What is an information system (IS)?
An information system (IS) is an interconnected set of components used to collect, store, process and transmit data and digital information. At its core, it is a collection of hardware, software, data, people and processes that work together to transform raw data into useful information. An IS supports a variety of business objectives, such as improved customer service or increased operational efficiency.
Typically, an IS comprises an integrated set of hardware and software, plus databases and communications networks that facilitate data collection, storage and use. People and processes are also vital components of an IS.
An organization may implement different types of ISes, such as the following:
- Management information system (MIS). These computerized systems collect, store, process and present data to support management decision-making. Different kinds of organizations and industries use different types of MISes. For example, an MIS in a hospital may collect data on patient admissions, treatments and outcomes to help administrators make decisions about resource allocation and process improvements.
- Decision support system (DSS). A DSS enables users to explore and analyze data to gain insights into business performance and, accordingly, make data-driven decisions. For example, a retail chain may use a DSS to collect and analyze data on customer demographics, buying behavior and sales performance in order to guide changes in inventory management and marketing campaigns. A DSS is also known as a business intelligence (BI) system.
- Knowledge work system (KWS). These systems provide useful insights for knowledge workers, such as researchers, analysts and consultants. For example, marketing analysts may use a KWS to analyze customer data and track the performance of marketing campaigns.
- Executive information system (EIS). An EIS provides high-level information about the company's financial performance, market trends, competitive landscape and so on. It also provides analytical tools that enable senior executives to make strategic decisions based on the available information.
Other types of ISes include the following:
- Knowledge management system (KMS). A KMS is an information system used to update and manage the organization's knowledge resources.
- Inventory management system (IMS). An IMS collects inventory information and generates insights to help with inventory management.
- Transaction processing system (TPS). A TPS processes transactional data and generates useful insights to help streamline transactional processes.
- Customer relationship management (CRM) platform. A CRM platform is a comprehensive tool or set of tools that enables organizations to view customer information in real time and use that information to guide their sales, marketing, support, commerce and other decisions.
The effectiveness of any enterprise IS depends on whether it aligns with the organization's information requirements, as well as its business goals, usability and features related to information security and regulatory compliance.
Who uses information systems?
Information systems are crucial drivers of the modern digital economy. They enable digitized organizations to do more with their data and information assets. A reliable IS enables different departments, teams and functions to access and share the data they need for their specific purposes.
For example, the accounting team may use an IS to streamline audit processes, identify and manage financial risk, and generate accurate financial reports. Similarly, sales and marketing teams may rely on one or more of the company's ISes to identify prospects, understand customer demographics, and design targeted sales or marketing campaigns.
Other business functions that typically use ISes within their operations include the following:
- Human resource (HR) management.
- Operations.
- Supply chain management.
- Customer support.
- Information security and cybersecurity.
- Risk management.
- Compliance.
Individuals also use various kinds of information systems, many of them internet-based, in their private and professional lives. For example, an IS may be used for shopping, studying specific topics or performing banking transactions. Information systems are also available for entertainment, socializing, and access to digital products and cloud services.
Benefits of information systems
A comprehensive IS facilitates communication and coordination, both within the host organization and between the organization and its external stakeholders -- customers, vendors, other third parties, etc. More importantly, an IS can provide consistent and up-to-date data for analysis, which enables companies to understand market trends and customer needs and to design new products and services to meet those needs.
The right kind of IS also provides the information and insights that businesses need to optimize existing operations, manage HR, implement processes to improve customer experience and employee experience, and more. It can also enable organizations to explore new business models and opportunities, such as e-commerce, social media and artificial intelligence (AI).
Well-designed information systems play a critical role in enterprise decision-making. ISes also support knowledge management, which is essential to help employees find the information they need to do their jobs and make valuable contributions to their department and organization with their work and skills.
How does an information system work?
An IS is a powerful system that brings many different components together. In doing so, it enables organizations to collect, store, process and distribute information efficiently and for a variety of purposes. Some ISes also provide dashboards and produce human-friendly reports in predefined or customizable formats. The reports may include textual information, as well as graphics and useful data visualizations, to simplify data analysis and facilitate decision-making.
