CALMS
What is CALMS?
CALMS is a conceptual framework for the integration of development and operations (DevOps) teams, functions and systems within an organization. By adopting CALMS, organizations can assess their ability to adopt DevOps methodologies and, ultimately, improve their software development operations and delivery.
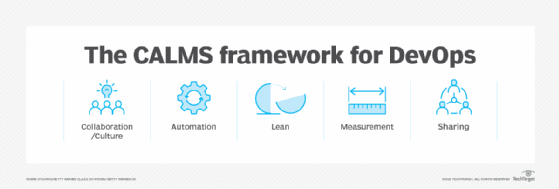
CALMS is an acronym that stands for culture, automation, lean, measurement and sharing. The acronym is credited to Jez Humble, co-author of The DevOps Handbook. Adopting the CALMS framework and its principles can help organizations to create a highly productive, efficient and collaborative software development environment.
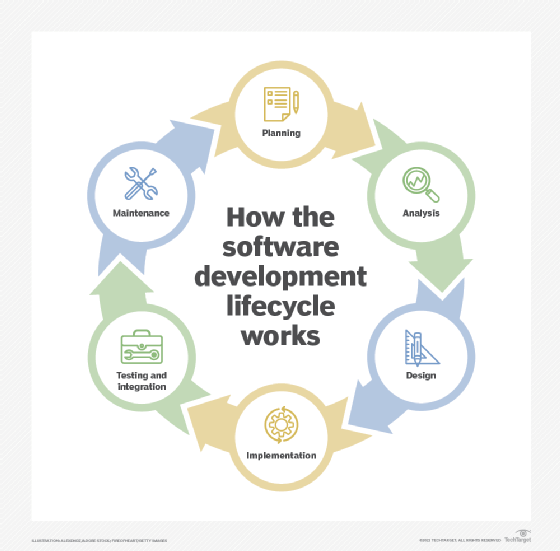
The CALMS framework is often used as a maturity model, helping managers to evaluate whether their organization is ready for DevOps or what needs to change if not. Moreover, it is widely recognized by the global DevOps community as a way to successfully adopt DevOps practices in the software development lifecycle (SDLC) and benefit from those practices.
Five pillars of the CALMS framework
As a framework for implementing DevOps, CALMS consists of five key pillars:
Culture
CALMS encourages creating a culture of shared responsibility. It also emphasizes a culture where open communication and collaboration are valued. In addition, it encourages learning from failures to facilitate innovation, out-of-the-box thinking and faster resolutions.
Automation
Recognizing that automation is one of the core tenets of DevOps, CALMS emphasizes the need for automation in software development. Team members should seek out ways to automate as many tasks as possible to minimize the need for manual interventions and improve the speed, efficiency and reliability of the SDLC.
Teams should also be comfortable with the idea of continuous delivery (CD). CD provides numerous benefits, including improved code quality, higher developer productivity and faster product releases and time-to-market.
Automation with CD facilitates fast, timely feedback loops that then enable fast iterations and ongoing improvements. Adding infrastructure as code (IaC) is also useful, since it makes it easy to set up and manage infrastructure in a safe, consistent way. IaC and CD unburden developers from mundane "busywork" so they can focus on their core task, which is to create high-quality software.
Lean
The lean principle is borrowed from manufacturing. It refers to a production approach that seeks to maximize productivity while minimizing waste. In the DevOps and CALMS contexts, lean means that team members should be able to visualize work in progress (WIP), limit batch sizes and manage queue lengths.
Teams should also try to streamline SDLC processes, aim for continual process improvement and eliminate non-value-adding activities to the best possible extent. The end goals of going lean are to accelerate software delivery, improve software quality, lower production costs and enhance customer experiences.
Measurement
Data is collected to help teams make objective assessments and fact-driven decisions. Also, such mechanisms provide visibility into all the systems and processes involved in the SDLC.
These processes and activities are continuously tracked to identify improvement areas and inform decision-making (that might result in improved DevOps processes and outcomes).
Sharing
The sharing pillar is about implementing user-friendly channels to enable ongoing communication between development and operations. These channels should make it easy for team members to disseminate knowledge, share best practices and engage in continual learning.
Sharing is also vital to build a culture that values openness, transparency and community. This pillar encourages removing the siloes that previously existed between Dev and Ops. This is exactly what DevOps also proposes.
Interconnections between the CALMS pillars
The five pillars of CALMS are interconnected, meaning it's important to implement all five to achieve the full potential of DevOps.
For example, improved software quality depends on both the Automation and Learning pillars. Automated testing tools increase testing coverage and help teams quickly find bugs earlier in the SDLC so they can iterate faster and produce a higher-quality product. Similarly, knowledge sharing and collaboration between Dev, Ops and Testing teams create a culture where quality is everyone's responsibility.
Another example of interconnection is between Lean and Measure. In the context of DevOps, Lean sets the expectation that failure is inevitable -- paving the way for continual improvement. Data also helps to improve SDLC processes; by capturing data and metrics, teams can measure their performance and identify points of failure. They can then determine the actions needed to rapidly recover from the failure and keep moving forward.
Benefits of CALMS
The CALMS framework provides a way for organizations to adopt DevOps by describing the skills and competencies needed to successfully implement DevOps processes and practices. After implementing the framework's suggestions, organizations can enjoy many benefits:
- Streamlined software development and delivery processes.
- Enhanced communication and collaboration among team members.
- Learning valuable lessons from failures.
- Easily manageable infrastructure and activities related to testing and deployment through automation.
- Optimized team productivity and efficiency.
- Accelerated product development and time to market.
- The ability to gather and track performance metrics to guide ongoing improvements.
- A culture of knowledge-sharing, transparency, innovation and celebrating each other's success.
At its core, the CALMS framework helps organizations speed up software development and delivery, improve software quality, foster innovation, facilitate continual improvement and promote greater agility and resilience among their workforce.
CALMS and ITSM
The CALMS framework is sometimes considered an alternative to Information Technology Service Management (ITSM). ITSM is a strategic approach to designing, delivering, managing and improving the way IT is used within an organization.
ITSM, which is often associated with ITIL is considered by some IT administrators to be too rigid and therefore incompatible with DevOps. CALMS is sometimes thought of as a way of negotiating the differences between the two approaches.
That said, it can be challenging to implement all the practices CALMS recommends. Automation tools are expensive, workflows need to be redesigned and staff need to undergo training. Identifying appropriate metrics for measurement or opportunities to eliminate waste can also be challenging, as can overcoming resistance to change. Organizations that can overcome these potential challenges, however, are poised to reap the benefits of CALMS and DevOps.
DevOps can be challenging to communicate across IT and business teams. Learn more about the five elements of the CALMS framework and how it can help organizations measure progress.
