Chaos Monkey
What is Chaos Monkey?
Chaos Monkey is a software tool Netflix engineers developed to test the resiliency and recoverability of its Amazon Web Services (AWS) infrastructure.
In software engineering, building resilient systems that can withstand unexpected errors and recover quickly is essential. Chaos Monkey was designed to intentionally introduce disruptions to a system, simulating real-world failures and testing the system's resilience.
By introducing disruptions through Chaos Monkey, engineering teams can identify vulnerabilities and address them proactively before they impact users or customers.
Chaos Monkey was an original component of Netflix's Simian Army, a collection of software tools designed to test the AWS infrastructure. The software is open source to allow other cloud services users to adapt it for their use.
Chaos engineering with Chaos Monkey
Chaos engineering is the practice of intentionally creating disruptions in systems to identify and address vulnerabilities proactively. Chaos Monkey serves as a critical tool in enhancing chaos engineering; it enables engineering teams to simulate failures across multiple configurations and monitor the system's behavior in real time.
Another way to refer to this is purposeful disruption. Unlike traditional testing tools that rely on predefined scripts and expected outcomes, Chaos Monkey is designed to introduce purposeful disruptions into a system by shutting down virtual machines that are running services, simulating real-world failures.
With its intentional disruptions, Chaos Monkey offers a more realistic evaluation of a system's resilience. The approach underscores the importance of resilience testing and the need for constantly exposing systems to disruptions to prevent critical failures.
Key features of Chaos Monkey
Key features of Chaos Monkey include the following:
- Random failure injection. Chaos Monkey randomly selects and injects failures into a system, simulating real-world scenarios and forcing the system to handle unexpected failures.
- Fault tolerance testing. By continuously injecting failures, Chaos Monkey tests the system's fault tolerance and ability to recover from failures by triggering system mechanisms, like autoscaling, failover and redundancy.
- Automated testing. Chaos Monkey enables scheduled and automated testing, ensuring that failure scenarios are consistently introduced into the system to uncover weaknesses and provide continuous feedback on resilience.
- Customizable chaos. Chaos Monkey provides the ability to customize the types of failures injected into the system so organizations can test specific failure scenarios based on their infrastructure and architecture.
- Cloud-native support. Chaos Monkey works with cloud-native architectures and services, making it easy to incorporate into systems deployed on cloud platforms, like AWS, Azure or Google Cloud.
Randomness for realistic scenarios
Chaos Monkey uses randomness, simulating real-world scenarios, to enhance the quality of results. By repeatedly introducing disruptions, often at random times, Chaos Monkey ensures that resilience testing is comprehensive and realistic.
This approach emphasizes the importance of continued testing and the need to expose systems to failures continuously.
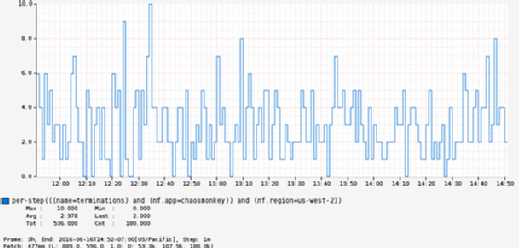
Continuous monitoring and reporting
Chaos Monkey offers continuous feedback on system behavior, enabling engineering teams to evaluate the system's resilience and identify areas that require improvement before they escalate into more significant issues.
Through continuous monitoring, Chaos Monkey provides teams with a detailed understanding of the system's behavior during disruptions, shedding light on how different components interact and respond to failures. This information is invaluable in identifying areas for improvement and designing more resilient architectures.
Chaos Monkey generates comprehensive reports that highlight system vulnerabilities and areas of concern, detailing how the system reacts to different types of disruptions and failures. This can help teams prioritize issues and address them effectively.
Chaos Monkey's reports include metrics such as response time, error rate, availability and resource utilization during disruptions. This data can help teams quantify the system's performance and assess the impact of disruptions on users or customers. By analyzing the reports, teams can pinpoint specific vulnerabilities, understand root causes and develop targeted solutions to mitigate risks.
Guidelines to implement Chaos Monkey effectively
Implementing Chaos Monkey in a system effectively requires careful planning and adherence to certain guidelines. These guidelines ensure that Chaos Monkey tests the system's resiliency without negatively impacting critical business operations.
Organizations can maximize the benefits of Chaos Monkey, while minimizing any potential risks, by following these best practices:
- Start with a well-designed and stable system. Before introducing Chaos Monkey, it's essential to have a well-designed, stable system. Chaos Monkey is not a solution for fixing fundamental design flaws or instability issues. It works best when used in systems that are already sufficiently resilient to handle unexpected failures.
- Gradually introduce chaos. Chaos Monkey should be gradually introduced into the system, starting with low-impact disruptions and progressively increasing the level of chaos. This enables teams to gauge how the system responds and ensures that any adverse effects can be addressed promptly. Gradual introduction also helps teams gain confidence in the system's ability to handle failures and builds resilience over time.
- Define targeted failure scenarios. To test system resiliency effectively, define specific failure scenarios that align with the system's architecture and potential weak points. You can simulate network failures, server crashes or service disruptions. By customizing failure scenarios, organizations can focus on testing areas of concern and gain insights into the system's response to specific failures.
- Schedule regular chaos sessions. Incorporate Chaos Monkey into the system's operations as a regular, scheduled practice. By scheduling chaos sessions, teams can ensure that failures are consistently introduced and tested. This helps identify and fix vulnerabilities early in the development lifecycle and provides continuous feedback on system resiliency.
- Monitor and analyze system behavior. Continuous monitoring and analysis of the system's behavior during chaos sessions are crucial for understanding its response to failures. This data provides insights into the system's performance under stress and helps identify areas for improvement.
- Include autorecovery mechanisms. Chaos Monkey helps assess the system's ability to recover from failures autonomously. To enhance resiliency, include autorecovery mechanisms, such as automatic scaling, redundant components and failover systems. These mechanisms ensure that the system can adapt to failures and maintain business continuity.
- Involve the entire team. Implementing Chaos Monkey effectively requires collaboration and involvement from the entire team, including developers, operations and quality assurance. This ensures that everyone understands the purpose of Chaos Monkey, actively participates in chaos sessions, and contributes to the identification and resolution of vulnerabilities.
- Document and learn from findings. Document the findings and insights gained from Chaos Monkey sessions. This documentation should include details about vulnerabilities discovered, fixes implemented and lessons learned. By maintaining a knowledge base, teams can build on their learnings and continually improve the system's resiliency.
Implementing Chaos Monkey effectively requires a disciplined approach and a commitment to continuous improvement.
By following the suggested guidelines, organizations can use Chaos Monkey to identify and address vulnerabilities, strengthen system resilience and enhance overall operational reliability.
See how Chaos Monkey testing can help with microservices, and explore how to choose the right chaos engineering tools. Read about tools to conduct security chaos engineering tests and ways to test in production promptly and productively.
