
What is machine vision?
Machine vision is the ability of a computer to see; it employs one or more video cameras, analog-to-digital conversion and digital signal processing. The resulting data goes to a computer or robot controller. Machine vision is similar in complexity to voice recognition.
Machine vision is sometimes conflated with the term computer vision. The technology is often integrated with artificial intelligence (AI), machine learning and deep learning to accelerate image processing.
How does machine vision work?
Machine vision uses cameras to capture visual information from the surrounding environment. It then processes the images using a combination of hardware and software and prepares the information for use in various applications. Machine vision technology often uses specialized optics to acquire images. This approach lets certain characteristics of the image be processed, analyzed and measured.
For example, a machine vision application as part of a manufacturing system can be used to analyze a certain characteristic of a part being manufactured on an assembly line. It could determine if the part meets product quality criteria and, if not, dispose of the part.
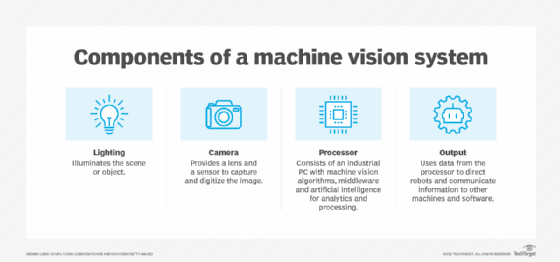
In manufacturing settings, machine vision systems typically need the following items:
- Lighting. Lighting illuminates the object or scene to make its features visible.
- Lens. This captures the image and delivers it to the sensor in the camera as light.
- Capture board, frame grabber or sensor. These devices work together to process the image from the camera and convert it to a digital format as pixels. Image sensors convert light into electric signals using either complementary metal-oxide semiconductor technology or a charge-coupled device.
- Processor. The processor runs software and related algorithms that process the digital image and extract the required information.
- Communication. These systems enable the machine vision cameras and processing system to communicate with other elements of the bigger system, usually using a discrete input/output signal or a serial connection.
There are two types of cameras used in manufacturing machine vision:
- Area scan. These cameras take pictures in a single frame using a rectangular sensor. The number of pixels in the sensor corresponds to the width and height of the image. Area scan cameras are used for scanning objects that are the same size in terms of width and height.
- Line scan. These cameras build an image pixel by pixel. They're suited for taking images of items in motion or of irregular sizes. The sensor passes in a linear motion over an object when taking the picture. Line scan cameras aren't as limited to specific resolutions the way area scan cameras are.
Camera lenses vary in optical quality. Two important specifications in any vision system are the sensitivity and the resolution of the lens, which have the following characteristics:
- Sensitivity is the ability of a machine to see in dim light or to detect weak impulses at invisible wavelengths.
- Resolution is the extent to which a machine can differentiate between objects.
In general, the greater the resolution, the more confined the field of vision. Sensitivity and resolution are interdependent. If other factors are constant, increasing the sensitivity reduces the resolution, and increasing the resolution reduces the sensitivity.
Human eyes are sensitive to electromagnetic wavelengths ranging from 390 to 770 nanometers. Video cameras can be sensitive to a range of wavelengths much wider than that. Some machine vision systems function at infrared, ultraviolet or X-ray wavelengths.
Binocular, also called stereo, machine vision requires a computer with an advanced processor. In addition, high-resolution cameras, a large amount of RAM and AI programming are required for depth perception.
Types of machine vision
Machine vision systems can operate across various dimensions based on the specific needs and requirements of a particular application.
Common types of machine vision systems include the following:
- 2D vision systems. These are the most widely used systems that excel in pattern recognition tasks.
- 3D vision systems. Operating in multiple dimensions, 3D vision systems provide enhanced accuracy for measurement and inspection purposes.
- Smart camera-based vision systems. These systems use integrated cameras and software to perform a variety of inspection-related tasks.
- Compact vision systems. These systems are designed to be self-contained and can seamlessly integrate into existing equipment and manufacturing processes.
- PC-based vision systems. By using computer processing and image analysis, these systems enable the execution of more complex visual inspection tasks.
- Multispectral imaging. As an alternative to conventional 2D imaging, this method involves capturing images at multiple wavelengths.
- Hyperspectral imaging. Similar to multispectral imaging, hyperspectral imaging captures images at a significantly larger number of wavelengths, facilitating detailed analysis of spectral data.
- Variable magnification lenses. Equipped with adjustable magnification levels, these lenses provide greater flexibility in carrying out inspection tasks.
How are machine vision systems used?
Machine vision applications are used in a range of industries to perform various tasks, including the following:
- Electronic component analysis. Machine vision is used in the construction of circuit boards for tasks such as solder paste inspection and component placement.
- Optical character recognition (OCR). OCR enables a computer to extract printed or handwritten text from images.
- Handwriting and signature recognition. With these features, a computer can detect patterns in images of handwriting and signatures.
- Object recognition. In the automotive industry, self-driving cars use object recognition on images taken by cameras to identify obstacles on the road. Machine vision systems also determine the position of objects, such as the proper placement of a label on a pill bottle.
- Pattern recognition. Medical imaging analysis uses pattern recognition to make diagnoses based on technologies such as magnetic resonance imaging, blood scans and brain scans.
- Materials inspection. Machine vision capabilities in materials inspection systems ensure Quality control. Machine vision checks for flaws, defects and contaminants in a range of materials and products. For example, these systems can inspect pills and tablets for issues during manufacturing.
