reinforcement theory
What is reinforcement theory?
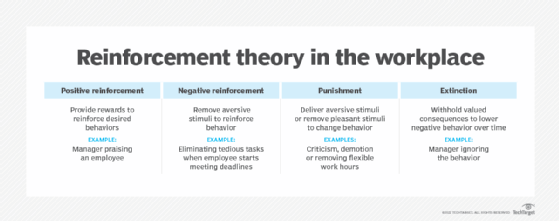
Reinforcement theory is a psychological principle suggesting that behaviors are shaped by their consequences, and that individual behaviors can be changed through reinforcement, punishment and extinction.
Behavioral psychologist B.F. Skinner was instrumental in developing modern ideas about reinforcement theory. According to Skinner, a person's internal needs and drives are not important areas of concern because their current behaviors follow the law of effect and are based on the consequences of former behaviors. This means that behaviors can be altered or manipulated over time.
How can managers use reinforcement theory to motivate employees?
The reinforcement theory of motivation aims to motivate staff through reinforcement, punishment and extinction. Reinforcement theory in the workplace can be positive or negative as long as it reinforces the desired employee experience and behavior. Managers using reinforcement theory to motivate staff should explain to employees which behaviors will result in positive feedback.
Here are several behavioral concepts that are common in business management, human resources management, marketing, social media, website and user experience design, and end-user training.
Positive reinforcement
A key idea in the reinforcement theory of motivation is that positive reinforcement with rewards reinforces desired behaviors. For example, providing an employee with extra days off for good performance in their job.
Negative reinforcement
Negative reinforcement involves the removal of aversive stimuli to reinforce the target behavior. For example, a manager can stop assigning tedious tasks to an employee when the employee starts meeting deadlines.
Punishment
Positive punishment involves the delivery of an aversive stimulus, such as criticism, to affect behavior. Meanwhile, negative punishment removes a pleasant stimulus -- flexible work hours, for example -- to do the same.
Extinction
Like punishment, the goal of extinction is to lower the occurrence of undesired behaviors. In this scenario, valued consequences can be withheld to reduce the probability of a specific learned behavior from continuing. The idea is to stop a learned behavior over time. For example, an organization might stop paying overtime to discourage employees from staying late and working too many extra hours.
However, extinction can also reduce desired behavior by not offering positive reinforcement when the desired behavior occurs. For example, if a manager stops praising an employee for completing tasks quickly, the employee might stop this behavior. To avoid unwanted extinction, managers must continue to reward desired behaviors.
What is differential reinforcement theory?
Like the reinforcement theory of motivation, differential reinforcement theory proposes that people are more likely to continue behaviors that are reinforced and discontinue behaviors that are not.
What is a reinforcement schedule?
A reinforcement schedule describes the timing of the behavioral consequences of a given behavior. There are two broad types of reinforcement schedules -- continuous reinforcement and intermittent reinforcement.
Continuous reinforcement
When behavior is reinforced every time it occurs, this is called continuous reinforcement. A continuous reinforcement schedule is the quickest way to establish new, desired behaviors or eliminate undesired behaviors. However, continued reinforcement isn't practical for a corporate environment, so employers tend to apply intermittent or scheduled reinforcement in corporate settings.
Intermittent reinforcement
Intermittent reinforcement involves the delivery of rewards on an occasional and unpredictable basis. This approach tends to promote the continued efforts of an employee for more extended periods without a payoff.
Slot machine payouts are an example of intermittent reinforcement, as they provide adequate rewards over time to keep players motivated. Similarly, managers can use a lottery system to reward employees. When employees meet a specified performance level, they become eligible to enter a lottery. This approach could produce the desired higher level of performance from employees.
Leading intermittent reinforcement theories include the following:
- Fixed-interval schedule. Fixed-interval schedules reinforce desired behaviors in accordance with a set time. For example, weekly paychecks follow a fixed-interval schedule. However, fixed-interval schedules are not considered the best approach to achieve the desired behavior, since they are often subject to rapid extinction.
- Fixed-ratio reinforcement. The purpose of a fixed-ratio schedule of reinforcement is to use an action multiple times to achieve a desired outcome. For example, a mouse can be trained to press a button three times to get a reward. Once the mouse understands the relationship between the action and the prize, it will push the button three times to receive a reward. Similarly, if a manager pays a factory worker for manufacturing a set number of products, the worker will repeat this process to receive the payment. Fixed-ratio punishments can also be used to discourage undesired behaviors. For example, "three strikes and you're out." But while fixed-ratio schedules can help when teaching a new task, they can also lead to burnout.
- Variable-interval schedule. Variable-interval reinforcement schedules reinforce desired behaviors over varied periods of time. This helps elicit behavioral change without the risk of extinction. For example, promotions and performance recognition at the workplace tend to fall under a variable-interval schedule.
- Variable-ratio reinforcement. The variable-ratio reinforcement schedule changes the number of desired behaviors needed for reinforcement depending on the situation. Special awards and bonuses in an organizational setting are excellent examples of how a variable-ratio reinforcement schedule can be used in the workplace. Variable-ratio reinforcement can also produce a desired behavioral change that is highly resistant to extinction.
What is Gray's reinforcement sensitivity theory?
Developed by renowned British psychologist Jeffrey Alan Gray, reinforcement sensitivity theory suggests that there will be individual differences in the way people respond to punishment and reinforcement stimuli due to unique sensitivities of the brain. Proponents of the theory believe that these differences underlie the personality dimensions of conditions like anxiety, extraversion and impulsivity.
What is the reinforcement theory of learning?
The reinforcement theory of learning is a popular iterative process in machine learning. In this case, smart algorithms try to maximize some value based on rewards received for making the right decision under uncertainty.
See also: Guide to building an effective employee experience strategy