Most information systems follow these steps to transform raw data into useful information and insights:
- Accept input from one or more sources. The system collects data that acts as the input for all downstream functions. Many information systems collect data from multiple sources. The data may be structured (names, contact information, financial transactions, dates, etc.) or unstructured (images, videos, internet of things sensor data, chat logs, etc.)
- Process input data. Depending on its capabilities, the IS cleans the raw data to improve its accuracy and consistency. It may also apply other operations, like classification, labeling and analysis, to transform the raw data into meaningful information valuable for human decision-making.
- Produce output in user-friendly format. The IS presents the processed information as insights to users. These insights are typically presented in a user-friendly format, such as reports, graphs, charts and dashboards, enabling users to take action on the data without getting overwhelmed by data analysis and output formatting.
- Store the processed data. The IS stores the processed information in a predetermined data storage component, such as an on-premises database or the cloud. Users can retrieve the stored data as needed for their specific requirements.
Some ISes also include features to collect user feedback. The IS designers can use this feedback to evaluate IS performance and determine where improvements are needed to its design and functionality.
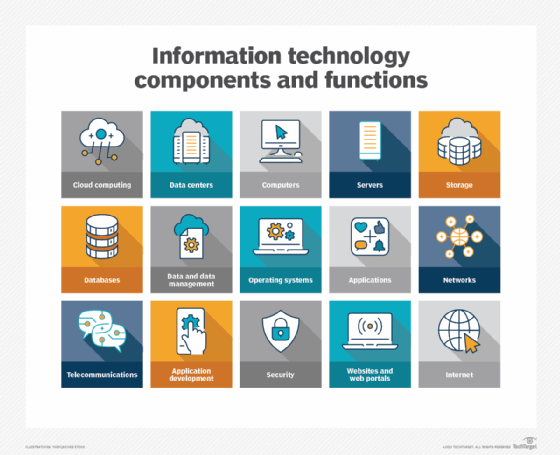
Typical components of information systems
An IS is composed of a variety of components, with each component playing an important role in the overall functioning of the system:
- Data is the most important component of any IS. It may be structured or unstructured, depending on the IS type, capabilities and use cases. Users can access this data and insights via dashboards, reports, visualizations, etc. for analysis and decision-making purposes.
- Hardware includes computers and servers. Computer hardware is essential for providing users with access to the IS, while servers facilitate data processing and provide access to storage space for the system's data, programs and applications.
- Networks such as local area networks, wide area networks, intranets and cloud networks are important for interconnecting different components, facilitating communication between them and enabling users to access the IS from anywhere in an organization -- and, in some cases from remote locations.
- Software. Operating systems (OSes) are needed to ensure that the IS operates as needed and produces expected output. Databases, data lakes and other storage components are needed to store and retrieve information from the IS. The IS may also include different software applications and large software packages for specific tasks or processes. These software products may be deployed on-premises or in the cloud as software as a service.
- People play a key role in any IS. These include administrators who manage the system, management personnel who make decisions about IS investments and deployments, and end users who interact with the IS to perform tasks and get work done.
- Business processes, as well as processes governing information collection, processing and storage, are critical for IS effectiveness. To ensure that the IS is used properly and securely and delivers the best possible outcomes, enterprise and IT leaders must define procedures for setting up secure user accounts, controlling data access, creating data backups and maintaining compliance with data privacy regulations.
Managing information systems
To effectively manage and maintain an IS, IS professionals must understand the system's capabilities and be aware of the needs and requirements of the businesses and users that rely on it. They must also understand the following aspects:
- Security. As with any technology-enabled or internet-connected system, information systems are also vulnerable to cyberthreats, like hacking, viruses, malware and unauthorized access. This is why IS administrators must make an effort to boost IS system and data security. They can do this by implementing extensive security tools and measures, like access control, firewalls, intrusion detection systems, intrusion prevention systems, antivirus and data encryption.
