weak tie theory
What is weak tie theory?
Weak tie theory is the proposition that acquaintances are likely to be more influential than close friends, particularly in social networks.
Where did the weak tie theory originate?
The weak tie theory originated as a concept in sociology that explains the role of weaker social ties in facilitating communication and information exchange.
It was first introduced by Mark Granovetter in his 1973 paper, "The Strength of Weak Ties," in which he argued that, while strong ties (i.e., close relationships with friends and family) are important for emotional support, weak ties (i.e., more distant or casual relationships) are more valuable in terms of providing access to new information and opportunities.
According to the weak tie theory, an individual's strong ties are typically composed of people who are similar to them in terms of demographics, values and interests. These individuals tend to share a lot of the same information and resources, and as a result, they are not likely to be sources of novel or diverse information.
In contrast, weak ties are typically composed of people who are less like us and who have access to different social circles and networks. As a result, they are more likely to be sources of novel and diverse information, which can be especially valuable for individuals looking to find a new job or pursue new opportunities.
Applications for the weak tie theory in interpersonal relationships
One of the key applications of weak tie theory is in the realm of interpersonal relationships. In particular, it suggests individuals should make an effort to cultivate weak ties in order to gain access to new information and opportunities.
This can be especially important for people who are looking to advance their careers or pursue new goals, as weak ties can provide valuable insights and introductions that may not be available through strong ties alone.
Applications for the weak tie theory in the enterprise
Within the enterprise, a department or a project team could be considered a group of strong ties. According to weak tie theory, encouraging intergroup communication and collaboration is likely to increase the dissemination of ideas and information and promote creativity and innovation.
Creating more connections among employees increases the flow of ideas -- and that is especially true for employees that have no apparent need to communicate.
Promoting the creation of weak ties might generate revenue-generating opportunities, cost-cutting strategies, recommendations for productivity enhancement and improvements in product development, among endless other possibilities.
Applications for the weak tie theory in social media
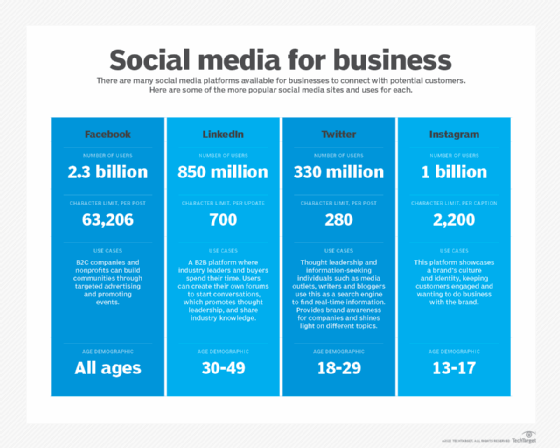
Weak tie theory also has important implications for social media sites, such as Facebook, LinkedIn and Twitter, which can serve as powerful tools for building and maintaining weak ties.
For example, LinkedIn is a social media platform built to support professional networking, and it enables individuals to connect with a wide range of people in their field, including both strong and weak ties. By actively using LinkedIn and other social media services to build weak ties, individuals can gain access to new information and opportunities that may not have been available to them otherwise.
Other applications for the weak tie theory
In addition to its applications in interpersonal relationships, the enterprise and social media, weak tie theory has also been used to understand the spread of information and ideas within social networks.
According to the theory, weak ties are more likely to facilitate the spread of novel and diverse information, as they are more likely to be connected to different social circles and networks. This can be especially important in times of crisis when it is critical for individuals to have access to accurate and up-to-date information.
Weak tie theory has also been applied to the study of social movements and political activism. In particular, it has been used to explain how social movements and political campaigns can gain traction and spread through weak ties, as these ties are more likely to connect individuals to different social circles and networks.
So, are strong ties bad?
Strong ties aren't bad per se, but because networks of strong ties are self-limiting, they can lead to what is sometimes called a filter bubble, a restriction of news, information and ideas that results from things like search personalization and maintaining connections mostly within homogenous groups of people.
The limitation can stem from confirmation bias, which is the human tendency to seek out sources of information that support our existing perspective and beliefs. A larger social network, including numerous weak ties, on the other hand, is likely to challenge that tendency and support critical thinking.
Explore the three pillars of successful collaboration in the workplace, learn ways to spot disinformation on social media, see the differences between generalists vs. specialists and check out why the co-innovation partnership model emerges as best practice.