haptics
What is haptics?
Haptics is the science of applying a sense of touch and control to interaction with computer applications. The word derives from the Greek haptein, meaning to fasten. Haptics offers an additional dimension to a virtual reality (VR) or three-dimensional (3D) environment. It's essential to the immersiveness of virtual environments.
By using special input/output devices -- such as joysticks or data gloves -- users can receive feedback from computer applications in the form of felt sensations in the hand or other parts of the body. In combination with a visual display, haptic technology is used to train people for tasks requiring hand-eye coordination, such as surgery, spaceship maneuvers and some manufacturing processes.
Haptics is also used for games in which players feel as well as see their interactions with images. For example, gamers might play tennis with another computer user somewhere else in the world. Both players can see the moving ball and use their haptic devices to position and swing their tennis rackets and feel the impact of the ball.
Reverse electrovibration, also known as virtual touch, is an area of haptics used with VR and augmented reality (AR) technology. Virtual touch facilitates electronic transmission of human tactile stimuli, allowing users to perceive the textures and contours of remote objects. Besides conveying the feel of everyday objects, haptic touch technology can also be used to enhance accessibility, for example, through the transmission of Braille characters.

Types of haptic technology
There are three main categories of haptic technology:
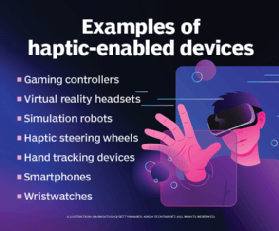
- Graspable. This type of haptics refers to handheld devices. Video game controllers and joysticks fall into this category. In robotics, haptic feedback can be added to help refine precise movements, such as surgeons practicing specific techniques.
- Touchable. Devices like mobile phones and VR technology use haptics to improve the user experience. For example, iPhone and other smartphone users receive tactile signals -- such as a vibration they can feel -- once they've successfully interacted with their phones. Meanwhile, VR users are more immersed in VR worlds when virtual objects provide haptic feedback that emulate real-world objects, such as bigger objects requiring more force to move.
- Wearable. Wearable haptic devices, such as wristbands or watches, typically communicate with users through vibrations, sounds or temperature. For example, when an Apple Watch receives a notification from an app, it then sends a signal using vibration so the user knows to check their watch.
In addition to these basic categories, touchscreens and other electronic devices provide users with various forms of haptic feedback:
- Vibrotactile. Vibrotactile feedback is the most common feedback in haptic technology. Graspable, wearable and touchable devices often use vibration to send users signals. Tiny devices, such as linear resonant actuators, act as motors that produce vibration patterns to send these signals. These are used in smartphones and similar feedback devices.
- Force. While other types of haptic feedback target skin receptors so users feel different sensations, force feedback emulates the kinetic energy of real-world forces to stimulate muscles and ligaments beneath the skin. For example, a steering wheel used in video games will provide resistance when the user's car presses against another vehicle or object, requiring more intense muscle activity.
- Thermal. Thermal feedback simulates feelings of heat or cold and might be found in advanced VR technology.
- Kinesthetic. Kinesthetic feedback provides users with realistic perceptions of size, density or motion of objects. Kinesthetic feedback is used in sports-based VR games to emulate the feeling of a ball.
- Electromagnetic. This involves tiny electric actuators -- much like those found in internet of things devices -- that create tiny electromagnetic fields to produce tactile sensations. For example, medical trainees doing simulations of real-world operations work with electromagnetic technology that sends out vibrations to guide them properly or advise them against certain actions.
- Ultrasonic. Ultrasonic feedback sends ultrasound waves that users can feel to emulate the sensation of real objects. Hand-tracking devices let people use their hands to control a virtual environment. They don't require that users have physical contact with an interface. Instead, machine vision tracks the motion of a user's hands and fingers and uses algorithms to track the motion and orientation of the user's hands.
Why are haptics important?
Training simulation is an important use of haptics in various industries. It's also widely used in game development and to operate remote equipment. New VR and AR applications wouldn't be nearly as effective without haptic tactile feedback.
Industries use cases where haptics plays an important role include the following:
- Gaming. Gaming controllers and VR applications are already using haptics. As platforms such as the Metaverse develop, haptic experiences will continue to evolve. The Metaverse is a virtual world intended to make interactions with other users and objects as realistic as possible; haptics will be instrumental in this effort.
- Healthcare. Healthcare professionals learning to conduct surgical operations use haptic devices that interact with and guide them through simulations.
- Manufacturing. Manufacturers and warehouses use haptic devices to help with various aspects of training, such as teaching employees to work on assembly lines.
- Space. Space rovers are equipped with haptic feedback technology so remote operators can experience the motions of robotic arms through tactile sensations.
- Aviation. Haptic feedback gloves and other devices can produce tactile sensations to guide pilot trainees through simulations.
History of haptics
The applications of haptic communication technology increased dramatically in the latter half of the 20th century. Yet examples of haptics actuators and sensors using electricity to produce physical motion can be traced even further back. For example, the piezoelectric effect was discovered in the late 19th century, yet the sensors and actuators -- which use electrical charges to produce high-frequency vibrations -- were invented and applied in industry settings well into the 1900s.
The earliest uses of haptics were in aviation and early video game technologies. A plane's cockpit control system could be equipped with vibrotactile feedback so pilots could sense turbulence. When arcades were the dominant form of gaming in the late 1970s and early 1980s, machines relied on vibrotactile feedback so players could experience rumbling sensations.
Throughout the '90s, vibrotactile feedback was incorporated into portable game consoles, such as Sony's PlayStation, which relied heavily on this type of haptic technology. This exemplified the evolution of haptics over time into smaller and more portable devices, both inside and outside the world of gaming. This trend continued in the 2000s, when companies such as Immersion Corp. developed wearable haptic devices that users could wear around their hands for immersive VR experiences.
More recently, the COVID-19 pandemic expedited the use of no-touch technology in industry settings so people could interact with machines without physical touch feedback. This includes haptics and remote sensing technology, such as LiDAR. In the post-COVID world, it remains to be seen if companies will continue to invest in these technologies.
Key takeaways: Pros and cons of haptics
Haptic technology isn't just an added technological feature for entertainment applications. It has practical applications in various industries and will become more commonplace as the Metaverse and associated platforms take shape.
Haptic technology has many benefits. It lets users learn through immersive simulations so they can operate machinery better. It also improves users' experiences with devices such as mobile phones and smart watches. The global haptic technology market will see growth as haptics permeates various industries in new and creative ways.
There are high costs associated with advanced haptic technology. For example, devices with ultrasonic feedback are generally expensive to implement. Aside from costs, haptic platforms that operate on desktop interfaces have limited space to work with, which would limit the range of physical movements users can perform. Technical difficulties also must be considered. For instance, actuator issues and connectivity problems that can inhibit a haptic system's ability to provide accurate or consistent feedback.
Immersive learning strategies that incorporate VR and AR tech with haptic capabilities yield both quantitative and qualitative benefits for organizations. Explore six benefits of immersive learning with VR and AR.