What is Cisco ISE?
Cisco Identity Services Engine (ISE) is a security policy management platform that provides secure network access to end users and devices. Cisco ISE enables the creation and enforcement of security and access policies for users and endpoints connected to network infrastructure, such as routers and switches. It is intended to help organizations simplify identity management across devices and applications, make proactive governance decisions, and implement a zero-trust model across their IT environments.
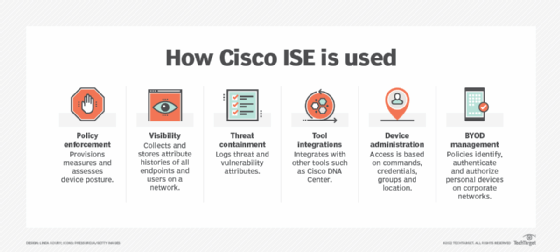
How is Cisco ISE used?
Cisco Identity Services Engine combines network access control (NAC), a zero-trust architecture, and identity and access control policy tools into one platform. Organizations can use Cisco ISE to define and enforce access policies with greater precision and meet compliance and reporting requirements. By enabling granular, policy-driven permissions for different populations of users and devices on a distributed network, Cisco ISE functions as a consolidated system for authentication, authorization and accounting (AAA). In doing so, it seeks to lower security risk and protect its IT assets and data from cyberattacks, data breaches and other undesirable events.
Cisco ISE can further strengthen network security and streamline security policy management by integrating with other security products. It can share information like user and device identities, as well as threats and vulnerabilities, with other Cisco and non-Cisco tools to jointly identify threats, isolate (or remove) infected endpoints and protect business-critical data.
In addition to policy enforcement, IT administrators can use ISE to improve network visibility, grant guest access to the network, and perform threat containment, tool integrations, device administration and bring your own device (BYOD) management.
Enhanced network visibility provides the ability to see not only which users and devices are connected but also the applications that are installed and running. Such visibility helps to strengthen network security and reduce the size of the attack surface. This then allows IT administrators to contain threats like malware in the network, minimizing their lateral movement and reducing the scope for damage.
Cisco ISE can authenticate wired, wireless and virtual private network (VPN) users. It can identify and log a user's identity, location and access history, as well as assign different services based on those unique properties. Administrators can also configure network devices with IPv6.
The platform can also help organizations to streamline their service operations by consolidating management of network infrastructure, such as switches, routers and firewalls. This reduces the operational burden on IT teams and supports more consistent policy enforcement.
Taken together, these features and capabilities make Cisco ISE well-suited to zero-trust strategies. With this platform, organizations can implement effective, highly granular, identity-based access management across wired and wireless networks.
How does Cisco ISE work?
With an increased number of users and devices accessing networks remotely, protecting an organization's data from network security breaches becomes more complex. Administrators can use Cisco Identity Services Engine to control who has access to their network and ensure authorized, policy-compliant devices obtain connectivity.
Cisco ISE is built to allow only trusted users and devices to access the resources on an enterprise network. It works with other network devices to create contextual identities for users and devices. Organizations can then use these all-encompassing identities to enforce secure access policies.
The platform obtains information from multiple sources to automatically identify and classify devices. Through passive network monitoring and telemetry, Cisco ISE collects endpoint attribute data. Its Profiler function then passes on these attributes to the analyzer. Here, all known endpoints are classified according to their policies and identity groups.
Using its Wi-Fi Edge Analytics feature, Cisco ISE obtains data from Apple, Intel and Samsung devices to conduct enhanced profiling according to attributes like device model, OS version and firmware. In addition, it uses predefined and custom device templates to automatically associate administrator-defined identities to connected endpoints and to associate authorization policies for specific types of endpoints.
Cisco ISE deployment
Cisco Identity Services Engine is available as both a physical or virtual appliance. The virtual appliances can run on VMware ESXi 6.5, 6.7 and 7.x, KVM on Red Hat 7.x, Microsoft Hyper-V (on Microsoft Windows Server 2012R2 and later), as well as many other on-premises and cloud platforms. Organizations can use either type of deployment to create clusters. These clusters provide the scale, redundancy and failover enterprise networks require.
Organizations also have the flexibility to deploy Cisco ISE in standalone or distributed modes. In distributed deployments, also known as high-availability or redundant deployments, one machine assumes the primary role. Another machine assumes the secondary role and is considered the backup.
Additionally, the Cisco ISE architecture can be deployed with what Cisco refers to as Administration, Monitoring and Troubleshooting, Policy Service, and pxGrid personas. These personas are roles assigned to each ISE node, which constitutes a single virtual or physical appliance. The Administration persona provides a comprehensive, consolidated portal for all the core functions of network configuration and management. The other personas provide more specialized functions to create a fully scalable, integrated system.
Another available node for Cisco ISE is the Inline Posture node. Network admins can use this node to enforce policies and execute change of authorization requests that other network devices cannot accommodate.
Top Cisco ISE features
Cisco ISE helps to protect networks from cyberattacks using the following features:
- Access control. Provides numerous access control options that include downloadable access control lists (ACLs), virtual LAN, URL redirections and security group ACLs to reduce the attack surface and strengthen overall network security.
- Centralized management. Administrators can configure, manage and authenticate users and devices from a single, user-friendly GUI. The console's unified view also simplifies network administration.
- Cisco DNA Center integration. This network controller and analytics platform integrates with ISE to simplify the setup of various Cisco ISE services. It also aids in policy design, provisioning and assignment to users and applications instead of network devices. Additionally, it enables admins to deploy group-based access controls and implement network segmentation based on business requirements.
- Contextual identity and business policies. A rule-based, attribute-driven policy model makes it easy to implement business-relevant access control policies. Admins can create attributes like authentication protocols, device identity and posture validation, and reuse them as needed.
