What is the digital divide?
The digital divide is the gap between demographics and regions that have access to modern information and communications technology (ICT) and those with no or restricted access. This technology can include the telephone, television, PCs and internet connectivity.
Broadly speaking, the digital divide refers to the gap between people who can access digital technologies, including the internet, versus those who cannot. This may be due to a lack of access to these technologies, although the problem is not just access-related.
Multiple factors are responsible for the current digital divide and its expansion. These include the availability of technology and its affordability to the general population. The relevance of technologies to local communities -- say, due to a lack of localized content or poor understanding of or interest in those technologies -- can also exacerbate the digital divide. Similarly, the available quality of service and level of digital literacy among potential ICT users also contribute to the digital divide.
As a global phenomenon, the digital divide affects people in every country and in both urban and rural geographies. However, it is particularly visible in rural areas, among low-income individuals and users, and in less developed countries.
Why is the digital divide an important global issue?
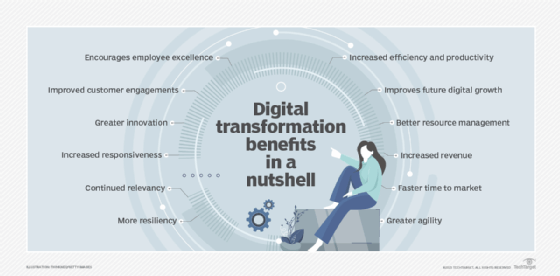
ICT is a crucial aspect of modern-day life. It fuels what is now known as the digital economy. Everyone uses technology for many different reasons, whether it's individuals, businesses, governments, militaries or nonprofits. Technology is a crucial driver of business efficiency and competitiveness. It helps governments deliver public services, empowers militaries to protect borders and citizens, and can boost individuals' quality of life.
Technology-powered devices and software support new and creative innovations in various industries and sectors, including manufacturing, retail, healthcare, education and finance. Technology enhances communication and collaboration, facilitates sustainable development, and fosters social inclusivity and equity. It keeps people connected and can keep businesses operational in the event of a crisis. When governments face crises and their aftermath, technology facilitates a faster return to normal life.
Those who can access and use ICT enjoy all the benefits of ICT, while those removed from it miss out on many economic and educational opportunities and encounter multiple barriers to connectivity and mobility in their personal, professional and social lives.
The digital divide prevents people in some geographies or communities from accessing healthcare information, resources and innovations, such as telemedicine and virtual consultations with medical professionals. They may also be unable to access potentially life-saving healthcare and medical developments, such as new vaccinations, antibiotics, genetic testing and telesurgery.
A widening digital divide also impacts education and educational outcomes, as well as business performance and results. Students with little or no access to the internet are unable to access online educational resources; some lose out on education entirely. Similarly, some businesses may struggle to tap into new markets, fail to convert new opportunities for expansion and growth, or fall behind competitors, simply because they lack the technology needed to achieve their goals.
All these issues deepen existing societal divides, including those between rich and poor, men and women, and various communities and subcommunities. A growing digital divide widens the chasm between developed and developing -- and underdeveloped -- economies, making it harder for the latter group to solve socioeconomic problems and improve the standard of living for their people.
What are the origins of the digital divide?
Long before the late 20th century, the digital divide referred mostly to those with and without telephone access. After the late 1990s, the term differentiated those with and without internet access, particularly broadband. The digital divide has evolved to refer to those in urban versus rural areas; between the educated and uneducated; between socioeconomic groups; and, globally, between the more and less industrially developing countries.
Even among populations with some access to technology, the digital divide can be evident in the form of lower-performance computers; lower-speed wireless connections; lower-priced internet connections, such as dial-up; and limited access to subscription-based content.
What is the digital divide today?
Today, the digital divide stems from multiple factors, such as the following:
- ICT accessibility, resulting from a lack of access to digital technology and internet service.
- Availability and affordability of modern, high-quality technologies, like smartphones and Wi-Fi access.
- The presence of a national technological framework for penetration, interconnectivity, quality of service and content localization.
The digital divide remains significant worldwide. A study by the United Nations Educational, Scientific, and Cultural Organization (UNESCO), International Telecomunnication Union (ITU) and Broadband Commission for Sustainable Development stated that the global offline population is 2.6 billion people. With that many people unable to access or use internet devices and applications, it's clear that meaningful, universal connectivity is not yet a lived reality for everyone in the world. The same report cited significant inequality across the globe in internet bandwidth growth and broadband penetration. Internet usage is another area of disparity. The study showed that 93% of people in high-income countries use the internet, making it nearly ubiquitous there, while internet usage is a paltry 27% in low-income countries and only 35% in the world's least developed countries. Experts anticipate the digital divide will be bridged in the coming years with growing demand from consumers, citizens, entrepreneurs and businesses for digital services, digital payments, connectivity services and digital transformation. But the world is not there yet. Only 155 countries in 2022 had a national strategic broadband plan.
In the U.S., the digital divide is starkly evident between high-income Americans and those with lower household incomes, i.e., under $30,000 per year. Among the latter group, according to a 2021 Pew Research Center report, 24% of adults don't own a smartphone, 43% don't have home broadband services and 41% lack a computer. In contrast, these technologies are commonly used by almost all American adults earning $100,000 or more and fairly common among those earning $30,000 to $99,000.
The deep-rooted, multifaceted nature of the digital divide is why some experts say that it is not a binary phenomenon, meaning it is not just a problem between the ICT haves and have-nots. Experts believe that the solution to bridging the divide is not simply to provide universal and affordable access to ICT, especially the internet. Effort must also go to getting more people interested in using ICT once they gain access.
The need to bridge the digital divide
Bridging the digital divide improves digital literacy, promote digital skills democracy, enhance social mobility and promote economic equality and growth. It is also critical to ensure universal connectivity to the internet. Many experts and organizations believe that is vital for the following:
- Achieving sustainable global development.
- Removing barriers to digital and social inclusion.
- Accelerating economic development and welfare.
- Sparking progress toward the U.N.'s Sustainable Development Goals (SDGs).
Some organizations like UNESCO say that digital technology could be the most essential tool for ensuring human-centered emancipation, again underscoring the need to bridge the digital divide. Many organizations are pursing that goal. The U.N., for example, helps to raise awareness through a celebration of World Telecommunication and Information Society Day on May 17 every year. Similarly, ITU and the Broadband Commission publish The State of Broadband report every year to spread awareness about global online activity, current gaps and how these gaps impact the global achievement of the UN SDGs.
In the U.S., nonprofits are also involved; some work to provide internet access and laptops to school districts and low-income users, enabling them to access educational services, like video on demand, video conferencing and virtual classrooms.
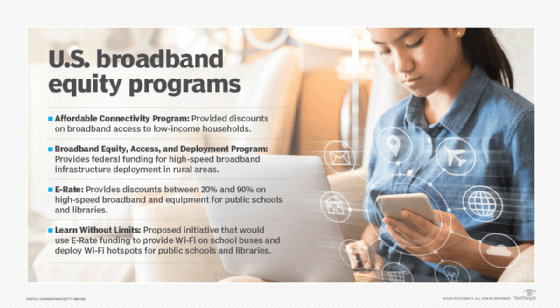
Without these interventions, users on the disadvantaged side of the digital divide may not be able to use these services, which require access to both digital devices and high-speed internet connections.
See how the digital divide affects patient portal use in primary care, and learn about creating a community-led telehealth approach for supportive cancer care to bridge the digital divide in rural areas.