What is YAGNI principle (you aren't gonna need it)?
YAGNI principle ("you aren't gonna need it") is a practice in software development that states that features should only be added when required. As a part of the extreme programming (XP) philosophy, YAGNI trims away excess and inefficiency in development to increase the frequency of releases and deliver value faster.
The principle helps developers avoid wasted effort on features that they assume will be needed at some point. The idea is that this assumption often ends up being incorrect. Even if a feature is desired, it still might turn out that the implementation is not necessary. The argument is that developers should not waste time on creating extraneous elements that might not be necessary and can hinder or slow the development process.
As YAGNI helps avoid spending time on features that might not be used, the main features of a program are better developed, and less total time is spent on each release. Much like the "worse is better" principle, YAGNI is against the development of extra features and helps avoid feature creep. Other popular programming principles include KISS ("keep it simple, stupid") and DRY ("don't repeat yourself").
YAGNI is one of the best-known principles of XP. This part of XP comes from the book Extreme Programming Installed, authored by Ronald Jeffries, Ann Anderson and Chet Henderson.
YAGNI in Agile development and why it is beneficial
The YAGNI principle is core to truly Agile development practice. Agile recognizes that it is better to deliver value as quickly as possible and respond to changing needs. This dovetails with releasing a minimum viable product (MVP).
YAGNI helps save time in several ways. It prevents developers from working on features that sound useful but are never used. In addition, even if the feature is needed later, the product is in the hands of the customer earlier and generates value for them sooner than if it were delayed to add all the features.

To illustrate, imagine you were programming an online shopping cart for a company, and you knew they had big year-end sales in December that you might need to add a feature to support. If it were ready without the sales feature in March, but it would take a month to program, adding it could mean the customer loses out on sales in March. When the time comes to add the sales feature, you will be ready to understand the changed market conditions as well.
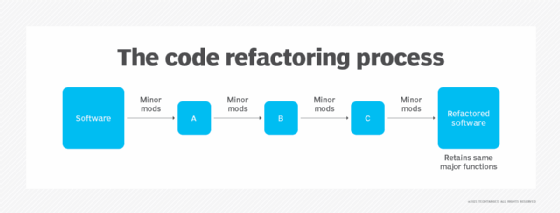
Clean code refactoring is essential to a successful YAGNI approach. When features are added, they need to be well integrated into the existing code by refactoring it. This helps to prevent code bloat and tech debt, often associated with evolving products or scope creep.
An additional advantage of YAGNI is that it keeps the codebase lean. After something is programmed, it takes work to maintain that code. It needs to be kept up to date, documented, debugged, and integrated with future releases. By not including features until they are needed, it prevents the costs associated with maintaining code that delivers little or no current value.
YAGNI and other programming practices
Extreme programming, of which YAGNI is a core approach, takes many best practice techniques to the logical extremes.
It is good practice to review code before it is integrated. XP promotes using pair programming during development for continual feedback and review. XP also includes continuous integration/continuous development (CI/CD), test-driven development (TDD), and coding smaller pieces.
SOLID, another programming practice, is a collection of principles that help to keep software reliable and easy to work with. It includes concepts like each piece of code should do one thing and be easy to extend but shouldn't be modified. By applying both SOLID and YAGNI, code can be kept clean and maintainable.
Learn how to make remote pair programming work, including best practices for remote pair programming, tools and style. See how TDD can benefit programmers, read about CI/CD best practices for DevOps teams, learn the phases of feature-driven development and check out must-know Agile terms.
