What are customer service and support?
Customer service is the support organizations offer to customers before, during and after purchasing a product or service. When customer service is executed correctly, the organization's representative values both potential and existing customers equally. Customer service representatives are the main line of contact between an organization and its customers, making customer experience (CX) a critical facet and the main priority of customer service teams.
The customer service team represents the company's voice, pursuing customer satisfaction and loyalty. In today's digital-first world, customer service extends beyond traditional phone and email support to include AI-powered chatbots, self-service portals and social media engagement.
Customer support falls under the customer service umbrella but prioritizes customers who have trouble or require assistance with a product or service they purchased. Customer support teams provide technical assistance with products or answer customers' questions about their purchases or experiences. The goal of customer support teams is for customers to leave their interactions with answers, solutions and overall positive experiences.
Why are customer service and support important?
While customer service and support teams interact with customers on an as-needed basis -- using various chat channels such as phone, website chat applications and social media messaging -- those moments of contact are critical to keeping an organization running successfully.
If customer service teams provide a positive CX and customer support teams successfully assist customers with questions or problems, then those customers are likely to be happy and do business again with the organization. With good customer service and support, satisfied customers might also leave positive reviews or tell friends and family about an organization, which can yield more customers.
Both customer service and support directly impact brand reputation, customer retention, and revenue. Businesses that excel in customer support can expect the following benefits:
- Higher customer retention rates.
- Increased word-of-mouth referrals.
- Reduced churn rates.
- Stronger brand loyalty.
In contrast, poor service can lead to negative reviews, social media backlash and lost sales.
The shift from reactive to proactive support
Traditionally, customer service was reactive; companies responded only when customers reached out. Today, businesses leverage AI and predictive analytics to anticipate customer issues and offer proactive solutions.
For example, an e-commerce company might use AI to detect cart abandonment and send a personalized discount to encourage checkout completion.
How do customer service and customer support differ?
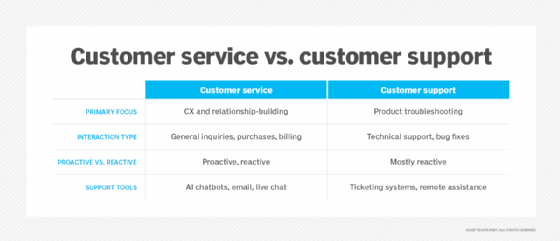
While both customer service and support teams focus on the customer, they help customers in different ways.
Customer service teams focus on providing the best possible CX before and after a customer purchases a product. They also specialize in customer retention and solving complex issues that frustrate customers. The customer service team is the face of the organization and the frontline when customers require assistance. Customer service agents help customers pay bills, review or make changes to accounts, handle returns and answer frequently asked questions.
Customer support teams also interact with customers, but they are part of the larger customer service department. They answer product-related questions and troubleshoot problems when necessary. Depending on the industry, support teams provide guidance on electronic equipment, software and apparel, among other products. Customer support agents solve problems related to products customers purchase or use.
In essence, while both focus on enhancing CX, they serve different roles.
Types of customer service and support
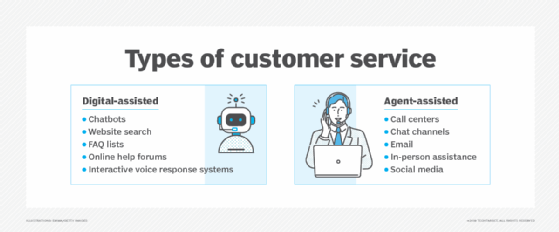
An organization might employ different types of customer service and support depending on its goals and offerings. The types include the following:
Digital-first customer service
- AI-powered chatbots (leveraging generative AI products such as ChatGPT and Gemini).
- Omnichannel messaging (WhatsApp, Facebook Messenger, WeChat).
- Voice assistants (such as Siri, Alexa or Google Assistant).
- Self-service portals (FAQs, knowledge bases, interactive tutorials).
Customer support services
- Troubleshooting and technical assistance.
- Product installation and maintenance.
- Software updates and security fixes.
- Warranty claims and replacements.
Key customer service and support skills
Customer service and customer support teams require the same skills, whether they work in a call center or contact center, face-to-face with customers or as live chat agents. Those skills include the following:
- Organizational knowledge.
- Active listening.
- Written and verbal communications.
- Calmness under pressure (able to de-escalate situations).
- Problem-solving.
- Multitasking.
- Team-oriented with coworkers.
