What is the metaverse? An explanation and in-depth guide
The metaverse reached the peak of hype and has been left for dead, but make no mistake, the technologies that will power this 3D internet are firing on all cylinders.
The metaverse refers to the convergence of physical and virtual space accessed through computers and enabled by immersive technologies such as virtual reality, augmented reality and mixed reality. Described by proponents as the next iteration of the internet, this 3D virtual world is envisioned as a persistent, collective, shared space where digital facsimiles of ourselves, or avatars, move freely from one experience to another, taking our identities and monetary assets with us.
Visions of a parallel digital universe where humans can experience life in ways both akin to and not possible in the real world aren't new -- they predate the internet. But the concept of a blended physical and digital reality became more tangible in recent decades as technological advances -- from the near-universal adoption of mobile phones and rollout of high-speed internet to popular games such as Pokémon Go -- made the metaverse seem less far-fetched.
Hefty industry investment in metaverse-enabling technologies, the growth of online video games, breakthroughs in AI and the acceleration of remote work and socializing driven by the COVID-19 pandemic spurred more tech innovation and increased user adoption of online life.
In November 2021, Facebook renamed itself Meta and announced a $10 billion investment in developing virtual experiences, prompting enthusiasts to anoint the metaverse as the world's new computing interface. Bill Gates jumped on the bandwagon, predicting that meetings would move from screens to the metaverse in two or three years. The hype was premature, though.
What happened to the metaverse? Is it dead?
In late 2022, about the time ChatGPT captured the world's attention, the metaverse bubble popped. Financial losses ensued, notably Meta's $13.7 billion operational loss in its Reality Labs division for 2022 as a whole. Microsoft laid off employees from its Mixed Reality Toolkit and HoloLens teams, cryptocurrency collapsed and consumers, eager to return to their pre-COVID lives, were not clamoring for extended reality devices.
The losses at Meta's Reality Labs unit increased to $16.1 billion in 2023, and Disney cut its metaverse division. Media reports proclaimed the metaverse was dead. The backlash to metaverse overmarketing included industry repudiation of the term itself. In its 2024 debut of the Apple Vision Pro headset, Apple, for example, took pains to disassociate the device from the metaverse, calling it instead an entrée to spatial computing.
Why metaverse technology is still important for businesses
Although the vision of a rapid gestation of fully-realized virtual worlds where humans work, shop and socialize from the comfort of their couches has dimmed, the metaverse isn't dead. Components of it are gaining traction as graphics and capabilities for virtual and augmented reality, bolstered by AI, rapidly improve. The development of new technology such as eye tracking, which uses sensors to monitor and record eye movements, promises to make visual experiences more engaging.
In the area known as the industrial metaverse, epitomized by the Nvidia Omniverse platform, companies are building digital twins to design and monitor physical objects. Businesses are also using virtual reality (VR) to train employees and applying augmented reality (AR) to overlay information on real-world objects, helping their employees work better.
In e-commerce, customers are clamoring for virtual products that "tie back to the physical world," according to a June 2023 McKinsey report, which stated that the market for metaverse commerce alone -- "from home and food to fitness and apparel" -- could drive "$5 trillion in value creation by 2030." A report from data-gathering company Statista pegs the metaverse market at $74.4 billion in 2024 and predicts that by 2030, at an annual growth of rate of 38%, it will reach $507.8 billion with over 2.6 billion users.
A metaverse guide for the enterprise
What are companies to make of a technology phenomenon that's hot one day, cold the next and in the throes of rebranding itself? TechTarget's guide to the metaverse breaks down where this rapidly evolving set of technologies stands today and where it's headed.
Topics covered include the various technologies and platforms that support the metaverse, ongoing challenges, real-world use cases and the metaverse's impact on the future of work. Readers can follow the hyperlinks to other TechTarget articles for deeper dives into these and other topics, as well as to our in-depth definitions of key metaverse terms and novel techniques such as digital threads and Gaussian splatting.
