What is a threat intelligence feed?
A threat intelligence feed, also known as a TI feed, is an ongoing stream of data related to potential or current threats to an organization's security. Threat intelligence feeds provide information on attacks, including zero-day vulnerabilities, malware, botnets and other security threats. They're vital components of security infrastructure, helping identify and prevent security breaches. Threat intelligence can be used to implement more granular security policies, as well as to identify potential characteristics or behaviors associated with a threat.
Intelligence, in the military, business, security and other contexts, is information that provides an organization with decision support and, possibly, a strategic advantage. Threat intelligence is a field within information security that focuses on collecting, analyzing and sharing data to help organizations gain visibility into their digital risks.
Threat intelligence is gathered to help organizations understand emerging threats in the cybersecurity landscape, such as advanced persistent threats and exploits. Threats can also come from internal and partner threat actors, but the emphasis is on outside sources that might cause the most damage to an organization's environment.
Researchers, including information security analysts and officers, collect data about possible threats from public and private sources. They analyze and correlate the data and create curated lists, or feeds, of potentially dangerous activity. Companies and security professionals use this threat information to determine potential issues and when they might need to respond to a cyberthreat.
This article is part of
What is threat detection and response (TDR)? Complete guide
What is threat intelligence data and why is it important?
Threat intelligence data, also known as indicators of compromise (IOCs), are the pieces of information that comprise threat intelligence feeds. It's an important element in defending against modern cyberattacks and is comprised of machine-readable information on suspicious domain names, data breaches and threat indicators. Actionable threat intelligence data is gathered from a variety of sources, including open source intelligence, social media, forums and even the dark web.
Security researchers and security operations centers often use threat intelligence feeds. The data helps organizations identify malicious actors' tactics, techniques and procedures (TTPs), allowing organizations to prepare against potential attacks before they occur. Cyberthreat intelligence feed data is often divided into various types, including tactical, operational and strategic, each of which serves a different role in protecting an organization.

How is threat intelligence data collected?
Threat intelligence feeds come from various sources. There are free indicator feeds, paid feeds, bulletins, internal intelligence gathering and strategic partnerships. Organizations within the network security community, including the SANS Institute Internet Storm Center and the U.S. Department of Homeland Security's Automated Indicator Sharing program offer free, open source feeds. Such feeds are sometimes characterized as threat data rather than threat intelligence because the data hasn't been analyzed and processed, as the term intelligence implies.
Other options include commercial products that provide vetted and aggregated data, as well as information-sharing communities specific to cybersecurity threats in particular industries or focus areas. Free feeds need the most checking to ensure accuracy, but even information from paid feeds and bulletins should be subjected to regression testing and have Internet Protocol (IP) addresses and domains investigated to avoid accidentally blocking too many addresses.
Types of threat intelligence feeds
There are several types of threat intelligence feeds and frameworks:
- Open source threat intelligence feeds are freely accessible and provide basic, public information on cyberthreats.
- Tactical threat intelligence describes in detail how cyberattacks occur, threat hunting techniques and IOCs.
- Operational threat intelligence tracks active campaigns and TTPs.
- Strategic threat intelligence is high-level intelligence providing insight into long-term threats and ways to improve security strategies.
- Machine-readable threat intelligence provides automated feeds that integrate with security information and event management (SIEM) systems for real-time threat detection.
- Threat indicator threat intelligence focuses on key indicators like compromised domain names, false positives and malicious metadata.
- Commercial threat intelligence is vendor-provided paid feeds.
Features of threat intelligence feeds and platforms
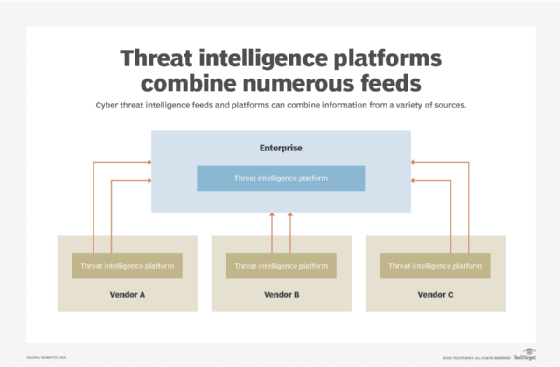
Threat intelligence platforms have emerged to help businesses and security professionals view multiple threat intelligence feeds at once. They also let users work with other security products and tools. Common features of platforms include the following:
- Security analytics. The main goal of threat intelligence platforms is to provide an organization with a single, unified interface to streamline the collection and analysis of threat intelligence data. Platforms integrate with security tools like SIEM systems, next-generation firewalls and endpoint detection and response products. Security analysts or IT security staff may need to be specially trained on the platform to manage data feed information.
- Consolidated data feeds. Intelligence platforms compile data feeds from multiple sources, such as a vendor's own global database and publicly available feeds. Examples of consolidated feeds include IP addresses, malicious domains and URLs, phishing URLs and malware hashes.
- Alerts and reports. Platforms typically provide real-time alerts and generate reports based on daily, monthly and quarterly data. The reports include information on emerging threats and threat actor motives.
What are threat intelligence feeds used for?
Business and IT leaders can use threat intelligence feeds and the data they provide to improve many aspects of information security, including the following:
- Security operations. A threat intelligence program can give security operations teams the ability to identify, disrupt and develop effective strategies for defending against attacks. Threat intelligence can also help security teams contain attacks that are already underway.
- Incident response. Security analysts use threat intelligence to identify threat actors, their methods and the potential threat vectors they use to gain access to systems. Armed with this knowledge, security staff can then predict which systems are most at risk and focus their incident response resources and strategy on protecting those systems.
- Vulnerability management. Threat intelligence can help security professionals combat threats by providing accurate and timely information on new and emerging threats, vulnerabilities and exploits.
- Risk analysis. Threat intelligence provides contextual data for organizations when evaluating their risk profile. It's especially helpful for those using risk analysis and risk modeling to determine investment priorities.
- Fraud prevention and mitigation. Threat intelligence helps with fraud prevention by giving companies the knowledge they need to identify threats before they cause major damage. For example, organizations might use threat intelligence to prevent typosquatting, compromised data and payment fraud.
- Security leadership. Security leaders can benefit from using threat intelligence as a critical resource to assess business and technical risks and communicate those risks to management.
Threat intelligence feeds vs. threat feeds
Threat intelligence feeds and threat feeds both play important roles in detecting and protecting against cyberthreats. Threat feeds typically focus on delivering raw data like compromised domain names, blocklist entries and specific IOCs that can signal a cyberattack. These feeds are usually machine-readable and integrated directly into SIEMs or other cybersecurity platforms.
On the other hand, threat intelligence feeds offer more context as part of their data. This can include known TTPs of cyberattackers and high-level threat reports from experts. Threat intelligence feeds can go beyond threat feeds' raw data and offer actionable intelligence on which to base more structured insight and strategies for defending against attacks.
Threat intelligence feed vendors
According to G2 ratings, the top threat intelligence feed providers in 2024 include the following:
- RSA.
- Sophos Professional Services.
- Webroot Threat Intelligence.
- Cisco Security Services.
- OpenText.
- Nomic Networks.
- Kaspersky Cybersecurity Services.
- Malware Patrol.
- Ernst & Young.
- Microsoft Defender Experts for XDR.
It's important to keep threat intelligence strategies up to date. Enhance your organization's threat intelligence program and security posture with proactive approaches to formalizing and automating it, as well as making use of managed services.