It's also crucial to apply security patches and updates as they become available to fix vulnerabilities and prevent their exploitation by threat actors. Additionally, regular security audits, vulnerability assessments and penetration testing can reveal potential security risks before they can result in damaging attacks or data breaches. - Data management. Proactive and ongoing data management is needed to maintain the accuracy, consistency and integrity of the data stored in the IS. IS administrators must implement data backup processes to prevent data loss in case of system failures or disasters. Admins must also ensure that data is stored in a structured and organized manner so that it can be easily accessed and analyzed as needed.
- Network management. IS administrators must implement systematic network management processes to monitor and maintain the IS network infrastructure. They must ensure that network devices -- routers, switches, servers, etc. -- are correctly configured, network traffic is managed properly to avoid congestion and delays, and network security measures, like firewalls, to block malicious traffic and prevent unauthorized access are implemented and maintained.
- System updates and upgrades. IS administrators must regularly update and upgrade the IS and implement a patch management process to ensure that all components in the IS continue to run smoothly. They must also monitor system performance metrics, such as CPU and memory usage, to identify and troubleshoot performance issues as early as possible.
- User support. IS administrators must provide the necessary training and job-appropriate data so users can use the system effectively. Help desk support is also useful in assisting users with troubleshooting problems. Easy access to a knowledge base with articles, FAQs and chatbots can also help resolve user queries without overburdening the help desk team.
Information system jobs and education
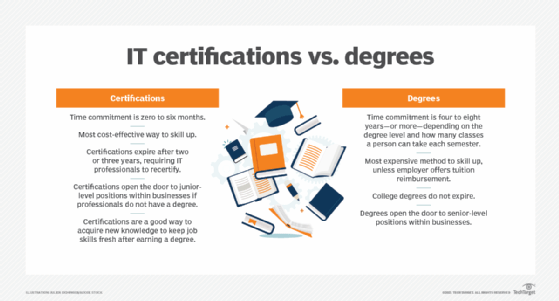
IS jobs are in high demand across a variety of industries. Professionals in this field should ideally have a combination of technical, business and communication skills, as well as an understanding of the components and processes associated with ISes. Most companies require applicants for IS positions to hold a bachelor's degree or higher in computer science or a related field, like software engineering or IT.
Many employers also prefer candidates who have obtained IT certifications, especially if the job opening is specific to security or networking. Some seek candidates experienced in cloud computing due to the popularity of services like Amazon Web Services, Google Cloud and Microsoft Azure. In addition, security knowledge is perennially in high demand due to the expanding threat landscape affecting the performance and integrity of information systems.
IS job opportunities abound, varying from entry-level positions, like support technicians, to higher positions, like senior engineers or system architects. Other potential career paths include application developer, database analyst and administrator, IT consultant, BI specialist and systems integrator. Areas of ISes in high demand in today's job market include automation technologies, such as robotic process automation, AI and machine learning engineering.
For those interested in pursuing an IS degree, colleges and universities offer a variety of programs, ranging from associate degrees to doctoral courses of study. These typically cover topics such as system architecture, OSes, databases and data structures, networking, security, cloud computing, project management, programming and software development. Individuals enrolled in these programs can expect to learn computer programming languages, database management and data analysis techniques, network design and security principles, system development methodologies, BI tools and techniques, project management principles, change control processes, user interface design principles and software engineering practices.
Information system and other similar-sounding terms
The term information system is often used interchangeably with computer system. While these categories do have some overlaps, they are not necessarily the same. Computer systems are a crucial part of any IS; however, they do not encompass all the components that make up an IS, such as people, processes and procedures.
Information technology also sounds similar to information system. However, IT focuses on the technical or technological aspects of the hardware and software used in enterprise computing. IT professionals are mainly concerned with implementing, maintaining and troubleshooting the IT systems needed to support business processes and meet business needs. They may not have a deep or broad understanding of these processes and needs.
In contrast, information systems and IS professionals do have an understanding of the underlying business imperatives driving the need for ISes. Information systems are also concerned with how the people within an organization use various IT systems and data to manage operations, make decisions, engage with customers, and compete in the market and industry.
Explore the differences between operational technology vs. information technology. Also, a large part of the decision to use a systems management service depends on the capabilities of the company's IT team. One type of systems management is server management. Learn the most important skills a server engineer needs to monitor, maintain and manage servers.