- Currency inspection. Machine vision is used to analyze currencies to detect counterfeit notes.
- Item counting. This capability is used to tally items such as pills in a packet or bottles in a case.
- Barcode tracking. This common application uses the capabilities of machine vision systems to read and track barcodes in real time.
- Robotics. The use of cameras for robot guiding is a rapidly growing area of machine vision. Both 2D and 3D cameras are important in instructing robots to handle individual or bulk components effectively. These applications provide high return on investment by reducing the requirement for physical labor.
Benefits of machine vision
Common benefits of machine vision include the following:
- Removes human error. Although the human eye is impressive, it's not immune to errors. Machine vision excels in quantitative measurements due to its precision, consistency and speed. For instance, when integrated into a production line, a vision system can swiftly inspect hundreds or even thousands of parts per minute. By using high-resolution cameras, machine vision systems can detect and examine minute object details that could go unnoticed by the human eye. Moreover, machine vision eliminates the effects of operator fatigue and individual variances, ensuring consistent and reliable inspections.
- Reduces downtime. A vision system protects against part damage by removing physical touch between a test system and manufactured parts. As wear and tear take their toll on mechanical components, it also cuts down on the time and costs associated with repairs. Machines operate more quickly as they require less care, enabling companies to achieve production deadlines consistently and easily.
- Lowers cost. A machine vision system can boost manufacturing speed and reduce the labor necessary to operate the equipment. It can also minimize the scrap rate so less materials get wasted, which eventually lowers the overhead.
- Improves workplace safety. Machine vision combined with AI improves workplace safety by minimizing the need for human intervention during the manufacturing process. When operating large, powerful machines, employees are less likely to sustain injuries, and their contact with hazardous parts and materials is also limited.
- Detects flaws. Machine vision can detect product irregularities, such as surface dents and scratches. By carefully setting detection boundaries, it distinguishes between acceptable and unacceptable flaws.
- Measures accurately. A machine vision system can locate and measure specific points on an image, such as diameter, radius, distance and depth. For example, this could help determine the inner diameter of an engine cylinder bore or the liquid fill level of a container. This information can be gathered with either 2D or 3D cameras.
- Identifies printing defects. A machine vision system can easily identify printing anomalies, such as incorrect color shades, blemished prints or missing letters. The system begins by inputting a master or golden image, which serves as the reference for all produced components. Any deviations from the master image are promptly identified and flagged for correction, ensuring accurate and high-quality prints.
Machine vision in AI
AI is used in machine vision to expedite the decision-making process. AI can process a large amount of images and data information that was previously too difficult to gather.
Examples of how AI is used with machine vision include the following:
- AI can assist with signature and character recognition, which require a level of nuance.
- In manufacturing, AI helps with object recognition and materials inspection to enable machine vision systems to understand acceptable variations in the shape and texture of an object or material.
- In quality assurance, an AI-enabled system can interpret acceptable anomalies rather than rejecting anything that doesn't rigidly fit one specification.
Machine vision in robotics
Machine vision, paired with AI and deep learning, expands the role of robots in performing production-line tasks, such as picking, sorting, placing and performing a manufacturing line scan. This combination of technologies also enables robotics to operate in other environments, such as supermarkets, hospitals and restaurants.
Examples of how machine vision is used in robotics include the following:
- A robot with machine vision can navigate the supermarket aisles, capturing inventory data about products on the store's shelves. It scans products using radio frequency identification (RFID) technology to read a barcode and can avoid obstacles in crowded aisles. Amazon Go retail stores use machine vision-powered systems to monitor inventory and check out customers when they're ready to pay.
- Machine vision technology enables automation, making it possible for process sequences in various applications to be networked.
- Machine vision also makes collaboration between robots and humans more efficient and safer. For example, in a supermarket, a robot can be dedicated to performing inventory management tasks so that human associates have more time to assist customers. The robot can perform inventory scans more frequently than people with greater accuracy. On an assembly line, robots with machine vision can analyze hazardous materials and perform other dangerous tasks without exposing workers to unsafe conditions.
- The data machine vision-enabled robots collect and use can be processed in the cloud or at the edge of the network, enabling scalability and detailed data analysis.
What is the difference between machine vision and computer vision?
In some cases, the terms machine vision and computer vision are used synonymously. In other cases, distinctions are made.
Machine vision is often associated with industrial applications of a computer's ability to see. The term computer vision is often used to describe any technology in which a computer is tasked with digitizing an image, processing the data it contains and taking some kind of action.
Another distinction that's often made is in processing power -- that is, the difference between a machine and a computer. A machine vision system typically has less processing power and is used in Lean manufacturing environments, performing practical tasks at a high speed to acquire the data needed to complete a specified job. Quality control, inspection of items and guiding of objects through an assembly line are common applications of machine vision.
Computer vision systems collect as much data as possible about objects or scenes and aim to fully understand them. Computer vision is better for collecting general, transferable information that may be applied to a variety of tasks. It also can be performed without a camera as the term can refer to a computer's ability to process images from any source, including the internet. Common applications of computer vision include self-driving cars, reading barcodes and RFID tags, and inspecting for product defects.
Machine vision is one of the many applications of AI in manufacturing. Learn other ways manufacturing companies use AI to simplify business processes and increase efficiency.







