Pegasus malware
What is Pegasus malware?
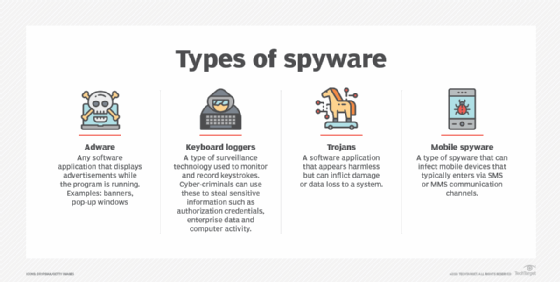
Pegasus malware is spyware that can hack any iOS or Android device and steal a variety of data from the infected device, including text messages, emails, key logs, audio and information from installed applications, such as Facebook or Instagram. The spyware can record conversations and videos and snap pictures from the device's camera. The malware was created by NSO Group, an Israeli cybersecurity firm that was founded in 2010 and has been around since at least the summer of 2016.
What is Pegasus spyware used for?
Threat actors can use Pegasus to stealthily gather information from high-value targets, including executives with strategic corporate information and government officials with access to national or international secrets.
As the Pegasus malware price is said to be very expensive, it's not used to spy on the general public.
How does Pegasus malware work?
A Pegasus attack starts with a simple phishing scheme: The attacker identifies a target and then sends that target a website URL via email, social media, text message or any other message.
In the case of Pegasus iOS malware, once the user clicks on the link, the malware secretly carries out a trio of zero-day exploits against the victim's iPhone, jailbreaking it remotely so the spyware can be installed.
The only indication that something has occurred is that the browser closes after the user clicks the link. There's no other indication that anything has happened or that any new processes are running.
Once Pegasus is installed, it begins contacting the operator's command and control servers to receive and execute the operator's commands.
The spyware contains malicious code, processes and apps that spy on what the user does on the device, collects data and reports what the user does. The malware can access and exfiltrate calls, emails, messages and logs from applications, including Facebook, X, Instagram, Facetime, Gmail and WhatsApp.
Once the spyware jailbreaks the user's device, it compromises the original apps already installed on the device to capture data rather than download malicious versions of these apps. Jailbreaking gives the malware more extensive control over the target's phone.
Pegasus for Android doesn't require zero-day vulnerabilities to root the target device and install the malware. Instead, the malware uses a well-known rooting technique called Framaroot.
With Pegasus for iOS, if the zero-day attack execution fails to jailbreak the device, then the overall attack sequence fails. However, the hackers' built-in functionality for the Android version still enables Pegasus to ask for permissions to access and exfiltrate data if the initial attempt to root the device is unsuccessful.
History of Pegasus
Pegasus was first discovered by Ahmed Mansoor, a human rights activist in the United Arab Emirates (UAE). On August 10 and 11, 2016, Mansoor, now imprisoned in the UAE, received SMS text messages on his iPhone that promised he would receive new information about individuals tortured in UAE jails if he clicked on the link in the messages.
However, Mansoor didn't click on the link. Rather, he sent the messages to researchers at the Citizen Lab, an organization based at the University of Toronto. The organization produces evidence-based research on cybersecurity issues associated with human rights concerns. The group's research includes investigating digital espionage.
The researchers recognized that the links belonged to an exploit infrastructure connected to the NSO Group, which sells Pegasus and other spyware to governments known for human rights violations to spy on critics and activists.
When information about the iOS version of Pegasus was first released, Apple issued an iOS security update that patched the three vulnerabilities, including two zero-day vulnerabilities. Google helped researchers investigate the case with the Android version and notified potential Pegasus targets directly. Google claimed that just a few dozen Android devices had been infected.
In 2018, an Amnesty International staff member received a suspicious WhatsApp message that included a link that, had it been clicked, would have installed Pegasus on the employee's mobile device. WhatsApp ultimately patched the flaw that would have allowed an attacker to infect a victim's device with the spyware.
Who uses Pegasus?
NSO Group claims to sell its surveillance software exclusively to governments to help them fight terrorism and serious crime. However, it's important to note that verifying its users can be difficult because the company is highly secretive about its sales, and evidence often comes from investigative reporting and leaked data.
Its spyware, including Pegasus, has been licensed to dozens of countries, including Azerbaijan, Bahrain, Djibouti, India, Mexico, Saudi Arabia and the UAE.
Governments worldwide have used Pegasus to target activists, including the Amnesty International employee, Saudi activists, Mansoor, at least 24 human rights defenders, journalists, parliamentarians in Mexico, and allegedly murdered Saudi journalist Jamal Khashoggi, according to a lawsuit filed in 2019 by Amnesty International and other groups demanding that the Israeli Ministry of Defense revoke the export license of NSO Group.
How do you detect if your phone has Pegasus malware?
Detecting Pegasus infection is complicated. This is because Pegasus spyware is designed to be stealthy. There are some signs that can indicate a potential issue, but they are far from conclusive.
Although not guaranteed, unusual device behavior, battery drain, overheating and unexplained data usage can suggest a potential infection. Mobile apps experiencing glitches, especially messaging apps like WhatsApp and Telegram, which are known to be targeted by spyware, can indicate a possible infection.
How to remove Pegasus malware from your phone
If a user thinks their mobile device is infected with Pegasus spyware, they may consider using the Mobile Verification Toolkit by Amnesty International to contain and remove it. However, this requires considerable technical expertise and may not be foolproof.
A high-value target can consider engaging a cybersecurity professional to initiate a thorough investigation and formulate a solution.
Spyware can steal routine information, track people's every move and more. Learn more about the types of spyware and how to best fix infected devices.