- Dynamic Reauthentication Times. Admins can create temporary policies for devices that do not need continuous access. After the designated period expires, devices lose network authentication.
- Cipher control. Admins can edit a list of ciphers and disable those no longer needed to ensure uninterrupted compliance with security standards.
- Device profiling. Cisco ISE can create custom device templates that automatically detect, classify and associate administration identities for connected endpoints.
- Guest lifecycle management. Built-in support for hotspot, sponsored, self-service and other access workflows, plus real-time visual flows remove the complexity from implementing and customizing guest network access.
- IPv6 support. Cisco ISE is IPv6-ready for all RADIUS and TACACS+ based network devices.
- Monitoring and troubleshooting. ISE users can access a built-in console for detailed reports (historical and real time) of network monitoring, reporting and troubleshooting data.
In addition to the above, other key features of Cisco ISE include the following:
- Common policy automation. Cisco ISE acts as a universal translator that enables different parts of the network architecture to understand each other, regardless of whether they are legacy or next-gen elements.
- PxGrid Direct enhancements. These improvements enable organizations to immediately synchronize data from PxGrid Direct Connectors, ensuring fast database updates.
- PAC-less Communication. ISE typically uses Protected Access Credentials, or PACs, to establish encrypted TLS tunnels. Cisco ISE 3.4 introduced PAC-less Communication to streamline communication between ISE and Cisco TrustSec devices.
- AI/ML profiling and multifactor classification. Cisco ISE can quickly create a profile and rules for identical unknown endpoints to simplify management and boost security.
- Security group tags. SGTs simplify segmentation and the management of switches, routers and other network devices.
Benefits of Cisco ISE
Cisco Identity Services Engine offers the following benefits:
- Centralized network access control (NAC). All an organization's network access points can be controlled from one centralized location, reducing management overhead and enhancing security.
- Simplified network visibility. ISE stores detailed attribute histories of all endpoints and users connected to a network to ensure comprehensive, real-time visibility into the entire network.
- Threat containment. ISE matches endpoints with attributes like users, location, threat and vulnerability, enabling administrators to choose who and what devices to allow on a network.
- Zero-trust implementation. Organizations can easily implement a zero-trust network architecture to ensure secure network access, lower the risk of harmful events, and protect business integrity and continuity.
- Easy administration access control and auditing. Audit trails are maintained for every change in the network, allowing admins to easily conduct audits and troubleshoot issues.
- More control over Domain Controllers (DC). Cisco ISE maintains Active Directory site awareness and ensures that a DC is always available.
- Automated compliance. Cisco ISE uses a persistent client-based agent, a temporal agent or a query to an external endpoint management tool to enforce required compliance policies for endpoints.
Cisco ISE licensing
Cisco ISE is licensed on a subscription basis, but a 90-day free evaluation license can be downloaded for up to 100 endpoints. The evaluation license includes all the features of a full license and allows admins to set up a limited deployment in Evaluation mode. When the license expires, admins can only view the Licensing window in the Cisco ISE administrator portal. It is possible to request an extension to the license or coverage for additional endpoints.
The full versions of Cisco ISE are licensed on a subscription basis for terms of one, three and five years. Cisco offers three tiers of licenses: Essentials, Advantage and Premier.
Essentials is the base package, and Premier is the highest tier. All license packages for Cisco ISE are set up in a nested doll model, meaning all the features in the Essentials and Advantage tiers appear in the Premier edition, and all the features in the Essentials edition appear in the Advantage tier. Simply put, the higher-tier licenses include all the features of the lower-tier licenses.
Essentials includes the following features and capabilities:
- AAA and 802.1x.
- Support for Guest functionality on endpoints with RADIUS sessions.
- Easy Connect (PassiveID).
The Advantage license includes all the features and capabilities of the Essentials license, along with the following:
- Endpoint profiling classification in authorization policies.
- BYOD support.
- PxGrid, PxGrid Cloud and PxGrid Direct for endpoints with RADIUS sessions.
- Group-based policy (TrustSec).
- Endpoint analytics visibility and enforcement.
- Adaptive Network Control policy and User-Defined Network attributes in authorization policies.
The Premier license contains the most features, including all the above plus the following:
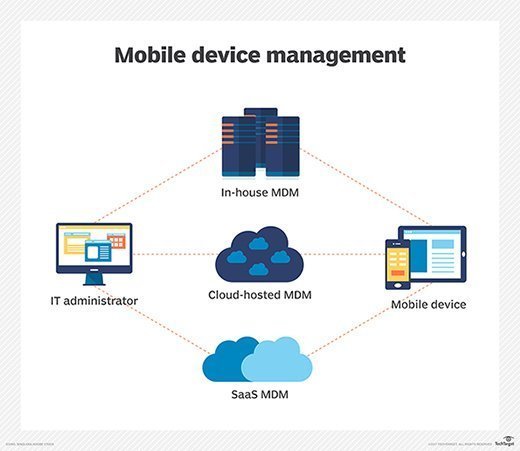
- Mobile device management visibility and enforcement.
- Posture visibility.
- Compliance visibility.
- Threat-centric NAC.
- Segmentation using Cisco Software-Defined Access.
- Cisco AnyConnect intelligent VPN/zero-trust network access with agent.
All subscriptions automatically renew at the completion of the license term (12, 36 or 60 months) for an additional 12-month term. To prevent automatic renewals, customers must deselect the option when placing the initial order. They can also choose to cancel a renewal up to 60 days before the new term's start date.
Learn about some other ways to improve network visibility and security, such as including intrusion detection systems, automation or executive support.







