What is a robot? Definition, purpose, uses
A robot is a type of automated machine that can execute specific tasks with little or no human intervention and with speed and precision. There is no "standard" robot, meaning robots can be of different sizes and shapes, do different things and operate in different environments.
The field of robotics, which deals with robot design, engineering and operation, has advanced remarkably in the last 50 years. Today, robots are operating in homes, offices, factories and other places to do everything from cleaning floors, adjusting ambient temperatures and taking high-resolution aerial photographs, to assembling products in factories, detecting landmines, fixing underwater pipe leaks and even exploring the surface of planets.
In 2016, IDC identified robotics as one of six innovation accelerators driving digital transformation.
Robotics continues to drive digital transformation in organizational and other commercial settings. The worldwide robotics market volume is expected to grow at a healthy compound annual growth rate (CAGR) of 9.49% (2025-2029) to top $73.01 billion by 2029, according to Statista, a data and business intelligence company. Some of the chief drivers for the increasing value of this market will be countries' GDP growth, labor shortages and inflation.
How do robots work?
Despite differences in their physical characteristics and operational capabilities, all robot systems automate certain tasks by doing three things:
- Sensing the operational environment.
- Performing calculations that will assist them in making decisions.
- Acting autonomously and with minimal human input.
To sense the environment, robots use sensors and other devices. Sensors detect specific aspects of an environment and transmit a signal to the robot. On receiving this signal (which is often sent in real time or near real time), the robot performs the actions it's supposed to perform.
Different kinds of sensors are used, depending on the robot's environment and application. For example, in a product manufacturing or assembly environment (factory), robots might use sound sensors that enable the robot to carry out certain tasks in response to a specific sound or series of sounds.
Another example might be a robot that works in extreme temperatures and assists with construction or ecological restoration. It might be set up with a temperature-sensing sensor so that when it detects temperature changes in the environment, it sends the information to the robot so that the robot can respond accordingly.
Similarly, obstacle avoidance robots, commonly used in self-driving vehicles, parking assist systems and industrial automation typically use contact or touch sensors. These sensors detect obstacles so the robot can adjust its movement to avoid the obstacle and continue functioning uninterrupted.
Robots perform calculations by means of a control system. The construction of the control system, also known as the central processing unit (CPU), varies depending on the robot's application. Some robots use a simple electronic circuit as the CPU, while others use advanced multicore processors. For the most powerful, large-scale or complex robots, the CPU may be an entire network of interconnected computers that work together to facilitate the robot's operation.
Regardless of the CPU size or capability, its job is to tell a robot how to complete a specific task. It does this by sending appropriate and timely signals to the robot. On receiving the CPU's signal, the robot starts moving or moves other things, depending on what it's been programmed to do.
To qualify as a robot, a device must have a movable frame with an actuator that facilitates the movement of the frame. An actuator receives the signal from the CPU and then converts this energy into physical motion. The various motors that make the actuator move in tandem to help the robot move and carry out tasks like navigation, spinning, pushing, pulling and so forth.
Some robots may also have end effectors, external components that robots need to finish a task. Examples of end effectors include scalpels, drills, paint sprayers and gripping claws.
The sense-compute-act process is known as a feedback loop. It is a cyclical process that allows robots to operate continuously and carry out their tasks.
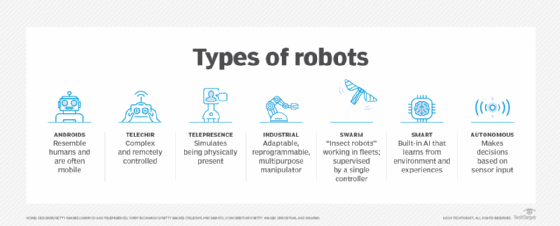
Some robots work autonomously, meaning they operate independently of human operators. They use sensors and computers to recognize the environment and make decisions about next actions. Other robots are human-controlled. These teleoperated robots are often used in dangerous, inaccessible or remote environments like deserts, nuclear plants, deep sea, rubble-filled locations and outer space. Wireless networks are usually needed to enable human users to operate these teleoperated robots from a safe distance.
What can robots do?
Essentially, there are as many different types of robots as there are tasks for them to perform. Robots can perform some tasks better than humans, but others are best left to people
Some of the things that robots do better than humans include the following:
- Automating manual or repetitive activities in corporate or industrial settings.
