What are the top 10 spyware threats?
The top 10 spyware list describes the most common spyware threats behind famous spyware attacks and is frequently identified by leading antispyware tools from vendors like Webroot, Norton and Malwarebytes.
What is spyware?
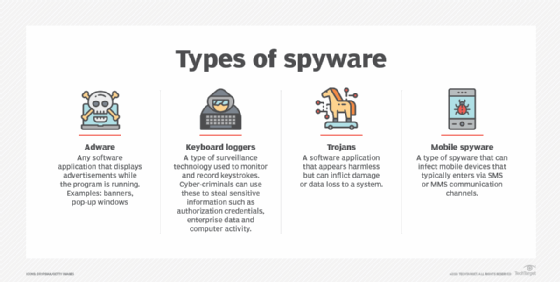
Spyware refers to malicious software purposely designed to access a computer and record its activity. Spyware can track and record a user's browsing habits, login credentials, passwords and more. The spyware author uses the information obtained in this data breach to engage in fraudulent activity or might sell it to a third party.
Spyware often spreads through phishing emails, malicious downloads, fake apps or compromised websites. Once installed, it can run in the background logging keystrokes, capturing screenshots or transmitting sensitive data.
Visit our spyware feature page to learn more about this problem and how to beat it.
The top 10 spyware threats
Some of the top spyware threats organizations face today, according to security experts, include the following:
1. Advanced Keylogger
Advanced Keylogger, a keystroke logger, monitors keystrokes and takes screenshots.
2. CoolWebSearch (CWS)
CoolWebSearch (CWS) is a software suite originally used to exploit vulnerabilities in Internet Explorer (IE), which Microsoft officially retired in 2022. Though now considered outdated, CWS remains historically significant as one of the earliest, most aggressive examples of browser hijackers. It could rewrite search engine results, redirect DNS lookups and change browser settings to push users toward ad-laden pages.
3. FinSpy (aka FinFisher)
FinSpy, or FinFisher, is an advanced suite of surveillance tools sold to law enforcement and intelligence agencies. FinSpy works on Windows, macOS, Linux, Android and iOS operating systems. Its capabilities vary depending on the platform. Law enforcement, intelligence agencies and threat actors often use FinSpy to secretly turn on microphones to record conversations, switch on cameras, record and transmit images, transmit key logs in real time, modify files and more.
4. Gator (GAIN)
Gator is a type of adware that can display banner advertisements based on a user's web surfing habits. Gator is often bundled with numerous free software programs and pirated applications. Gator monitors online user behavior and targets them with personalized ads.
5. GO Keyboard
GO Keyboard was a virtual Android keyboard app that masqueraded as a legitimate mobile application. It was found to transmit personal information to its remote servers without explicit user consent, violating Google Play policies. The app was eventually removed from the Google Play Store, but it serves as a cautionary example of the risks posed by third-party keyboard apps.
Information shared by GO Keyboard spyware included the following:
- Android OS version.
- Device model and screen size.
- Google account email address.
- International Mobile Subscriber Identity (IMSI).
- Location.
- Network type.
- Preferred language.
- Social media interactions.
GO Keyboard executes code from a remote server to breach Google Play privacy policies.
6. HawkEye
HawkEye, a keylogger virus, was dormant for years but resurfaced during the COVID-19 pandemic. It infects machines to track key logs and other inputs, sharing that information with a remote server. New versions are increasingly difficult to detect due to enhanced anti-detection features. One campaign impersonated the World Health Organization in a social engineering attack designed to trick users into downloading a malicious attachment.
7. HuntBar
HuntBar is a Trojan application that hijacks web browser settings and downloads and installs adware without the user's knowledge. Also known as Adware, Websearch or WinTools, HuntBar tracks browsing behavior, redirects web traffic to affiliate websites, forcefully displays advertisements and installs more spyware programs and toolbars on IE.
8. Look2Me
Look2Me is spyware that tracks user behavior, website logs and social media interactions and shares this information with a remote server. The information is then used to show intrusive advertisements. Look2Me spyware also downloads and installs various add-ons, extensions, toolbars and other unwanted programs on a user's computer. This makes the spyware threat more dangerous than traditional adware. Removing Look2Me is difficult because of its rootkit-type functionality.
9. Pegasus
NSO Group's Pegasus spyware is one of the latest spyware threats making headlines. Although Pegasus was initially developed to fight terrorism, evidence suggests that many clients use Pegasus to spy on journalists, political activists, political opponents and almost anyone the client desires. The governments in France, Hungary, India, Saudi Arabia, United Arab Emirates, the United Kingdom and the United States are known to have used Pegasus spyware.
