perpetual software license
What is a perpetual software license?
A perpetual software license is a type of software license that authorizes an individual to use a program indefinitely. Generally, outside of termination, a perpetual software license lets the holder use a specific version of a software program continually with the payment of a single fee.
Use of traditional perpetual software licensing is declining as subscription-based pricing models become more popular. Customer's increased interest in subscriptions might be partly because perpetual licensing has a high initial cost.
Software vendors also have issues with the perpetual licensing model. It can be hard to ensure profitability with perpetual licensing because of the uncertain term of licensing and unforeseeable future development cost that can be involved with updates and upgrades.
How does a perpetual license work?
With perpetual licensing, a customer purchasing software pays an upfront charge for the software license. They also get supplemental support for a limited period, during which additional benefits are included. After the support period ends, the customer has the option of using the current version of the software without additional support, paying a lower-cost fee to for support and upgrades or buying a new license for an new version of the software.
Along with the perpetual license, the vendor typically provides technical support for a period of one to three years. During this initial period, the vendor usually provides software updates. However, updates might or might not be provided for free in perpetuity.
The perpetual software license model is comparable to other traditional retail purchases. For example, when a customer buys a refrigerator, they own it indefinitely after a one-time payment. That purchase usually comes with a warranty and service for a limited time.
Benefits and challenges of perpetual software licenses
There are several benefits to perpetual software licenses. Some user benefits include the following:
- Ownership. The customer owns the software for the term of the perpetual license agreement. There's no reliance on a cloud provider to host the software because perpetual licenses are often used with on-premises software.
- Upfront costs. Customers need only to pay a one-time fee to own the software. The license doesn't require repeated payments and there's less potential for hidden costs.
- Updates and support. Software support often only lasts for a limited period with perpetual licenses; however, in some cases, support is provided perpetually.
There are also benefits for vendors:
- Less continuous maintenance. In most cases, vendors don't commit to continuous updates with a perpetual license. Updates, new features and functionality, and software maintenance might be provided for a defined period, however.
- More revenue upfront. Perpetual licenses offer vendors guaranteed revenue up front, generally more than subscription licenses do.
Despite the benefits of perpetual licenses, there are several challenges. For customers, those include the following:
- Higher cost. Perpetual licenses have a higher upfront cost than subscription-based software licenses.
- Limited availability. Perpetual licensing might not be available for certain types of software.
- Maintenance. Perpetual licensing can be harder to update and maintain than subscription-based apps, especially when the customer fails to renew their support contract.
Downsides for vendors include the following:
- Less consistent revenue. The subscription license model offers a greater potential for consistent revenue than perpetual licenses.
- Less opportunity for change. It's easier to roll out updates and changes to the software product and pricing scheme in a subscription model. The perpetual model is less flexible.
Software subscription vs. perpetual license model
The perpetual license model and subscription licenses differ significantly.
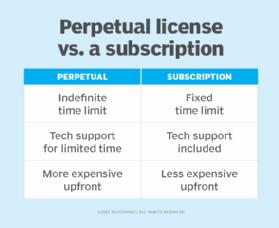
Perpetual software licenses are sold for a one-time payment and remain in effect for an indefinite time. The relationship between the customer and the software provider stops after the initial sale of the software unless the license includes maintenance and support for a specified time or the customer signs a maintenance contract.
Subscription software licenses are paid on an ongoing basis and remain in effect for a set time. Subscription software may be paid for on a weekly, monthly or annual basis. Subscription licensing is a more flexible pricing model; vendors can provide options for how frequently customers pay and how much they pay per period.
It's also more common for vendors to handle more maintenance tasks with subscription software. Subscriptions establish a consistent source of cash flow for the vendor.
Software as a service (SaaS) is usually paid on subscription basis. However, a third pricing model -- the perpetual subscription -- incorporates the perpetual license subscription approach. With a perpetual subscription, a SaaS product is paid at regular intervals indefinitely. The subscription is usually set to auto-renew.
The perpetual subscription is one of several SaaS subscription license types. Learn the basics of SaaS licensing and how the different types of licenses work.