A short history of the metaverse
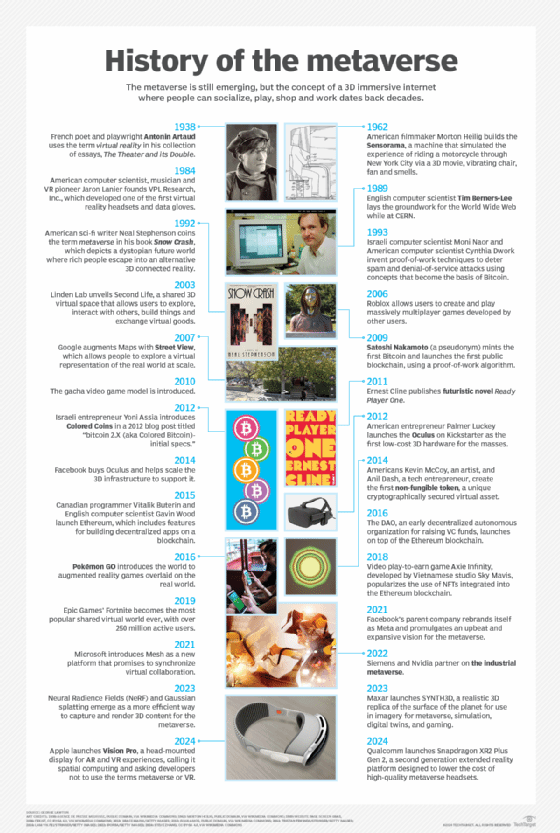
The concept of the metaverse dates back to the previous century, when the name was introduced into the lexicon -- albeit in a fictional setting.
Author Neal Stephenson coined the word metaverse in his 1992 dystopian sci-fi novel Snow Crash to describe a virtualized environment where people gained status based in part on the technical skill of their avatars. In addition to popularizing the concept of digital avatars, the novel's depiction of a networked 3D world is said to have influenced real-life web programs, including Google Earth and NASA World Wind.
Another novel that popularized the metaverse was Ernest Cline's Ready Player One, published in 2011 and later made into a movie by Steven Spielberg. It depicted a future where people escape real-world problems by entering The Oasis, a virtual world accessed using a VR headset and haptic gloves that provide tactile sensations. Such haptic feedback also became a key metaverse building block.
Fiction aside, the foundational technologies supporting an actual metaverse date back to the 1960s. The metaverse's legacy includes two other hype waves that are all but forgotten -- the first one in the early 2000s when use of the pioneering Second Life virtual community plateaued after initial growth, and the second in 2010 when the first VR headsets proved not to be the gateway to the metaverse that inventors anticipated. Both busts led to significant technological advances, though.
Here is a sampling of the inventors whose pioneering work proved integral to the current concept of the metaverse. A graphic showing a comprehensive timeline of metaverse technology milestones follows.
Dawn of virtual reality
American cinematographer and inventor Morton Heilig built the Sensorama in 1962. The mechanical device simulated the experience of riding a motorcycle through New York City by using a 3D movie, vibrating chair, a fan and piped-in smells, providing one of the earliest immersive multimedia experiences.
American computer scientist and Turing Award winner Ivan Sutherland created his revolutionary computer program, Sketchpad, in 1963 as a student at MIT, laying the foundation for modern computer graphics and human-computer interaction.
Jaron Lanier, another American computer scientist, began his pioneering work in virtual reality in the mid-1980s, developing some of the earliest commercial VR headsets and data gloves.
World Wide Web
British computer scientist Tim Berners-Lee developed the first open source web server, browser and editor in the late 1980s and early 1990s, inventing the World Wide Web, a linked network of webpages, graphics and other media making information accessible and navigable.
Massively multiplayer online role-playing games
A host of developers and designers, including Richard Garriott, Raph Koster and Mark Jacobs, introduced MMORPGs in the late 1990s and early 2000s, demonstrating the commercial viability of large-scale virtual games.
Second Life
In 2003, computer programmer and entrepreneur Philip Rosedale and his team at Linden Labs launched Second Life, an online platform for creating immersive, persistent, user-created virtual worlds.