10. PhoneSpy
PhoneSpy is an example of a spyware virus that pretends to be a mobile application to gain access to and infect Android mobile devices. This approach allows threat actors to remotely control mobile devices and steal data. Mobile applications with PhoneSpy aren't available on Google Play Store, so it's believed to spread through social engineering attacks and third-party platforms.
Emerging mobile spyware threats
As mobile device usage continues to rise, threat actors have increasingly turned to smartphones as high-value targets. Here are a few of the most concerning mobile spyware threats discovered in recent years:
Hermit
Hermit is a powerful mobile spyware tool designed to infect both Android and iOS devices. Typically delivered via fake mobile carrier apps or malicious links in SMS messages, Hermit can record audio, track location, intercept texts and access contact lists. It has been linked to state-sponsored surveillance campaigns targeting journalists and political figures.
SpyNote
SpyNote is a remote access trojan (RAT) that targets Android users. Once installed, it allows attackers to record audio, access text messages and call logs, and even activate the device's camera without user consent. SpyNote is often disguised as a legitimate app and distributed through unofficial app stores or phishing links.
Anatsa (also known as TeaBot)
Anatsa is a banking Trojan with spyware-like capabilities. It has been known to steal login credentials by capturing keystrokes and recording screen activity on Android devices. Anatsa spreads through fake app downloads posing as QR code readers, PDF viewers or security apps.
How to protect yourself from spyware
Spyware can be difficult to detect until it's already compromised your device. Here are simple best practices to help reduce the risk of infection:
- Use reputable antivirus and antispyware software and keep it up to date.
- Avoid downloading apps or files from untrusted sources, especially third-party websites.
- Enable automatic software updates on your devices to patch known vulnerabilities.
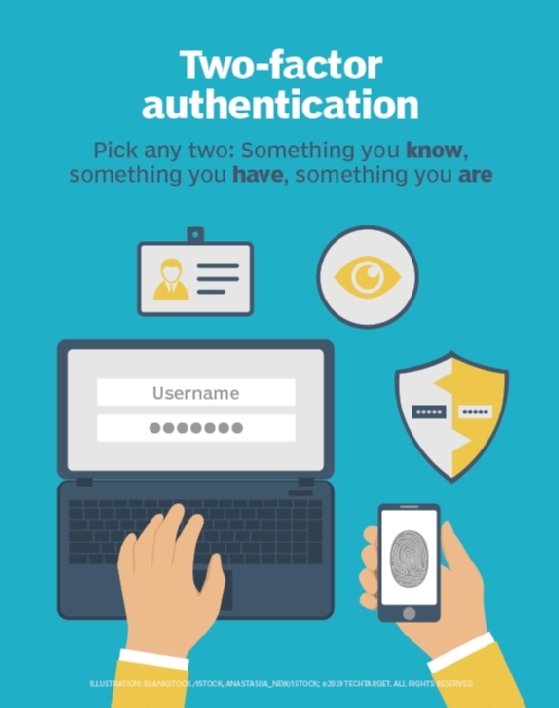
- Use strong, unique passwords and turn on two-factor authentication (2FA) for sensitive accounts.
- Be cautious of phishing emails and attachments, especially those with urgent or alarming messages.
- Review app permissions before installing, particularly for mobile apps that request access to contacts, location or cameras.
Staying alert and maintaining good digital hygiene can significantly lower your risk of falling victim to spyware.
FAQs about spyware threats
- Can spyware infect mobile devices?
Yes. Spyware is increasingly targeting mobile devices through fake apps, malicious links and phishing messages. Android devices are especially vulnerable when apps are downloaded from third-party sources. - What is the most dangerous spyware in 2025?
Pegasus remains one of the most sophisticated spyware tools in use. However, newer threats like Hermit and Anatsa are also highly capable and dangerous, especially on mobile platforms. - How do I know if my device has spyware?
Common signs include unexpected battery drain, overheating, slow performance, unknown apps appearing, and unusual network activity. If you suspect spyware, run a trusted mobile security scan and review app permissions. - Is Pegasus spyware still active?
Yes. While originally marketed for counterterrorism, Pegasus has been used by various governments and entities for broader surveillance. It remains a high-profile threat and continues to evolve.
Learn more on how to prevent spyware through best practices, including using a layered defense or content filtering. See how to protect against malware as a service. Also, protecting your endpoints is critical for maintaining security. Learn why endpoint detection and response technologies are essential for endpoint protection. Explore how to protect, detect and remove malware from mobile devices.