A guide to contact center security best practices
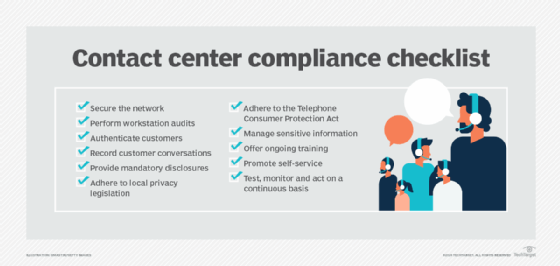
Follow this comprehensive contact center security checklist that encompasses technology safeguards, customer data protection procedures and common business sense.
Many company executives and contact center leaders know about the struggles to protect customer data. With increased distractions or assessing how new technology, like AI, can improve contact center services, company leaders can't lose focus on emerging security threats that could compromise data.
Contact center security must remain a focal point to protect customer data and enhance customer confidence when interacting with an organization, which is key to better customer relationships and experiences.
The increasing importance of contact center security
Contact center security must be front and center when developing and implementing a strategic customer experience framework. Organizations that don't employ proper security controls could risk serious negative consequences, such as the following:
- Financial. A security or data breach can result in lost business revenue and fines levied by various entities that significantly affect the bottom line.
- Reputation. Customers who feel their personal data isn't secure or who have been affected by security incidents, such as identity theft, might no longer do business with the organization or post their concerns on various social channels. The goodwill and positive reputation an organization builds over time is one of the biggest drivers to acquiring and retaining customers.
- Business disruption. Resources dedicated to running the business must be redirected to research and resolve the incident and improve security protocols.
Types of contact center security best practices
To avoid security problems, businesses need to implement a contact center security checklist that covers three categories: technology, customer and business best practices.
Technology best practices
In order to protect customer data and maintain security, companies and their contact centers should implement the following technology checklist:
Encrypt data. Encryption translates an organization's stored or transmitted data into different forms, which require a specific key to translate it back into its original format. Organizations often encrypt data to protect specific customer records, including medical, credit card or personal information.
Update technology. Keeping technology current ensures systems and components have the latest safeguards in place. Bad actors continuously test systems, looking for cracks that let them access data. Key practices to update technology include antivirus software, installing software patches and eliminating legacy systems that vendors no longer support.
Minimize data availability and access. More data is being stored each day. And, with more individuals given access to that information, an organization multiplies its risk of a potential data breach. Best practices to minimize availability and access to data include the following:
- Restrict the number of people who can access sensitive information.
- Use system permissions to manage who can access specific data.
- Automate session timeout rules.
- Delete employee access to accounts as soon as the person leaves the organization.
- Mask sensitive data to limit the information displayed to employees. For example, place asterisks over the first five digits of a Social Security number.
- Use alternate technologies to capture sensitive information. For example, send a caller to an interactive voice response system to enter credit card information.
- Limit the storage of critical information. For example, delete data after a customer provides a credit card number in a transaction. This scenario represents a tradeoff between customer convenience and data security.
- Use firewalls and intrusion detectors to prevent and report attempted and unauthorized activity.
Perform regular data backups. Regular data backups should be established to minimize data loss and provide the ability to recreate customer records in the event of a security breach.
Customer best practices
Businesses should institute the following customer-related best practices to protect customer data:
Maintain transparency. Companies must be transparent with customers, including telling them why the business requires sensitive data and how it uses and protects that information. Effective transparency goes beyond typical privacy statements, and organizations should share this information in an easy-to-understand format.
Transparency improves customer confidence, which instills a higher level of trust in the organization. Additionally, if an organization can teach its customers how to protect themselves -- like how to monitor credit card usage -- they feel better about sharing information.
Use authentication protocols. Authentication aims to prove somebody is the person they claim to be. In the past, typical authentication protocols used single-factor authentication that required users to enter a single piece of identifying information, such as a password. Many organizations have shifted to multifactor authentication, where users must enter multiple pieces of identifying information, like a password and an additional code. In many cases, the system sends the code to a user's mobile device.
Voice authentication is a lesser-used technology. As the technology improves, it should become a more viable customer identification tool.
Business best practices
Organizations should adhere to the following business-related procedures to protect customer data:
Train employees. Organizations need to continuously train contact center agents to ensure they understand how easily bad actors can steal customer data. Employee training should focus on specific behaviors to protect customer data along with understanding the process to communicate suspicious activity. Training should include the following:
- Follow smart practices to maximize password strength, like avoiding easily identifiable information.
- Shred documents with personal information and don't leave written notes around. Eliminate the need for paper documents wherever possible.
- Limit the information sent electronically to customers, like personal medical information.
- Don't open attachments or access links unless they come from a reliable source.
- Follow facility physical security protocols whether working on-site or remotely.
Implement improved remote work practices. Remote employees create new security gaps that can be addressed by the following measures:
- Require the use of company-issued devices.
- Develop requirements and monitor compliance for home network security and data access.
- Don't allow third-party listening systems in the remote workplace.
Share responsibility for data security. Everyone, even individuals outside of the contact center, is responsible for customer data security. Organizations can practice broad ownership of customer data security in many ways, including the following:
- Monitor and report suspicious activity.
- Restrict unauthorized hardware or software and access to questionable websites and documents.
- Bring unattended sensitive documents to leadership.
Use security expertise. Security expertise is critical to stay ahead of malicious actors. Organizations must bring on staff or use consulting firms that specialize in cybersecurity and other security-related matters.
Protecting an organization from security breaches and managing sensitive information isn't a part-time job, and ensuring the proper controls are in place -- and keeping an eye on the future -- requires dedicated effort and expertise.
Test security controls. Organizations must continuously test their technologies and processes to protect customer data. Business leaders should never assume everything will work as planned, especially when dealing with human behaviors and sophisticated bad actors. Examples of testing security controls include the following:
- Implement security audits, including security log reviews if a breach occurs.
- Scan for malware and other unauthorized software regularly.
- Perform office and home workstation reviews to ensure agents follow security best practices.
- Include the testing of security controls and the recovery process as part of the overall business continuity planning.
Prepare for a security breach. Customers are more likely to feel confident in the recovery process if an organization quickly controls a breach and has an action plan to protect customers. Security breach preparation should be included in disaster recovery and business continuity plans with specific actions outlining how and when to notify employees and customers, and how to support continued operations.
Business executives and contact center leaders should not get distracted by other initiatives. As security threats become more sophisticated, CX leaders should always prioritize contact center security.
Scott Sachs is president and founder of SJS Solutions, a consultancy that specializes in contact center strategy assessments and technology selection.