command-and-control server (C&C server)
What is a command-and-control server?
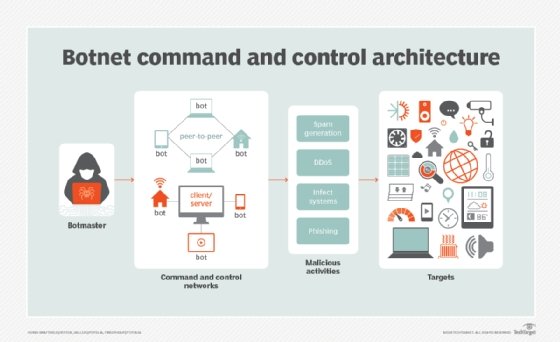
A command-and-control server (C&C server) is a computer that issues directives to digital devices that have been infected with rootkits or other types of malware, such as ransomware. C&C servers can be used to create powerful networks of infected devices capable of carrying out distributed denial-of-service (DDoS) attacks, stealing data, deleting data or encrypting data in order to carry out an extortion scheme.
In the past, a C&C server was often under an attacker's physical control and could remain active for several years. Today, C&C servers generally have a short shelf life; they often reside in legitimate cloud services and use automated domain generation algorithms to make it more difficult for law enforcement and ethical malware hunters to locate them.
How does a C&C server work?
For a C&C attack to materialize, a malicious remote server known as a C&C server must gain a foothold into an already infected machine. Most devices such as laptops, desktops, tablets, smartphones and IoT devices are vulnerable to this type of attack.
Command-and-control server attacks are typically carried out through the following channels:
- Phishing emails that trick users into clicking malicious links or attachments.
- Malvertising that distributes malware by injecting malicious code inside digital advertisements.
- Vulnerable browser extensions and plugins that may introduce malicious scripts into interactive webpages to redirect, block and steal information entered into online forms.
- Malware that's directly installed on a device to initiate malicious commands.
After the successful invasion of a device, a threat actor establishes communication with the malicious C&C server to send instructions to the infected host and form a malicious network. A malicious network under a C&C server's control is called a botnet and the network nodes that belong to the botnet are sometimes referred to as zombies. Beaconing can also be used between the infected device and the C&C server to deliver instructions or additional payloads.
Once the infected host starts executing the commands sent by the C&C server, further malware is installed, which gives the threat actor full control over the compromised machine. To avoid detection by firewalls, threat actors might try to blend C&C traffic with other types of legitimate traffic, including HTTP, HTTPS or domain name system.
C&C server malicious use cases
Even with cybersecurity and threat intelligence mechanisms in place, organizations may not always effectively monitor outbound communications. This may let certain outbound communication channels -- including phishing emails, lateral movements or infected websites -- weave their way into a network and inflict damage.
C&C servers act as the headquarters where all activities related to the targeted attack report back. Besides installing malware, a threat attacker may use a C&C server to carry out the following malicious activities:
- Data theft. A threat actor can move an organization's sensitive data, such as financial records, to the C&C server.
- Reboot devices. Cybercriminals can use a C&C attack to disrupt usual ongoing tasks by rebooting compromised machines.
- Network shutdown. Threat actors can use these attacks to bring down either a few machines or shut down an entire network.
- DDoS attacks. Hackers may try to disrupt web services or bring down a website by sending a massive number of DDoS requests to the server's IP address. This can cause a traffic jam, which prevents legitimate traffic from accessing the network.
- Misuse of future resources. A C&C attack may be carried out to disrupt legitimate applications to negatively affect future resources. One example of this is the SolarWinds breach from 2020, where threat actors secretly transmitted malicious code into the company's software system, which was then inadvertently sent out by SolarWinds as part of its software updates to customers. The code stayed dormant for months, creating a backdoor to the victims' machines, and was used by threat actors to spy and install additional malware.
- Advanced persistent threat (APT). An APT may not launch immediately or will stay dormant after infecting a certain host, waiting for a better attack opportunity. For example, a threat actor may try to sell the C&C server or a hosting package to the victim to generate more profit.
Popular botnet topologies
A botnet is a group of malware-infected and internet-connected bots that are controlled by a threat actor. Most botnets have a centralized command-and-control architecture, although peer-to-peer (P2P) botnets are on the rise due to their decentralized nature, which offers more control to the threat actors.
Popular botnet topologies include the following:
- Star topology. The bots are organized around a central server.
- Multi-server topology. There are multiple C&C servers for redundancy.
- Hierarchical topology. Multiple C&C servers are organized into tiered groups.
- Random topology. Co-opted computers communicate as a P2P botnet.
- P2P. Each bot operates independently as both a client and a server. Due to the lack of centralized control, a P2P botnet architecture is more aggressive and harder to detect.
In a traditional botnet, the bots are infected with a Trojan horse and use Internet Relay Chat (IRC) to communicate with a central C&C server. These botnets are often used to distribute spam or malware and gather misappropriated information, such as credit card numbers. Since IRC communication is typically used to command botnets, it's often guarded against. This has motivated cybercriminals to find more covert ways for C&C servers to issue commands. Alternative channels used for botnet commands include JPEG images, Microsoft Word files and posts from LinkedIn or Twitter dummy accounts.
Botnets can fuel DDoS attacks by taking advantage of IoT vulnerabilities. Learn how hackers create an IoT botnet and initiate a DDoS attack to infect networks.