- Working in unpredictable or hazardous environments to spot hazards like gas leaks.
- Processing and delivering reports for enterprise security.
- Filling out pharmaceutical prescriptions and prepping IVs.
- Delivering online orders, room service and supplies during emergencies.
- Assisting during surgeries.
Robots can also make music, monitor shorelines for dangerous predators, help with search and rescue and assist with food preparation.
In general, the tasks performed by a robot might be specific and narrow, meaning the robot is programmed to perform only those tasks. An example is Roomba, the robotic vacuum cleaner that can only vacuum floors. Similarly, gardening robots, welding robots and parts transfer robots all have a very narrow scope of work. For instance, a gardening robot may be built only to pull up weeds. It cannot prepare the soil, plant seeds or water plants. Similarly, a welding robot can only weld together small parts or subassemblies. It cannot sort parts, generate 3D prints or transport materials within the factory or warehouse.
Other robots are more versatile and can do many different things. For example, Spot by Boston Dynamics is a four-legged robot that can perform a variety of tasks in many different environments like construction sites, agriculture, factories, rough terrain and search and rescue operations in disaster zones. Unitree's B2 is another multipurpose quadruped robot. Described as the "fastest running industrial-grade quadruped robot" by the manufacturer, B2 is built for use in different kinds of industrial applications, including factories, warehouses and construction sites.
Types of robots
Among the many different types of robots and the tasks they can accomplish are:
Androids
Androids are robots that resemble humans in some way, either physically or behaviorally or both. They are often mobile, moving around on wheels or a track drive. The word android is rooted in two Greek words: andro meaning man and eides meaning shape. These humanoid robots are used in a wide range of areas, which include the following:
- Caregiving.
- Home and personal assistance.
- Search and rescue.
- Space exploration and research.
- Entertainment and media.
- Education.
- Public relations.
- Customer service.
- Medical and surgical procedures.
- Manufacturing automation and industrial control systems (ICS).
- Hospitality.
- Disaster response and emergency services.
Over the years, many famous Android robots have emerged in the real world. These robots include the following:
- Sophia. Sophia is a female-type android social robot developed by Hanson Robotics and first released in 2015. According to the company web page, she is "an agent for exploring human-robot experience in service and entertainment applications."
- Kebbi. This android, developed by Nuwa Robotics for use in social settings, includes voice intelligence and can use expressive gestures so users can engage in interactive experiences with this human-like machine. The robot can also answer queries, recommend content and teach languages and programming. Kebbi can be personalized to match a user's specific experience requirements.
- Atlas. Atlas is a fully electric robot for real-world applications from Boston Dynamics. This Android includes built-in athletic intelligence that enables it to adapt to changing and ongoing situations. It also has a full range of motion so it can mimic human movements and meaningfully interact with the world.
- Ameca. Ameca from Engineered Arts is an advanced human shaped robot for human-robot interaction. It can also be used as a platform to develop future robotics technologies.
As use cases and applications increase significantly, humanoid robotics startups are getting a lot of attention from the investor community. According to the research firm Research and Markets, these firms amassed about $7.2 billion in investment in 2024. The Android market is poised to hit $13 billion by 2026. Morgan Stanley estimates that by 2050, the humanoid market could surpass $5 trillion and the number of humanoid robots used for industrial and commercial purposes could surpass 1 billion.
Telepresence robot
A telepresence robot is a complex robot that can be remotely controlled by a human operator. It simulates the experience -- and some capabilities -- of being physically present at a location. Also, it continuously provides sensory feedback so users can interact with it in meaningful ways to achieve their objectives.
These robots combine remote monitoring and control via telemetry sent over radio, wires or optical fibers. Additionally, they include components that enable the robot and human operators to interact, such as a video camera, a screen, a tablet, a phone, speakers and a microphone.
Telepresence robots are most commonly used in inaccessible, remote, alien or dangerous environments, acting as the eyes and ears of humans who cannot (or should not) go into those environments. These robots are also useful in many other environments, such as the following:
- Schools.
- Hospitals.
- Factories.
- Offices.
- Warehouses.
- Museums.
- Stores.
- Social settings.
