Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP)
What is Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP)?
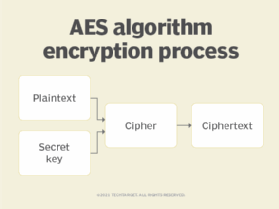
Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP) is an encryption protocol based on the U.S. federal government's Advanced Encryption Standard (AES) algorithm and uses the Counter Mode with CBC-MAC (CCM) mode of operation.
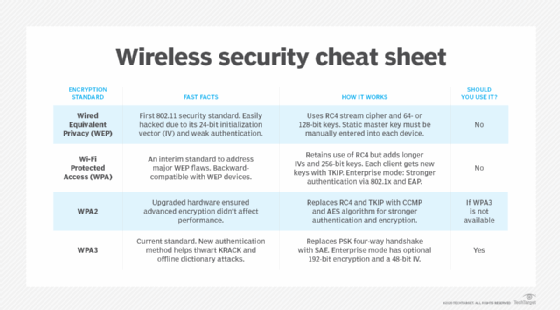
CCMP replaces Rivest Cipher 4 used in Wired Equivalent Privacy (WEP) and Temporal Key Integrity Protocol (TKIP). It was introduced with the Wi-Fi Protected Access 2 (WPA2) wireless security standard.
CCMP forms part of the 802.11i standard for wireless local area networks (WLANs). It implements amended standards to the original 802.11 standard. This protocol was developed by the 802.11i task group in response to the growth of WLAN and the need for more secure encryption protocols. CCMP was developed to address the vulnerabilities of the existing WEP protocol.
CCMP uses the AES cipher to encrypt sensitive data. It employs 128-bit keys and a 48-bit initialization vector (IV), also known as a CCM nonce block, to detect replays and minimize vulnerability to replay attacks.
The two main components of CCMP are Counter Mode and CBC-MAC. The Counter Mode component provides data privacy, while CBC-MAC provides data integrity and authentication. CCM is a generic authenticated encryption block cipher mode, meaning it can be used with any block-oriented encryption algorithm.
Characteristics of CCMP
The following are the core characteristics of CCMP:
- It is defined only for use with 128-bit block ciphers.
- CCMP key and block size are both 128 bits.
- CCM mode involves two parameter choices:
- M: The size of authentication field
- It requires a tradeoff between message expansion and the probability that an attacker could modify a message without being detected.
- Valid values: 4, 6, 8, 10, 12, 14, 16 octets.
- L: The size of length field
- It requires a tradeoff between the maximum message size and nonce size.
- Valid values range between 2-8 octets.
- M: The size of authentication field
- CCM provides parameters: K=16, M=8, L=2.
- CCM requires a fresh temporal key for every session since it exists only for the duration of a transaction.
- CCM requires a unique nonce value for each frame protected by a given temporal key and a 48-bit packet number.
- Reuse of a packet number with the same temporal key nullifies security guarantees.
In CCMP, packet numbers increment with each data frame, which is known as a MAC protocol data unit (MPDU), or plaintext data payload (see the next two sections). After MAC encapsulation, the plaintext MPDU becomes a MAC service data unit, or MSDU.
A nonce is generated one time for a specific transaction. It is created from the packet number, the transmit address and quality of service (QoS) data that is contained in the frame header.
Temporal keys are an integral part of the authentication process in CCMP. A temporal key is discarded after each transaction.
CCMP encapsulation
Here is how CCMP encapsulates a plaintext MPDU:
- It increments the 48-bit packet number to obtain a fresh one for every MPDU.
- It uses the fields in the MAC header to construct the additional authentication data (AAD).
- It constructs the IV from the packet number, destination IP address and MPDU priority.
- It encodes the key ID and the new packet number into the 8-octet CCMP header.
- It runs the Counter Mode AES with the temporal key, AAD, nonce and MPDU data. This forms the ciphertext and message integrity check (MIC).
- It links together the original MAC header, CCMP header, encrypted data and MIC to form the encrypted MPDU.
Message integrity check computation in CCMP
To calculate a MIC for the MPDU, CCMP uses AES in the CBC-MAC mode. There are three inputs required for this process:
- plaintext MPDU
- initial block for the MPDU
- temporal key
First, the algorithm encrypts the initial block to produce the CBC mode IV. Then, it calculates CBC-MAC with the plaintext MPDU data, the IEEE 802.11 header length and selected parts of the IEEE 802.11 MPDU header. The algorithm's output is a MIC value, which is appended to the MPDU on transmit. At the receiver, it is compared with the received MIC.
Counter Mode encryption
To encrypt and decrypt MPDU and MIC data, CCMP uses AES in Counter Mode. For this process, the input includes the following:
- MPDU data field with MIC appended
- counter for the MPDU
- temporal key
During transmission, the data field with MIC is plaintext. Upon reception, it becomes ciphertext. The algorithm's output is an encrypted MPDU data field on transmission and a decrypted MPDU data field with MIC upon reception.
During encryption, the Counter Mode preload contains the following:
- a flag byte
- 1 byte of QoS information
- a 6-byte address field
- a 6-byte packet number
- a 2-byte counter
CCMP decapsulation
CCMP only requires AES operations -- and no decryption operations. When the calculated MIC value matches with the MIC value received in the encrypted MPDU, the decapsulation process is successful.
See best practices for wireless network security, five tips for managing guest wireless network access and how the WPA3 security protocol simplifies logins and secures IoT.