cluster quorum disk
What is a cluster quorum disk?
A cluster quorum disk is the storage medium on which the configuration database is stored for a Cluster computing network. The cluster configuration database, also called the quorum, tells the cluster which physical server(s) should be active at any given time. The quorum disk comprises a shared block storage device that allows concurrent read/write access by all nodes in a cluster.
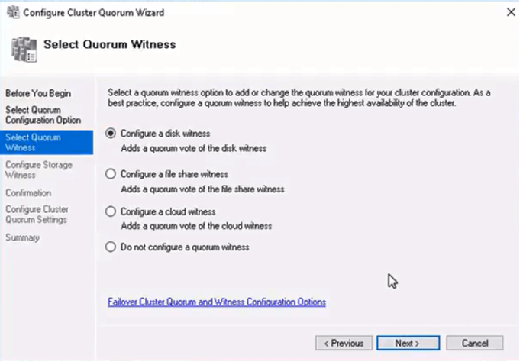
What is a cluster witness disk?
A cluster witness disk or quorum disk is a small, clustered disk found in the Available Storage cluster group. Cluster witness disks are highly available and enable failover between nodes.
The cluster quorum consists of the majority of voting nodes within an active cluster plus one additional node called a witness. A quorum witness may be a designated disk witness (a disk witness must also be a member) or a designated file share (a file share witness must also be a file share). Nodes do not have votes; only a file share witness has a vote.
In networking, clustering is the use of multiple servers to form what appears to users as a single highly available system. A webpage request is sent to a "manager" server, which then determines which of several other servers to forward the request for handling. Cluster computing load-balances the traffic on high-traffic websites. Load balancing involves dividing the work among multiple servers to accelerate processing so users see results faster.
Although clusters comprise multiple servers, users and other computers see the cluster as a single virtual server. The physical servers themselves are called cluster nodes. The quorum tells the cluster which node should be active at any given time and intervenes if communications fail between cluster nodes by determining which set of nodes gets to run the application at hand. The collection of nodes with the quorum keeps running the application while the other set of nodes is taken out of service.
What is a quorum disk in a Windows cluster?
In Microsoft Windows, a quorum disk (also known as a cluster disk) is a disk shared among all cluster nodes. It may be connected via Fibre Channel, InfiniBand, Small Computer System Interface, Serial Attached SCSI or similar protocols. It must be at least 512MB in size.
What is a quorum disk in the Red Hat cluster?
A Red Hat quorum disk cluster is a disk-based quorum daemon that provides supplemental heuristics to determine node fitness. With heuristics, you can determine factors that may be important to the operation of a node in the event of a network partition.
What happens if the quorum disk fails?
If the quorum disk in a Windows cluster becomes corrupted or fails, or if a rollback is required, a brand-new quorum disk can be created, and any required data may be restored. Quorum disks are protected using an image or local system job on the virtual server for the cluster center.
