Chris Tozzi is a freelance writer, research adviser and professor of IT and society. He has previously worked as a journalist and Linux systems administrator.