What is an inductive argument?
An inductive argument is an assertion that uses specific premises or observations to make a broader generalization. These inductive conclusions are reached by observing several specific incidences or situations, detecting a pattern and then, based on the patterns or inferences observed, drawing a conclusion. Inductive reasoning is usually contrasted with deductive reasoning, where the arguer starts with general information and then drills down to arrive at specific conclusions.
People often use inductive reasoning informally in everyday situations. For example, the intersection of A and B streets is only jammed at 4 p.m. each day. The textile plant on A street lets out at 4 p.m. each day. Therefore, the traffic jam on A and B streets is most likely caused by employees who are leaving work to go home.
Inductive arguments like the above example possess some degree of uncertainty. For instance, we don't know for sure that the traffic jam at the intersection of A and B streets is caused by employees leaving the textile plant at 4 p.m., but there's a high likelihood this is the case.
Inductive reasoning is a logical process that proceeds from bottom-level observations to a top-level conclusion based on the patterns observed, but its deductive results are never absolute. Instead, the conclusions reached with deductive reasoning are assessed as being either strong or weak, most likely or less likely -- and they're always backed by the evidence that has been gathered and observed.
Comparing inductive vs. deductive reasoning
Both inductive and deductive arguments are methods of critical thinking that are based on logic, facts and evidence. Where the two methods differ is that an inductive argument is a type of bottom-up logic because it observes ground-level specific events or details, detects patterns in this data, and then begins to formulate broader top-level generalizations or conclusions based on the data and the data patterns it has seen. In contrast, a valid deductive argument is a top-down argument that produces an irrefutable conclusion if its premises are true.
An example of top-down deductive reasoning is all fruits have seeds, lemons are a fruit; therefore, lemons have seeds.
Greek philosopher Aristotle was considered a deductive reasoner because his system of top-down logic typically moved from general premises down to specific conclusions. Each top-down application of Aristotelian reasoning was known as a syllogism, which is derived from the Greek word syllogismos, which is a conclusion or inference.
The conclusions that deductive reasoning produces are absolute -- true or false. There's no middle ground of uncertainty of most likely or least likely, as there is with inductive reasoning.
Deductive and inductive reasoning are both methods of logic aimed at producing a conclusion or result; however, they approach this logical process differently.
Inductive reasoning with examples
Inductive reasoning plays a major role in artificial intelligence (AI), which through data analysis, pattern recognition and inductive inferences at the bottom levels of data works its way up into top-level, most likely conclusions and recommendations for users.
Example
- Premise: All the tigers I saw on my safari trip to South Africa were orange.
- Conclusion: Therefore, all tigers are orange.
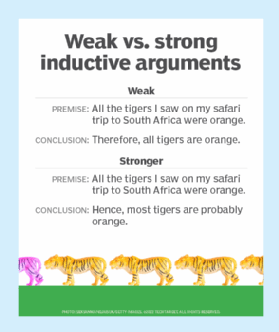
This is an example of a weak inductive argument because even though the premise is true -- the observer saw only orange tigers on their trip -- the conclusion can't be true. This is because white tigers also exist, even though the observer didn't see them.
It's possible to strengthen this inductive argument and its conclusion with the following:
- Premise: All the tigers I saw on my safari trip to South Africa were orange.
- Conclusion: Hence, most tigers are probably orange.
Although the conclusion isn't 100% true, as white tigers still do exist, it's much stronger than the previous argument due to the words most and probably.
How is inductive reasoning used?
Inductive reasoning is used in AI as well as in everyday situations that help people make sense of the world.
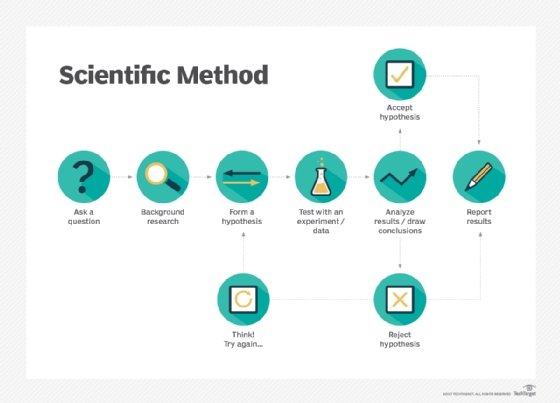
Scientists and researchers gather data, create hypotheses based on that data and then test their theories to prove or disprove those hypotheses.
