XSL (Extensible Stylesheet Language)
What is XSL (Extensible Stylesheet Language)?
XSL (Extensible Stylesheet Language) is a family of standards that specifies how to define Extensible Markup Language (XML) document transformation and presentation. The standards are published by the World Wide Web Consortium (W3C), an international community that develops specifications related to web architecture, design, applications and other web technologies.
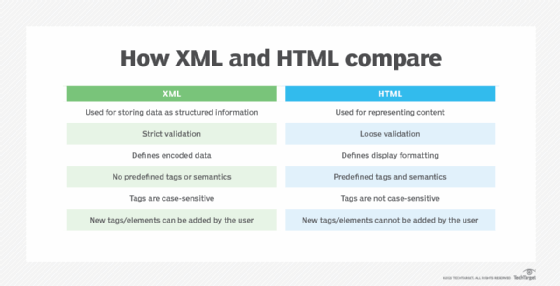
Originally, XSL was a single standard that detailed how to display an XML document of a given type, similar to how cascading style sheets (CSS) supports Hypertext Markup Language (HTML). In fact, the XSL standard was based in part on CSS, level 1, as well as on the Document Style Semantics and Specification Language standard. The W3C published the first working draft of the XSL standard in August 1998.
Since its initial publication, the XSL standard received several updates and was eventually divided into three parts -- XSL Transformations (XSLT), XML Path Language (XPath) and XSL Formatting Objects (XSL-FO) -- which together make up the current XSL family. Because there are now three parts, the acronym XSL is sometimes confused with one of those parts. For example, XSL and XSLT are often used interchangeably when describing XML transformations. Although this is generally not a problem, it is best to refer to the individual parts by their official names and use XSL to refer to the entire family of standards.
What is XSLT?
The XSLT standard defines a language for transforming XML documents into other XML documents or into formats such as HTML, Extensible HTML, text or JavaScript Object Notation (JSON). An XSLT document is essentially a stylesheet written in well-formed XML to provide specific styling information for one or more XML source documents. For example, an XSLT stylesheet might be used to tell a browser to format the data in an XML document as a table.
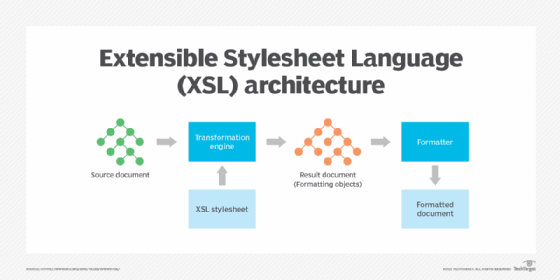
To use XSLT, you need an XSLT processor, a piece of software that applies the formatting rules defined in the XSLT stylesheet to the XML source document. The processor takes the XML and XSLT documents as input, parses the XML, applies the XSLT to the parsed data and generates an output document in the specified format, e.g., XML, HTML or text. An XSLT processor might be built into an application, included with a web browser or offered as a standalone tool.
The XSLT standard is developed by the W3C XSLT Working Group, which is currently working on the next version. The latest release of the standard is XSLT 3.0. However, XSLT 1.0 and XSLT 2.0 are still widely used. XSLT adheres to a declarative processing model, which describes the computational logic through constraints without defining the control flow. The W3C designed XSLT to work in conjunction with XPath, which provides a standard for navigating XML. Both XSLT and XPath share the same data model.
What is XPath?
The XPath standard defines a compact expression language used by XSLT and other languages to access or reference parts of an XML document. Its primary purpose is to address the nodes in XML trees and, as of XPath 3.1, in JSON trees. The W3C designed XPath to be embedded in a host language, such as XSLT or XML Query (XQuery). It uses path notation, rather than XML syntax, to navigate the hierarchical structure of XML documents.
The XPath data model -- its logical structure -- is defined in the W3C XQuery and XPath Data Model standard. The data model serves two purposes:
- to describe what information should be included in the input to an XSLT or XQuery processor; and
- to describe the permissible expression values in the XSLT, XQuery and XPath languages.
The basic building block in XPath is the expression, a string of Unicode characters made up of keywords, symbols and operands. Expressions identify elements in the XML hierarchical tree structure and make it possible to navigate that structure. XPath supports many types of expressions, such as path, conditional, arithmetic, concatenation and comparison expressions. The W3C XQuery Working Group and XSLT Working Group develop the XPath specification jointly. The latest release is XPath 3.1.
What is XSL-FO?
The XSL-FO standard defines a template-based vocabulary and expression language for specifying XML formatting semantics. The standard provides a type of markup language that can be used to define how information is laid out on a page and presented to the reader. XSL-FO is often used in conjunction with XSLT to apply formatting to the output from an XSLT processor. Because XSL-FO supports sophisticated document formatting, it is commonly used to generate PDF files from XML documents.
The latest release of XSL-FO 1.1 was published in December 2006. The W3C published a working draft of XSL-FO 2.0 in January 2012. At one time, the XSL Working Group was responsible for the XSL-FO standard, but that effort was taken over by the XML Print and Page Layout Working Group. However, the working group is no longer active because of a lack of participation, so the XSL-FO specification is currently not maintained. The group's charter ended in January 2013.
See also: XML Schema Definition, AJAX, SPML, BPEL , XACML , ebXML and Information and Content Exchange.
