
supply chain management (SCM)
What is supply chain management (SCM)?
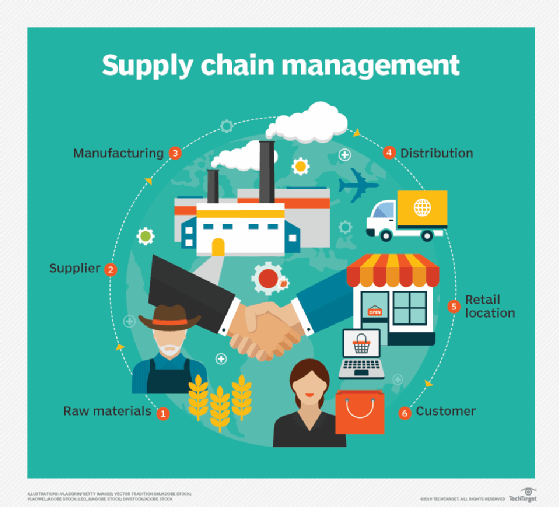
Supply chain management (SCM) is the optimization of a product's creation and flow from raw material sourcing to production, logistics and delivery to the final customer.
SCM encompasses the integrated planning and execution of processes required to manage the movement of materials, information and financial capital in activities that broadly include demand planning, sourcing, production, inventory management and storage, transportation -- or logistics -- and returning excess or defective products. Effective supply chain management relies on business strategy, specialized software and collaboration.
Because it's such an expansive, complex undertaking, each partner -- from suppliers to manufacturers and beyond -- must communicate and work together to create efficiencies, manage risk and adapt quickly to change.
Other areas of major concern for today's companies include supply chain sustainability -- which covers environmental, social and legal issues, in addition to sustainable procurement -- and the closely related concept of corporate social responsibility -- which evaluates a company's effect on the environment and social well-being.
This article is part of
Guide to supply chain management
The history of supply chain management
Supply chain management has been essential to business since the dawn of the Industrial Revolution. Mass-production manufacturing was a key driver in supply chain evolution, along with the standardization of automobile parts to streamline the manufacturing process. With the advent of computers in business, SCM took another great leap forward as it became possible to coordinate supply chain management across many different sources, including data from suppliers, distribution centers and transportation providers.
Even so, supply chain management was largely a linear process, and one in which only a limited number of employees participated.
The simultaneous arrival of the internet and the expansion of the global economy made the linear view of the supply chain obsolete. Supply chain management now describes the integration of many complex networks of dynamic data sources that are often updating in real time, 24/7, and mastery of this complexity is increasingly essential to the assessment of customer needs and the accurate forecasting and efficient fulfillment of customer demand. This demand-driven operational model requires organizations to maintain SCM systems that are highly responsive and flexible. These systems require a considerable institutional investment, diligent communication with partner companies and broad participation of employees within the enterprise.
Benefits of supply chain management
Supply chain management creates numerous benefits that translate to higher profits, better brand image and greater competitive advantage. These include the following:
- Better ability to predict and meet customer demand.
- Better supply chain visibility, risk management and predictive capabilities.
- More accurate forecasting to support decision-making.
- Fewer process inefficiencies and less product waste.
- Improvements in quality.
- Increased sustainability, both from a societal and an environmental standpoint.
- Lower overhead.
- Improvements in cash flow.
- More efficient logistics.
5 stages of supply chain management
Supply chain management can be broadly categorized into the following five steps or areas:
- Plan. Using supply chain analytics and materials management features in enterprise resource planning (ERP) systems, organizations create strategic plans to meet customer demand for product and avoid a bullwhip effect.
- Source. Organizations identify and select vendors that can supply materials in a streamlined and efficient way according to agreements. Supply chain collaboration starts at this stage and is important throughout the supply chain management process.
- Make. In this stage, products are manufactured. This includes production scheduling, testing, ensuring compliance requirements are followed, packing, storage and release. Multiple machines are likely to be involved, especially for larger companies, and these increasingly use technologies such as internet of things (IoT) and artificial intelligence (AI) to work more efficiently.