Inductive arguments are also used frequently and effectively in academia and the practice of law. In fact, lawyers almost always use inductive arguments and provide evidence that seems irrefutable to support those arguments. Their reasoning is aimed at establishing a logical relationship between known facts. They can draw a strong conclusion and support it with the available evidence.
Depending on the strength of the lawyer's arguments and the validity of the evidence they present, the listener -- such as the judge or jury -- will assess which argument is sound and which one is unsound. These factors determine whether the defense or prosecution will win the case.
Types of inductive reasoning
There are several types of inductive arguments, including the following:
Inductive generalization
A generalized inductive argument observes a series of random samples of data and then draws general conclusions about a larger population of data.
Example
- Premise: The right-handed musicians I have seen play right-handed guitars.
- Conclusion: All right-handed musicians probably play right-handed guitars.
Statistical generalization
In this type of argument, statistics based on a large and usually random sample set are used to support conclusions. Since the statistics are quantifiable and aren't vague or unsupported, such generalizations usually strengthen the conclusion.
Example
- Premise: Worldwide, about 2% of people are born with red hair.
- Conclusion: A randomly selected person probably won't have red hair.
Causal inference
A causal argument creates a causation -- or cause and effect -- link between the premise and the conclusion.
Example
- Premise: All the sweets in this box are doughnuts. I just saw a jam-filled doughnut.
- Conclusion: Therefore, all the doughnuts in the box are probably jam-filled.
Bayesian reasoning
In Bayesian reasoning, statistical reasoning -- simply put, probability -- is used to account for additional or new information. This kind of inductive argument is frequently used in the following disciplines:
- Law.
- Engineering.
- Medicine.
- Science.
- Sports.
Example
- Premise: Baseball talent assessors evaluate a host of statistics on hitters, such as at-bat velocity of balls hit and bat angle, to determine the probability of success for a player they're considering acquiring.
- Conclusion: Player XYZ excels in all categories when compared to their peers. The team signs this player.
Analogical or analogous reasoning
The arguer concludes that because two groups have some shared property or similarity, they're also likely to share another property or similarity.
Example
- Premise: John and Will are left-handed and pitch left-handed. Bob is also left-handed.
- Conclusion: Hence, Bob is likely to be a left-handed pitcher.
Predictive reasoning
A predictive inductive argument involves making some prediction about the future. Thus, a conclusion is drawn based on previously known or past information.
Example
- Premise: Sunflowers always bloom in summer in this valley.
- Conclusion: Therefore, sunflowers will bloom in this valley next summer.
Analogical reasoning
Analogical, or comparative, reasoning is used when the arguer arrives at a conclusion about something based on its similarities to another thing.
Example
- Premise: Scientists test a new drug in the laboratory and finally go to successful human trials.
- Conclusion: The drug is safe for use by humans.
Drawbacks of inductive arguments
An inductive argument isn't capable of delivering a binary, true-or-false conclusion. This is because such arguments are often based on circumstantial evidence and a limited number of samples. Because of this limitation, an inductive argument can be disproven by a single negative or weak sample.
Inductive reasoning is also susceptible to failure because of cognitive bias, which occurs when the investigator only sees what they expect to support their argument. This could result in a weak argument or unsound conclusion and make the listener doubt the reliability of the arguer's beliefs.
Inductive arguments can be convincing and show that a conclusion is likely to be true. However, they don't provide absolute proof.
It's not enough for AI to be right or wrong. Learn how Ron Brachman from Cornell University and Hector J. Levesque from the University of Toronto propose programming AI with human psychology to react using common sense.