Industrial robot
The International Federation of Robotics (IFR) and the International Organization for Standardization (ISO) both define an industrial robot as an "automatically controlled, reprogrammable multipurpose manipulator programmable in three or more axes, which can either be fixed in place or fixed to a mobile platform for use in automation applications in an industrial environment."
These robots can be reprogrammed without requiring physical alterations and can be adapted for different applications as well. The robots consist of some arrangement of segments that are joined to or sliding relative to each other. Finally, they can move in either linear (along two axes) or rotary mode (along three axes).
There are many types of industrial robots, including Cartesian robots, SCARA robots, articulated robots, parallel robots, cylindrical robots and polar robots.
Combining these robots with AI in industrial settings has helped businesses move beyond the automation of simple repetitive tasks to the automation of higher-level and more complex tasks that previously relied on human labor, including product assembly lines, dispensing and quality control.
The robot-AI combination enables manufacturing organizations to:
- Optimize process performance.
- Automate production to increase productivity and efficiency.
- Speed up product development.
- Enhance safety.
- Lower costs.
According to IFR's World Robotics 2024 report, there were over 4 million industrial robots operating in factories worldwide, a 10% increase over 2023. A majority of the robots newly implemented in 2023 were deployed in Asia, with China and Japan being the largest markets, followed by Europe and the U.S.
Swarm robot
Swarm robots (aka insect robots) work in fleets ranging from a few to thousands, all under the supervision of a single controller. These robots are analogous to insect colonies, in that they exhibit simple behaviors individually, but when working together demonstrate behaviors that are more sophisticated with an ability to carry out complex tasks.
Swarm robots are very useful in construction, agricultural and medical environments, as well as applications such as the following:
- Search and rescue.
- Environmental monitoring and remediation.
- Chemical spill cleanups.
- Pest control.
- Military operations.
- Space exploration.
- Package delivery.
Smart robot
A smart robot is the most advanced kind. Gartner defines it as "an AI-powered, often-mobile machine designed to autonomously execute one or more physical tasks."
Unmanned autonomous vehicles (UAVs) -- also known as drones -- are a type of smart robot. A drone is a flying robot, used in a wide range of applications, including agriculture, construction, logistics, e-commerce, search and rescue, law enforcement, infrastructure, environmental conservation and aerial photography. Smart robots can also be automated mobile robots (AMRs), collaborative robots (cobots) or articulated robots.
These robots have a built-in AI system that learns from its environment and experiences to build the robot's knowledge and enhance its capabilities. As its capabilities improve, a smart robot can operate autonomously and perform its given tasks with increasingly higher efficiency and accuracy. Also, smart robots can interact with humans and help solve problems in numerous personal, logistics and industrial areas, including the following:
- Agricultural labor shortages.
- Food waste.
- Study of marine ecosystems.
- Infrastructure inspection.
- Emergency response.
- Product organization in warehouses.
- Clearing debris from disaster zones.
Medical robot and agricultural robot
These robots are specifically designed to work in medical and agricultural environments.
Medical robots perform a variety of tasks, such as transporting medical supplies, dispensing prescription drugs to patients and assisting with surgeries on the human body. Some robots can also assist with physical therapy, generate content in natural language and perform clinical administration and management. Advanced medical robots use AI and machine learning to complete tasks, learn from those tasks and improve their capabilities over time. AI also allows these robots to adapt to workflows and make independent decisions.
Agricultural robots can operate in farms and greenhouses, helping farmers and gardeners with labor-intensive or repetitive tasks such as crop harvesting, fruit picking, mowing, weeding, plant monitoring and environmental monitoring and control. Through automation and autonomous operation, these robots help to mitigate the twin challenges of labor shortage and increasing food demand.
Service robot
Service robots perform useful tasks for humans or equipment. These tasks might be repetitive, time-consuming or hazardous. The robots might be used in both personal and professional settings and can often work autonomously with minimal or no human input.
Service robots are used to simplify tasks in many areas. Some examples are listed below:
- Hospitality.
- Healthcare.
- Homes.
- Warehouses.
- Logistics.
For example, a service robot might be used in the home to clean floors and in a warehouse to move goods. Service robots can also be used to deliver packages, help with visitor or guest management in airports, malls, hospitals, etc., or to perform routine checks and maintenance on manufacturing equipment.
