What is employee monitoring?
Employee monitoring is when businesses monitor employees to improve productivity and protect corporate resources. The main intention is to prevent unacceptable behavior in the first place and, should that effort fail, to curtail the behavior before it can harm the business.
Research indicates that around 30% to 40% of employees' internet usage during work hours is not work-related. Additionally, a significant portion of employees engage in activities such as online shopping and social media during work hours, contributing to productivity loss. In the United States, the annual loss in productivity due to non-work-related internet activities is substantial.
With the rise of remote work, employee monitoring has become even more critical as companies seek to ensure productivity and security outside traditional office environments.
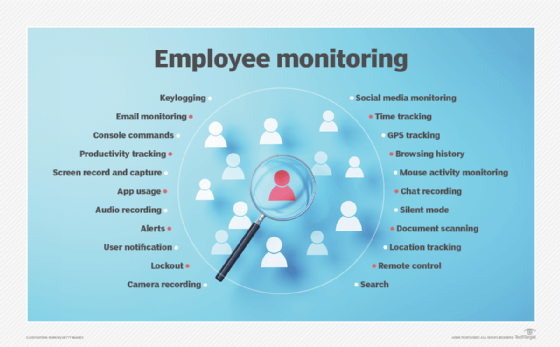
Employee monitoring methods
A few of the many monitoring methods include keystroke logging, wiretapping, GPS tracking and internet monitoring, which includes surveillance of employees' web surfing, email, instant messaging and interaction on social networking sites.
Modern employee monitoring tools also use artificial intelligence and machine learning to analyze employee behavior patterns and identify potential security threats or productivity issues.
Legal considerations of employee monitoring
One important consideration for employee monitoring is the question of whose equipment they are using and when they're using it.
It's legal for employers to monitor staff's use of corporate-owned computers, smartphones and other devices during business hours, but if the employee owns the equipment or they are on their own time, that's another matter. The issue of legality becomes murky when employers monitor staff using corporate-owned devices outside of work hours or using their own devices during work hours.
Employers must navigate various legal frameworks and privacy laws, such as the General Data Protection Regulation (GDPR) in Europe, which imposes strict requirements on monitoring practices and data protection.

Developing an acceptable employee monitoring use policy
Before deploying an employee monitoring program, organizations should clarify the terms of acceptable and unacceptable use of corporate resources during work hours and develop a comprehensive acceptable use policy (AUP) that staff must agree to.
The AUP should clearly outline the extent and purpose of monitoring, the types of data collected, and how the data will be used and protected. Transparency and communication with employees are key to ensuring compliance and maintaining trust.
Ultimately, employee monitoring is a vital practice for businesses aiming to enhance productivity and safeguard resources. By implementing effective monitoring methods and adhering to legal requirements and acknowledging ethical concerns, organizations can create a secure and efficient work environment.
Employee monitoring software, colloquially known as bossware, tracks every conceivable productivity-related metric. Businesses need clear goals for employee monitoring to cut through the noise. Learn everything employees should know about employee monitoring software. Also, see how for some companies' employee productivity monitoring tools are part of their 'trust but verify' approach to remote work.
See also: Hawthorne effect.
