
security audit
What is a security audit?
A security audit is a systematic evaluation of the security of a company's information system by measuring how well it conforms to an established set of criteria. A thorough audit typically assesses the security of the system's physical configuration and environment, software, information handling processes and user practices.
Security audits are often used to determine compliance with regulations such as the Health Insurance Portability and Accountability Act, the Sarbanes-Oxley Act and the California Security Breach Information Act that specify how organizations must deal with information.
These audits are one of three main types of security diagnostics, along with vulnerability assessments and penetration testing. Security audits measure an information system's performance against a list of criteria. A vulnerability assessment is a comprehensive study of an information system, seeking potential security weaknesses. Penetration testing is a covert approach in which a security expert tests to see if a system can withstand a specific attack. Each approach has inherent strengths and using two or more in conjunction may be the most effective approach.
Organizations should construct a security audit plan that is repeatable and updateable. Stakeholders must be included in the process for the best outcome.
This article is part of
What is data security? The ultimate guide
Why are security audits important?
There are several reasons to do a security audit. They include these six goals:
- Identify security problems and gaps, as well as system weaknesses.
- Establish a security baseline that future audits can be compared with.
- Comply with internal organization security policies.
- Comply with external regulatory requirements.
- Determine if security training is adequate.
- Identify unnecessary resources.
Security audits will help protect critical data, identify security loopholes, create new security policies and track the effectiveness of security strategies. Regular audits can help ensure employees stick to security practices and can catch new vulnerabilities.
When is a security audit needed?
How often an organization does its security audits depends on the industry it is in, the demands of its business and corporate structure, and the number of systems and applications that must be audited. Organizations that handle a lot of sensitive data -- such as financial services and heathcare providers -- are likely to do audits more frequently. Ones that use only one or two applications will find it easier to conduct security audits and may do them more frequently. External factors, such as regulatory requirements, affect audit frequency, as well.
Many companies will do a security audit at least once or twice a year. But they can also be done monthly or quarterly. Different departments may have different audit schedules, depending on the systems, applications and data they use. Routine audits -- whether done annually or monthly -- can help identify anomalies or patterns in a system.
Quarterly or monthly audits may be more than most organizations have the time or resources for, however. The determining factors in how often an organization chooses to do security audits depends on the complexity of the systems used and the type and importance of the data in that system. If the data in a system is deemed essential, then that system may be audited more often, but complicated systems that take time to audit may be audited less frequently.
An organization should conduct a special security audit after a data breach, system upgrade or data migration, or when changes to compliance laws occur, when a new system has been implemented or when the business grows by more than a defined amount of users. These one-time audits may focus on a specific area where the event may have opened security vulnerabilities. For example, if a data breach just occurred, an audit of the affected systems can help determine what went wrong.
Types of security audits
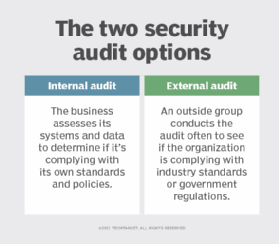
Security audits come in two forms, internal and external audits, that involve the following procedures:
- Internal audits. In these audits, a business uses its own resources and internal audit department. Internal audits are used when an organization wants to validate business systems for policy and procedure compliance.
- External audits. With these audits, an outside organization is brought in to conduct an audit. External audits are also conducted when an organization needs to confirm it is conforming to industry standards or government regulations.
There are two subcategories of external audits: second- and third-party audits. Second-party audits are conducted by a supplier of the organization being audited. Third-party audits are done by an independent, unbiased group, and the auditors involved have no association with the organization under audit.
What systems does an audit cover?
During a security audit, each system an organization uses may be examined for vulnerabilities in the following areas:
- Network vulnerabilities. Auditors look for weaknesses in any network component that an attacker could exploit to access systems or information or cause damage. Information as it travels between two points is particularly vulnerable. Security audits and regular network monitoring keep track of network traffic, including emails, instant messages, files and other communications. Network availability and access points are also included in this part of the audit.
- Security controls. With this part of the audit, the auditor looks at how effective a company's security controls are. That includes evaluating how well an organization has implemented the policies and procedures it has established to safeguard its information and systems. For example, an auditor may check to see if the company retains administrative control over its mobile devices. The auditor tests the company's controls to make sure they are effective and that the company is following its own policies and procedures.
- Encryption. This part of the audit verifies that an organization has controls in place to manage data encryption processes.
- Software systems. Here, software systems are examined to ensure they are working properly and providing accurate information. They are also checked to ensure controls are in place to prevent unauthorized users from gaining access to private data. The areas examined include data processing, software development and computer systems.
- Architecture management capabilities. Auditors verify that IT management has organizational structures and procedures in place to create an efficient and controlled environment to process information.
- Telecommunications controls. Auditors check that telecommunications controls are working on both client and server sides, as well as on the network that connects them.
- Systems development audit. Audits covering this area verify that any systems under development meet security objectives set by the organization. This part of the audit is also done to ensure that systems under development are following set standards.
- Information processing. These audits verify that data processing security measures are in place.
Organizations may also combine specific audit types into one overall control review audit.
Steps involved in a security audit
These five steps are generally part of a security audit:
- Agree on goals. Include all stakeholders in discussions of what should be achieved with the audit.
- Define the scope of the audit. List all assets to be audited, including computer equipment, internal documentation and processed data.
- Conduct the audit and identify threats. List potential threats related to each Threats can include the loss of data, equipment or records through natural disasters, malware or unauthorized users.
- Evaluate security and risks. Assess the risk of each of the identified threats happening, and how well the organization can defend against them.
- Determine the needed controls. Identify what security measures must be implemented or improved to minimize risks.
Test vs. assessment vs. audit
Audits are a separate concept from other practices such as tests and assessments. An audit is a way to validate that an organization is adhering to procedures and security policies set internally, as well as those that standards groups and regulatory agencies set. Organizations can conduct audits themselves or bring in third parties to do them. Security audit best practices are available from various industry organizations.
A test, such as a penetration test, is a procedure to check that a specific system is working as it should. IT professionals doing the testing are looking for gaps that might open vulnerabilities. With a pen test, for instance, the security analyst is hacking into the system in the same way that a threat actor might, to determine what an attacker can see and access.
An assessment is a planned test such as a risk or vulnerability assessment. It looks at how a system should operate and then compares that to the system's current operational state. For example, a vulnerability assessment of a computer system checks the status of the security measures protecting that system and whether they are responding the way they should.
Security audits are one part of an overall strategy for protecting IT systems and data. Find out the latest thinking on cybersecurity best practices and procedures.