Limitations of robots
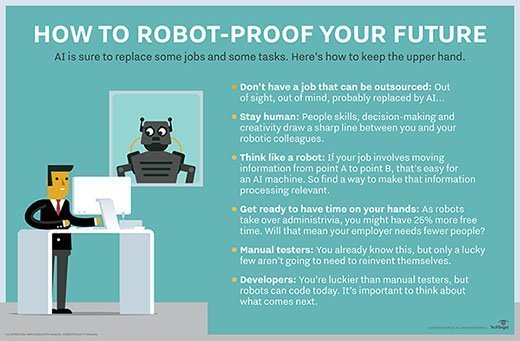
Despite their increasing ubiquity and many advantages, there are several shortcomings to using robots:
- While they can perform surgeries, they cannot soothe scared patients.
- Robots can sense furtive footsteps in a closed-off area, but not take action against gate-crashers.
- They can lead exercise sessions for the elderly, but not ease their loneliness.
- They can help medical professionals with diagnoses, but not empathize with patients.
- Robots can learn from data, but not find creative solutions to unexpected situations.
Another challenge is that robots pose data security risks. Since many modern robots are now connected to the internet or part of highly interconnected internet of things (IoT) networks, they are vulnerable to cyberattacks like malware, ransomware and man-in-the-middle (MitM) attacks that can disrupt operations, cause data breaches or damage an organization's finances and reputation.
Furthermore, robots can be expensive to maintain and repair. They can also contribute to environmental waste and pollution.
Robots -- like other technologies such as AI -- might eliminate some jobs. This raises concerns among human workers about the potential threat of robots to their livelihoods.
While robotics technology has advanced to such a degree that robots can now automate simple or complex tasks in both predictable and unpredictable, human-dependent areas, the fact remains that robots do depend on human programming to function well, and it's likely they always will.
Common characteristics of robots
Not all robots look like HAL 9000 in 2001: A Space Odyssey or BigDog, the rough-terrain quadruped robot with complex sensors, gyroscopes and hydraulic actuators from Boston Dynamics. Some have human-like features (androids), while others are all mechanical limbs. Still others look like keychains or whizzing toys.
Nonetheless, all robots have some common characteristics, such as the following:
- Mechanical construction. The mechanical parts of a robot include arms, wheels, tubing, pistons, gears and motors that allow the robot to move (or make other things move).
- Electrical components. These parts include actuators, sensors, power supplies, resistors and capacitors that provide the electrical energy needed for the robot to perform its tasks.
- Computer programming. The robot's CPU and control software take in information from sensors and send the signals to the mechanical components. These signals determine what decisions the robot makes and how it acts in real-world settings.
As AI and software advance, robots will become smarter, more efficient and will take on more complex challenges.
Robotic process automation and intelligent process automation
Robotic process automation (RPA) technology involves the design, deployment and use of software-based robots to accomplish tasks, such as the following:
- Automating rules-based business processes.
- Streamlining enterprise operations.
- Saving human effort.
- Lowering costs.
RPA automates repetitive tasks so human personnel can focus on higher value work. Use cases can be simple, such as automated email responses, or complex where thousands of functions are automated.
RPA is a steppingstone to more advanced intelligent process automation (IPA). IPA adds decision-making capabilities, AI tools and cognitive technologies like natural language processing and machine learning.
Robots and robotics: A short history
The 1921 play, R.U.R., which stands for Rossum's Universal Robots, by Czech writer Karel Capek, first introduced the word robot. These robots were artificial people rather than machines and could think for themselves, so they are somewhat similar to modern androids. Isaac Asimov said that Capek contributed the word robot to all languages in which science fiction is written. Asimov introduced the word robotics and his famous Three Laws of Robotics in his story Runaround.
The first robots -- although they weren't called that at the time -- actually date back several centuries before R.U.R. In 1478, Leonardo da Vinci designed a self-propelled car which is still considered influential for robotic designs. While da Vinci's autonomous system didn't make it past the drawing board, in 2004 a team of Italian scientists replicated its design as a digital model, proving that it works.