- Deliver. This stage pertains to logistics and focuses on getting finished goods to consumers, in whatever manner of transportation is needed. As the Amazon effect has grown, more focus is on doorstep delivery. Greater emphasis is now also on supply chain leaders working more closely with customer service. Inventory management and warehouse management systems are especially crucial at this stage.
- Return. This stage includes all product returns, including defective products and products that will no longer be supported. The return stage also includes elements from other stages, including inventory and transportation management.
Example of SCM
The most basic version of a supply chain includes a company, its suppliers and its customers. An example would be a raw material producer, manufacturer, distributor, retailer and retail customer.
Most supply chains are far more complex and layered. This is why examples of unsuccessful supply chain management, where risk isn't managed or disruption occurs, can be so helpful.
Food shortages during COVID-19 are a good example of supply chain management gone awry. The food supply chain was disrupted in several ways. For example, many restaurants and schools closed to accommodate stay-at-home orders, causing bulk products meant to go to institutional settings to no longer be needed. Instead, far more consumers were eating at home, which had different packaging requirements, among other issues. The meat industry also ran into supply chain management disruptions due to COVID-19 outbreaks in slaughterhouses.
Now more than three years later, supply chains are still reeling from the effects of material and labor shortages. But a different problem exists: According to data from global management consulting firm Kearney, excess inventory of high-end electronics components is a $250 billion problem. After organizations raced to replenish and manufacture key components, suppliers were left with excess inventory as growth and demand leveled out.
The future of supply chain management
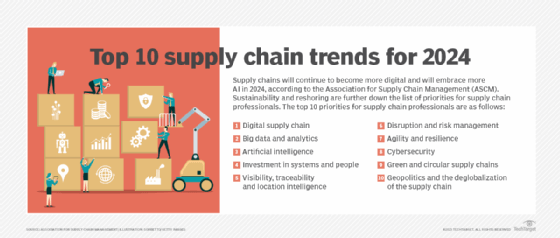
The next phase of supply chain management evolution will likely include the deployment of AI resources and machine learning to speed the processing of data and expand the utility of its results; and supply chain planning, a periodic undertaking in the past, will become a continuous-improvement process.
The role of supply chain management software
Technology is critical in managing today's supply chains, and ERP vendors offer modules that focus on key functions within SCM. There are also business software vendors that focus specifically on SCM. Important areas to note include the following:
- Supply chain planning software for activities such as demand management.
- Supply chain execution software for activities such as day-to-day manufacturing operations.
- Supply chain visibility software for tasks such as spotting and anticipating risks and proactively managing them.
- Inventory management software for tasks such as tracking and optimizing inventory levels.
- Logistics management software and transportation management systems for activities such as managing the transport of goods, especially across global supply chains.
- Warehouse management systems for activities related to warehouse operations.
Infor, Manhattan Associates, Oracle, Panasonic -- which acquired Blue Yonder in 2021 -- and SAP are examples of vendors of supply chain software.
The increasingly global nature of today's supply chains and the rise of e-commerce -- with its focus on nearly instant small deliveries straight to consumers -- are posing challenges, particularly in logistics and demand planning. Strategies such as lean manufacturing and newer approaches, like demand-driven material requirements planning, might prove helpful.
Technology -- especially big data, predictive analytics, IoT technology, supply chain analytics, robotics and autonomous vehicles -- is also being used to help solve modern challenges, including in the areas of supply chain risk and disruption and supply chain sustainability.
For example, IoT can help with transparency and traceability to help boost food quality and safety by using sensors to monitor the temperature of perishable food while it's in transit. Analytics can also help determine where to put smart lockers in densely populated areas to reduce the number of single-item deliveries and lower greenhouse gas emissions.
Learn how RFID can help companies improve product availability by managing their supply chain and logistics operations.