VR resurgence
Advances in virtual reality technology in the 2010s led by the likes of Palmer Luckey of Oculus VR -- now part of Meta's Reality Labs -- and developers at Sony, Google, Unity, Epic Games and other independent studios popularized VR use.
Bitcoin, blockchain and NFTs
The pseudonymous Satoshi Nakamoto created Bitcoin, the first decentralized cryptocurrency, and launched the first public blockchain using a proof-of-work algorithm in 2009.
In 2015, Russian-Canadian programmer Vitalik Buterin and Gavin Wood, a British computer scientist, launched Ethereum, a blockchain platform that introduced smart contracts. These contracts enabled the creation of decentralized applications and digital tokens, including non-fungible tokens. The Ethereum platform can support autonomous systems in the metaverse, such as virtual economies and governance mechanisms.
Other metaverse notables
In random order, a partial list of other modern-day metaverse enablers includes the following:
- Mark Zuckerberg of Meta.
- Tim Sweeney of Epic Games.
- Jens Bergensten of Minecraft fame.
- Sam Mathews of Fnatic.
- Tim Cook of Apple.
- Jensen Huang of Nvidia.
- Peggy Johnson of Magic Leap.
- Sam Altman of OpenAI.
How does the metaverse work?
In his best-selling primer, The Metaverse: And How It Will Revolutionize Everything, author Matthew Ball defined the metaverse as the following:
"A massively scaled and interoperable network of real-time rendered 3D virtual worlds that can be experienced synchronously and persistently by an effectively unlimited number of users with an individual sense of presence and with continuity of data, such as identity, history, entitlements, objects, communications and payments."
This version of the metaverse is largely unbuilt, and at present there are competing versions of what the metaverse could be like and which technologies will power it. Will it be open and have a deep level of interoperability across platforms? Or will it instead function as a multiverse, containing many independent worlds that share little, if any, data?
In a talk at the 2022 MIT Platform Strategy Summit, Lauren Lubetsky, senior manager at Bain & Company, outlined three possible scenarios for the metaverse that still hold true:
- The metaverse remains a domain of niche applications, used by consumers for entertainment and gaming but stopping well short of an all-encompassing virtual reality.
- The metaverse is controlled by large competing ecosystems -- for example, Apple and Android meta worlds -- with limited interoperability.
- The metaverse is a dynamic, open and interoperable space, much like the internet but in 3D.
Because the metaverse doesn't yet exist as a single entity, it can't be stated with precision how it will work. But broadly speaking, the metaverse is a digital ecosystem built on various kinds of virtual 3D technology, real-time collaboration software and blockchain-based decentralized finance tools.
The degree of interoperability among virtual worlds, data portability, governance and user interfaces will depend on what the metaverse eventually becomes.
When is a full-fledged metaverse coming?
Today, companies use the term metaverse to refer to many different types of enhanced online environments. These range from online video games like Fortnite to virtual workplaces like Microsoft Mesh or Meta's Horizon Workrooms to virtual dressing rooms and virtual operating rooms. Rather than a single shared virtual space, the current version of the metaverse is indeed shaping up as a multitude of metaverses with limited interoperability as companies jockey for position.
The combination of uncritical enthusiasm for the metaverse and uncertainty about how it will pan out has some industry watchers questioning if the metaverse will ultimately be much different from the digital experiences we have today -- or, if it is, whether the masses will be willing to spend hours a day in a headset navigating digital space.
Others, however, like engineer and entrepreneur Louis Rosenberg, who helped develop one of the first mixed reality systems at Stanford and the U.S. Air Force in the early 1990s, argue that our "immersive future" is inevitable.
"We will just think about one life. One reality, and it will be a combined world of the real and the virtual," said Rosenberg, CEO and chief scientist at Unanimous AI. "That is the metaverse."
How is the metaverse accessed?
