Getty Images/iStockphoto
Types of hackers: Black hat, white hat, red hat and more
Black, white and gray hats are familiar to security pros, but as the spectrum evolves to include green, blue, red and purple, things get muddled. Brush up on types of hackers.
The information security world has three well-known types of hackers: black hats, white hats and gray hats. These colored-hat descriptions were born as hackers tried to differentiate themselves and separate the good hackers from the bad. The roots of the black and white hat labels are drawn from Western movies, where protagonists wore white hats and antagonists wore black hats.
Today, the hacker-hat rainbow is broadening. While the terms are not as well known or well used, other hat colors describe other hacker traits.
What are black hats?
A black hat hacker is someone who maliciously searches for and exploits vulnerabilities in computer systems or networks, often using malware and other hacking techniques to do harm.
These stereotypical hackers might break laws as part of their hacking exploits, infiltrating victims' networks for monetary gain, stealing or destroying data, disrupting systems, conducting cyberespionage or just having fun.
What are white hats?
A white hat hacker, also known as an ethical hacker, is a security specialist hired to find vulnerabilities in software, hardware and networks that black hats might find and target. Unlike black hats, white hats only hack networks when legally permitted to do so.
White hats disclose all vulnerabilities to their employers. White hats also disclose vulnerabilities to the vendors whose hardware or software is affected so they can patch other customers' systems. White hat hacking techniques include penetration testing and vulnerability assessments.
What are gray hats?
A fusion of black and white, gray hats exploit security vulnerabilities without malicious intent, like white hats, but might use illegal methods to find flaws, like black hats. They might even release vulnerabilities to the public or sell details about them for a profit, like a black hat would. Gray hat hackers often hack without the target's permission or knowledge.
The gray hat description is also used to categorize hackers who might, at one stage in life, have broken the law in their hacking activities but have since become a more ethical, white hat hacker.
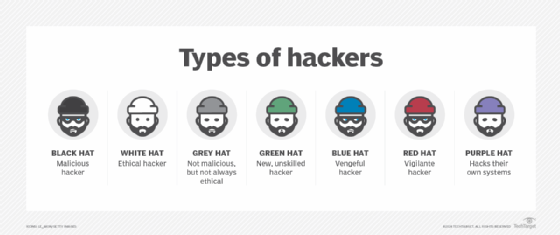
Other types of hackers
Over the years, people have attempted to paint the hat moniker other colors to describe different types of hackers. Rounding out the rainbow are green, blue, red and purple hats.
Green hats
A green hat hacker isn't necessarily Irish -- though some might be. Rather, a green hat describes hacker wannabes who, though they lack technical hacking skills and education, are eager to learn the tricks of the trade.
Blue hats
In Microsoft's world, blue hats act much like white hats: They are employed by the company to find vulnerabilities in unreleased products. Microsoft established its invite-only BlueHat conference to facilitate communications between hackers and company engineers.
In some circles, a blue hat is defined as a hacker seeking revenge. Blue hat hackers are also wannabe hackers, like green hats, but vengeance is a blue hat hacker's only motivation -- they have no desire to hone their hacking skills.
Red hats
A red hat hacker could refer to someone who targets Linux systems. But red hats are often characterized as vigilantes. Like white hats, red hats seek to disarm black hats, but the two groups' methodologies are significantly different. Rather than hand a black hat over to the authorities, red hats launch aggressive attacks against them to bring them down, often destroying the black hat's computer and resources.
Purple hats
A purple hat hacker is someone who attacks their own systems to learn and improve their hacking skills in a controlled environment. Some also categorize a purple hat as a combination of blue hat -- the kind who tests products before they are released -- and red hat -- but only ones who legally focus on finding black hats.
Other types of hackers
Hackers aren't only categorized by their hat colors. Other types of hackers include the following:
- Script kiddies. A script kiddie is a term for novice and unskilled hackers. This derogatory term describes hackers who use existing, premade exploits for their attacks.
- Nation-state hackers. Also called state-sponsored hackers, nation-state hackers are employed by their governments to hack other governments for foreign intel.
- Hacktivists. A portmanteau of hacker and activist, a hacktivist is someone who conducts politically or socially motivated cyberattacks.
- Insider threats. An insider threat is a person who has access to -- and poses a risk to -- an organization's data and systems. Insider threats include compromised, negligent and malicious insiders.
Sharon Shea is executive editor of TechTarget Security.