passive reconnaissance
What is passive reconnaissance?
Passive reconnaissance is an attempt to gain information about targeted computers and networks without actively engaging with the systems. In active reconnaissance, in contrast, the attacker engages with the target system, typically conducting a port scan to find any open ports.
The term reconnaissance comes from its military use to describe an information-gathering mission. In computing and networking, both passive and active reconnaissance are sometimes referred to as passive attacks because the purpose is simply to obtain information, rather than to actively exploit the target. However, reconnaissance is commonly used when preparing for an attack against a target system.
Why do cybercriminals do passive reconnaissance?
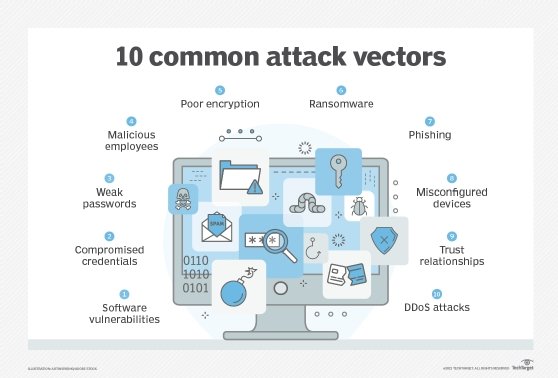
The main idea behind passive reconnaissance is to discover as much relevant information as possible about the target organization and its infrastructure without being detected. Cybercriminals attempt to achieve this in several ways:
- Open source intelligence (OSINT). Would-be attackers gather information from publicly available sources, typically via the internet. Collected data can come from a wide range of sources and include specific details about the target organization and its employees, including email addresses, phone numbers, IP addresses, domain names, suppliers, deployed technologies, geographic locations and social networking accounts. Cybercriminals can find most of this data by using search engines such as Google or Bing, as well as tools such as theHarvester, a command-line utility that uses popular search engines to more easily retrieve OSINT data. In some cases, the information that hackers discover is highly sensitive, making their jobs much easier.
- Environmental assessments. In conjunction with their OSINT searches, cybercriminals will look specifically for details about the target organization's operating environment. For example, they might try to discover what type of computers are being used, what operating systems are running, which software has been installed, an application's programming language and similar details about the organization's infrastructure and its configuration. To find this information, the cybercriminals often use a variety of tools. For example, they might use Wget to download files from a web server and then search those files for information about the environment, or they might use Netcraft, an internet security tool, to find specific details about a website such as IP addresses, domains or security certificate information. Hackers might also masquerade as authorized users to gain access to systems to learn more about the environment.
- Network examination. Cybercriminals will also learn whatever they can about an organization's network and its internet connections. For example, they'll often search for Domain Name System (DNS) information such as IP delegation, domain ownership or DNS record content. A tool such as Netcraft can also be useful for this type of research, as can tools such as nslookup or whois. Cybercriminals might also eavesdrop on an organization's network traffic using Wireshark or another packet sniffer. This is sometimes done in conjunction with war driving, the process of locating and possibly exploiting connections to wireless local area networks. In addition, cybercriminals might use a tool such as Shodan to identify vulnerable devices connected to the internet whose IP addresses belong to the target organization.
- Physical searches. Would-be hackers are not above performing physical searches to get at sensitive information. This might include digging through trash or looking for data stored on discarded computers or other devices. Any discarded item represents a potential inroad.
Both active and passive reconnaissance are also used by ethical hackers to carry out attacks against a system to determine its vulnerabilities. These can then be addressed before the system falls prey to a real attack. Ethical reconnaissance is typically part of a larger penetration testing strategy that also incorporates steps such as network scanning and vulnerability assessment.
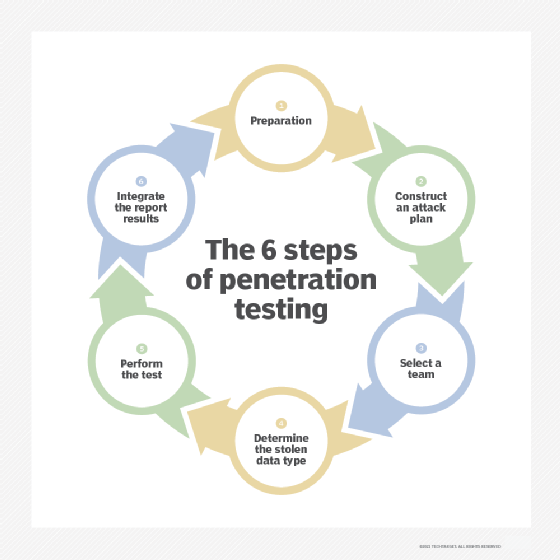
Cybercriminals use passive reconnaissance because they want to go unnoticed, so it can be very difficult for the target organization to detect. The organization's best defense is to implement a layered protection strategy that includes comprehensive firewall protection and an intrusion prevention system (IPS). The firewall should permit only essential traffic and limit port exposure. The IPS should detect port scans in progress and shut them down before hackers can gain a full map of the network. The organization should also conduct regular penetration testing and employ other security measures that protect against data leakage.
Explore nine essential elements of network security and five different types of firewalls.
