Internet Engineering Task Force (IETF)
What is the Internet Engineering Task Force (IETF)?
The Internet Engineering Task Force (IETF) is the body that defines standard operating internet protocols such as TCP/IP.
The IETF is an open standards organization supervised by the Internet Society's Internet Architecture Board (IAB). However, prior to 1993, the IETF was supported by the United States federal government.
IETF organizational structure
IETF members are volunteers, drawn from the Internet Society's individual and organization membership. Members form working groups and area directors appoint a chairperson (or co-chairs) to deal with a particular area discussed in IETF meetings.
Ultimately, the area directors, working groups and chairs form the Internet Engineering Steering Group (IESG), which is responsible for creating internet standards expressed in the form of Requests for Comments (RFCs).
Decisions on a standards track are made by rough consensus instead of formal voting protocols.
As part of overseeing the work of the IETF, the IAB supervises the RFC editor and offers technical direction to ensure the smooth operation of the internet.
They are also responsible for the Internet Research Task Force (IRTF), an organization parallel to the IETF that focuses on long-term research on issues relevant to the evolution of the internet.
Additionally, the Internet Assigned Numbers Authority (IANA), an organization responsible for overseeing global IP address allocation, root zone management in the Domain Name System (DNS), autonomous system number allocation, and other Internet Protocol-related symbols and numbers, also works closely with the IETF.
Funding for IETF activities is provided by meeting dues, sponsors and proceeds provided by organizational membership to the Public Interest Registry.
IETF areas of focus
The common areas of focus for the IETF include:
- applications
- general
- infrastructure
- internet
- operations and management
- real-time applications
- routing
- security
- transport
The internet standards process includes proposing specifications, developing standards based on agreed-upon specifications, coordinating independent testing and revising proposals based on testing results.
Before proposals become official standards, multiple interoperable implementations must be successful. In fact, protocols can be used in many different systems or as running code used to flesh out system architectures.
IETF notable projects
In addition to the IETF standards process, the group also coordinates a number of other activities.
Hackathons
One such example is hackathons hosted by the IETF which are geared toward improving the interoperability and quality of the internet.
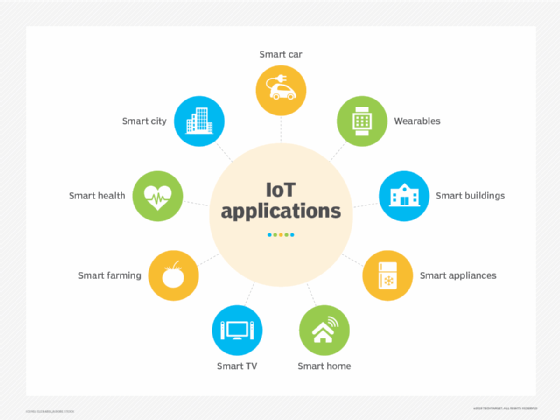
Internet of things (IoT)
The IoT is a network of software, electronics and sensors that facilitate data exchange and communication for manufacturers, operators and their connected devices. Multiple IETF working groups have developed the internet governance standards that regulate the IoT.
Legislation
The IETF also cooperates with a number of standards bodies that seek to regulate the internet and make it safer. Some examples include the International Standards Organization (ISO), the International Telecommunication Union (ITU) and the World Wide Web Consortium (W3C).