- Cooperative attitude with customers.
Customer service and support tools and technologies
Customer service and support teams incorporate various tools to operate efficiently. Here are some examples:
- Call management system. Teams use these systems to log incoming phone calls and route them through a network to the proper person or department.
- Contact center. Teams manage all customer interactions through the contact center, which offers omnichannel support encompassing email, voice, chat, chatbots and websites.
- Internet-based customer service suite. Also known as e-service suites, vendors design these platforms specifically for customer self-service.
- Field service and dispatch system. An essential part of customer service and support, field service and dispatch systems enable customer service and support teams to contact technicians and dispatch them to service a product.
While customers primarily use email and phone systems to contact customer service and support agents, those methods are not always the most efficient. Customers who pick up the phone can benefit from live chat with an agent, though both channels are limited to business hours.
To increase customer satisfaction and minimize costs, many organizations use customer-based service applications, such as web self-service. These applications allow customers to contact organizations outside of normal business hours and without human assistance.
Some examples of web self-service transactions include the following:
- Make a payment.
- Find usernames.
- Reset passwords.
- Check order status.
- Update account information.
- Look up business hours.
- Access user manuals.
Chatbots are increasingly popular for customer service and support teams. Like web self-service, customers can use chatbots on various channels outside normal business hours. Instead of clicking on links on a webpage, chatbots can answer verbal and written questions. Organizations that use chatbots typically train them on frequently asked questions and tasks, and program them to their specific industries.
How have customer service and customer support evolved?

Customer service and customer support have transformed over the years. In the past, organizations didn't prioritize CX or the customer journey in customer interactions. The main interactions were simply business transactions: The customer goes to a store, purchases a product, then leaves and returns home.
If customers required assistance, they had to return to the store during its normal business hours, despite the inconvenience. Organizations prioritized their convenience over customer convenience, providing only one channel for service and a specific timeframe for service hours.
Over time, organizations realized that positive CX could benefit them as much as or even more than their convenience, as happy customers could return and become loyal to the brand. So, customer service and support became 24/7 omnichannel initiatives, where customers can call, chat, email or post on social media at any time of day and get in touch with a representative from the organization.
In the future, innovative technologies such as AI and machine learning might transform customer service and customer support even further. Some of these advancements are already available in chatbots and other virtual assistants, which help save time for customer service representatives and offer customers more convenient service and support.
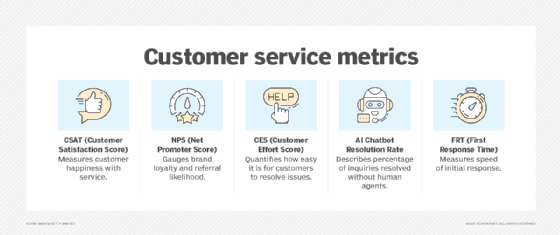
Customer service metrics that matter today
Beyond traditional KPIs, companies now track AI efficiency, automation success and customer sentiment.
The impact of AI and machine learning in customer support
AI-driven customer service is reshaping CX by automating responses and enhancing personalization. Here are a few ways AI improves customer support:
- 24/7 instant support. AI chatbots handle basic queries without human intervention.
- Personalized interactions. Natural language processing (NLP) algorithms customize responses based on customer history.
- Predictive assistance. AI detects potential issues before customers reach out for help.
- Sentiment analysis. AI identifies frustrated customers and prioritizes them for human agents.
Companies like Amazon, Netflix and Google use AI to streamline support, reduce wait times, and increase customer satisfaction. Some specific examples are given below:
- Apple's Genius Bar supports personalized, face-to-face technical support.
- Zappos' Legendary Service accommodates no time limit on customer calls; agents focus on relationship-building.
- Amazon's AI-driven CX provides one-click refunds with fast responses via AI chatbots.
Companies that invest in superior CX generally see higher customer lifetime value and stronger brand advocacy.
The role of social media in customer service
In addition to AI and machine learning, social media platforms have become essential for real-time customer interactions. Here are some ways social media is being used to advance customer service:
- X (formerly Twitter). Instant issue resolution (e.g., airline flight delays).
- Instagram and TikTok DMs. Brands provide personalized support via direct messages.
- WhatsApp and Facebook Messenger. Integrated social commerce with live chat.
Brands that engage with customers via social media typically see faster resolution times and higher engagement rates.
Are customers and businesses in agreement about customer service quality? See how to address common customer service gaps.