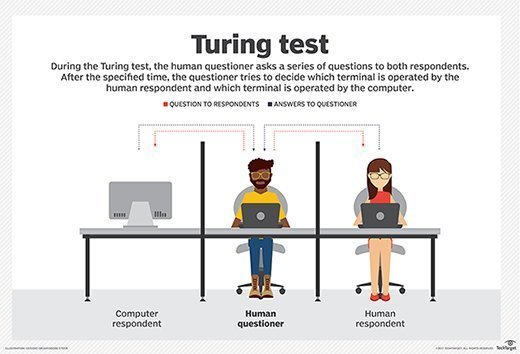
In 1950, English computer scientist Alan Turing developed the Turing Test, originally called the Imitation Game, that laid the foundation for further research into artificial intelligence and robotics.
Stanley Kubrick's 2001: A Space Odyssey presented one of the world's earliest AI robots, the HAL 9000. HAL recognized speech, understood natural language and even won chess games. Now a part of Carnegie Mellon University's Hall of Fame, HAL still inspires scientists to look for ways to duplicate its 1960s imagined capabilities.
In the 1950s, George C. Devol invented a reprogrammable manipulator called Unimate. Engineer Joseph Engleberger acquired Devol's robot patent and converted his design into the world's first industrial robot. He eventually earned the label, The Father of Robotics.
In 1966, MIT developed one of the earliest AI-based bots, Eliza, while SRI International later designed Shakey, a self-directed robot for specialized industrial applications. By the early 1970s, scientists had successfully integrated AI bots into medicine with MYCIN to help identify bacteria and INTERNIST-1 computer-based diagnostic tool. ALVINN, the robotics tech that powers today's self-driving cars, was developed in the 1980s.
The Tramp foresees the robot's rise
'Don't give yourselves to these unnatural men -- machine men with machine minds and machine hearts! You are not machines, you are not cattle, you are men! You have the love of humanity in your hearts!'
-- Sir Charlie Chaplin, The Great Dictator
In 1940, Sir Charlie Chaplin probably had no idea that the inexorable rise of machines was just a few decades away. Over 80 years later, automated robots are now used in manufacturing, industrial supply chains, agriculture, financial services, education and more.
By the 1990s, consumer-facing bots appeared as computer games like Tamagotchi. In the years after 2000, interest in robots and robotics increased substantially with the release of SmarterChild, a programmed bot within AOL Instant Messenger that's now considered the forerunner AI to Apple's Siri.
In the early 2000s PackBot, a military robot, and Stanley, a vehicular bot, were both invented. Notably, PackBot played an important role in the aftermath of the 9/11 attacks, as first responders sent the robot into the rubble to search for victims and assess the structural integrity of the debris. PackBot sent back pictures from hard-to-reach places, helping with rescue efforts.
The PackBot inspired a new era of robotics, accelerating the development of more advanced, autonomous machines that now help in areas such as the following:
- Disaster management.
- Law enforcement.
- Weather forecasts.
- Residential hygiene.
- Military reconnaissance.
Today's robots can carry out a number of complex tasks that would have been considered science fiction even half a century ago. Intelligent robots are now collaborating with humans and helping to solve problems that looked unsolvable in the past.
In recent years, robots have started moving from the realm of experimentation to commercialization. Companies are developing different types of robots for a wide variety of applications. These include medical robots, agricultural robots, and augmented or virtual reality robots.
These machines are constantly improving, performing a variety of complex tasks that were previously performed only by humans. In fact, many robots are now working alongside humans. For example, some medical robots can assist surgeons with various procedures, while others enable doctors to remotely check in with their patients.
Some companies are researching ways to combine robotics with AI. AI-enabled robots can not only complete several tasks autonomously, but also adapt to situations and independently make decisions that serve human users in tangible ways.
Continued research and development in the robotics field has also led to the emergence of robot toys. These are mechanical or electronic devices that serve as a source of entertainment but can also be used for educational purposes. They usually include interactive features and their actions can be programmed by users to provide more personalized engagement and experiences. Many robot toys are remote-controlled; they might include functions like voice recognition, gesturing, sound orientation, and object recognition and movement detection.
In the coming years, robotics researchers will likely discover many more applications for robots and more companies will step up to design and manufacture innovative products. It's also possible that advanced robots with humanlike mental power will emerge over the next few decades, performing complex tasks with ease.







