What is a domain controller?
A domain controller is a server that processes authentication requests from users and computers within a computer domain. Domain controllers are most commonly used in Windows Active Directory (AD) domains, but are also used with other types of identity management systems.
Domain controllers maintain directory service information for their domains, including users, authentication credentials and enterprise security policies.
What are the main functions of a domain controller?
Domain controllers restrict access to domain resources by authenticating user identity through login credentials and preventing unauthorized access to those resources.
Domain controllers apply security policies to requests for access to domain resources. For example, in a Windows AD domain, the domain controller draws authentication information for user accounts from AD.
A domain controller can operate as a single system, but is usually implemented in clusters for improved reliability and availability. For domain controllers running under Windows AD, each cluster comprises a primary domain controller and one or more backup domain controllers.
Insecure sites can use a read-only domain controller to speed up authentication. In Unix and Linux environments, domain controllers can manage Lightweight Directory Access Protocol domains.
Why is securing a domain controller important?
Domain controllers authorize all domain access, blocking unauthorized access to domain resources while allowing users access to authorized directory services. They also store many of the secrets that a domain uses to protect users and data. If someone gains unauthorized access to a domain controller, they can quickly gain access to all the data stored on the network, making domain controllers a primary target for attackers.
It is important to harden the domain controller with additional security mechanisms, such as the following:
- Firewalls.
- Isolated networks.
- Security protocols and encryption to protect stored data and data in transit.
- Restricted use of insecure protocols, such as Remote Desktop Protocol, on controllers.
- Deployment in a physically restricted location for security.
- Expedited patch and configuration management.
- Blocking internet access for domain controllers.
- Dedicated administrator accounts.
How are domain controllers set up in Active Directory?
The domain controller is the central server in a Windows AD domain. Domain controllers are servers that can use AD to respond to authentication requests.
Experts advise against relying on a single domain controller, even for smaller organizations. Best practices call for one primary domain controller and at least one backup domain controller to avoid downtime caused by system unavailability.
Domain controllers can be deployed on physical servers, running as virtual machines (VMs) or as part of a cloud directory service. It is best practice to deploy each domain controller on a standalone server. This includes virtual domain controllers, which should run on VMs running on different physical hosts. This minimizes the possibility of a compromise on another machine affecting the domain controller.
Setting up an AD domain controller includes the following steps:
- Domain assessment. The first step in setting up a domain controller is to assess the domain in which the controller will be set up. This assessment includes determining what types of domain controllers are needed, where they will be located and how they interoperate with existing systems in the domain.
- New deployment or addition. Whether planning for a new deployment of AD domain controllers or adding a new controller for an existing domain, determine the domain controller location as well as the resources needed to run the centralized domain controller and any virtual domain controllers.
- Security by design. It's imperative to secure a domain controller from internal or external attacks. The domain controller architecture must also be designed to withstand service disruptions such as loss of connectivity, loss of power or system failures.
Specifics for setting up and configuring AD domain controllers vary depending on the version of Windows Server used on the domain.
Other domain controller implementation options
The following options are available when setting up a domain controller with AD:
- Domain Name System server. The DNS domain controller can be configured to function as a DNS server. The DNS service provides the mapping of the computer name to its associated Internet Protocol address.
- Global catalog capabilities. The domain controller can be configured to use the global catalog, which enables the controller to return AD information about any object in the organization forest, regardless of whether the object is in the same domain as the domain controller. This is useful for large enterprises with multiple AD domains.
- Read-only domain controller. Domain controllers used in branch offices or in other circumstances where network connectivity is limited can be configured as read-only.
- Directory Services Restore Mode. DSRM enables emergency maintenance, including restoring backups, on the domain controller. A DSRM password must be configured in advance.
- Certificate services. Certificate services enable a domain controller to issue and authenticate certificates for authentication and encryption.
- Group policy. Domain controllers host AD group policies, which can be used to enforce security settings on domain member servers and clients.
- Distributed file system. DFS uses multiple file servers to host shared files. The servers can automatically replicate files and hide the underlying server structure from end users.
The same server can host other Windows services, such as a file share or print server. However, this is not recommended, as these other services could compromise the domain controller.
What are the benefits of domain controllers?
Domain controller benefits include the following:
- Centralized management of authentication enables organizations to authenticate all access requests with a single set of credentials.
- Enforcement of security policies, such as password age, complexity and lockout, helps to prevent unauthorized access across an enterprise.
- Access to file servers, email and other network resources through domain controllers provides seamless integration with Microsoft AD.
- Support for secured authentication and transport protocols in domain controllers improves authentication process security.
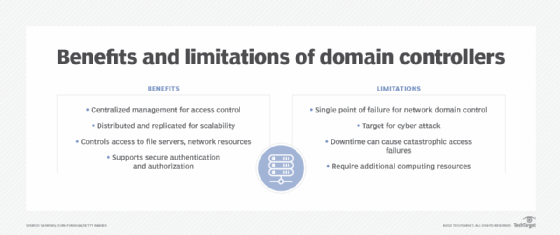
What are the limitations of domain controllers?
Some domain controller limitations include the following:
- Domain controllers can be a single point of failure for network domain control.
- Because they control access to the entire network, domain controllers are a target for cyberattacks. Successfully hacking a domain controller could give the attacker access to all domain network resources as well as authentication credentials for all users in the domain.
- Networks that use domain controllers for authentication and access security are dependent on them. To reduce the risk of downtime, controllers can be deployed in clusters.
- Domain controllers require additional infrastructure and security mechanisms.
Alternatives to domain controllers
Domain controllers have historically been the center of an organization's identity and access management. Still, they don't natively support many of the advanced features that are part of a modern environment.
Traditional castle-and-moat-style networks have given way to zero-trust networks. Simple passwords are being replaced by passkeys and two-factor authentication.
Microsoft Entra ID is a cloud-based identity manager. It is part of Microsoft's Azure cloud platform. Entra ID is designed to be secure from the start and support modern authentication.
Federated identities enable one authentication service to be used for other services. For example, a Google account can be used to sign in to an accounting website.
Amazon Web Services Directory Service is a managed AD service offered by Amazon. It hosts an AD environment in AWS.
Hybrid domain controllers
Hybrid cloud environments, which combine on-premises and cloud-based infrastructure, are becoming more prevalent. Domain controllers can be configured with tools to sync accounts and passwords with a cloud identity provider, such as Microsoft Entra ID. This enables users to have a single set of credentials that works for both on-premises and internet resources.
With hybrid deployments, a single management interface can be used to control access to all resources. Hybrid deployments are a good option for organizations that are not ready to move entirely to the cloud, but that use some online resources.
Account sync can be set up to be one-way or two-way. In a one-way sync, the on-premises information is sent to the cloud provider. Typically, only password hashes are synced; this prevents the possibility of the passwords being compromised, but could also prevent some features from working, such as self-service password resets. In a two-way sync, the online service can change the on-premises accounts.
Domain controllers are fundamental to securing unauthorized access to an organization's domains. Learn how to securely set up and deploy a Windows Server 2022 domain controller. Also, check out this Windows Server 2022 security hardening guide for admins.