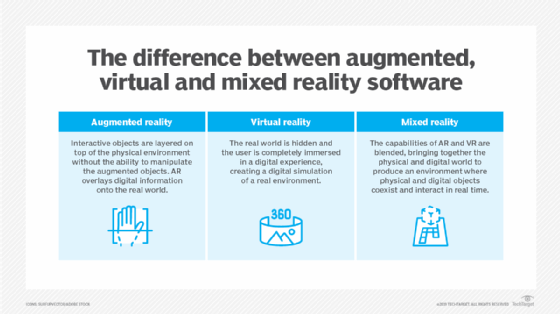
Virtual reality and augmented reality are two technologies considered particularly important to the development and growth of the metaverse. Here's why:
- VR is a simulated 3D environment that enables users to interact with a virtual surrounding in a way that approximates reality as perceived through our senses. This approximation of reality is now typically accessed through a VR headset that takes over a user's field of vision. Haptics, including gloves, vests and even full-body tracking suits, enable more lifelike interaction with the virtual environment.
- AR is less immersive than VR. It adds digital overlays on top of the real world using digital rendering tools. Users can still interact with their real-world environment. The game Pokémon Go is an early example of AR. Google Glass and head-up displays in car windshields are well-known consumer AR products.
Whether VR and AR experiences turn out to be the primary interfaces of the metaverse remains to be seen. At present, many of the metaverse-like experiences offered mostly by gaming platforms such as Roblox, Decentraland and Minecraft can be accessed through browsers or mobile devices and a fast internet connection.
What is the difference between the internet and the metaverse?
The internet is a network of billions of computers, millions of servers and other electronic devices. Once online, internet users can communicate with each other, view and interact with websites, and buy and sell goods and services.
The metaverse doesn't compete with the internet -- it builds on it. While the internet is used primarily for browsing, the metaverse offers a more immersive experience where people can "live" to a degree in virtual spaces. The growth of the internet has spawned many services that are shaping the metaverse.
"In gaming, you see Roblox, Minecraft and other immersive video games -- and even Zoom -- foreshadow what the metaverse is designed to offer," said Ben Bajarin, CEO and principal analyst at Creative Strategies.
A closer look: How VR and the metaverse relate to each other
VR is often associated with the metaverse, but the terms aren't synonymous. Particular VR technologies, as noted, provide the means for interacting with the more expansive multiverse platforms.
Within that access role, VR can support a variety of metaverse use cases. For example, VR can combine with the allied field of digital twin technology, which lets organizations create virtual representations of physical devices, machines or processes. Technologists can use the VR extension of a digital twin to simulate various issues, according to Johna Till Johnson, CEO and founder of Nemertes Research.
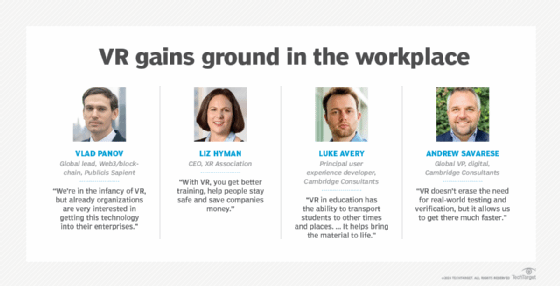
VR contributes to the industrial metaverse
VR and digital twinning provide some of the basic building blocks for the emerging industrial metaverse. The industrial metaverse will link digital twins into a wider virtual environment that encompasses machines, factories, products and supply chains.
Industrial design is another promising application for VR. Organizations can employ VR to consider the effects of different product design decisions. They can also build simulated prototypes to avoid the cost of creating physical ones.
Organizations are also deploying VR for employee safety training, particularly in settings where employee mistakes can cause harm. Assembly line workers can train in a virtual environment before hitting the factory floor, or emergency responders can use VR disaster training to practice in a safe environment. Indeed, risk reduction is one of the key workplace benefits of such VR applications, according to Ria O'Donnell, author of Transformative Digital Technology for Effective Workplace Learning.
VR sets stage for healthcare metaverse
In healthcare, VR could reform surgical training by letting surgeons practice a specific, on-demand procedure as many times as they wish, leading to a shorter learning curve. Medical researchers are also exploring the use of virtual reality in healthcare in fields such as pain management and pediatrics. Such applications represent the first vestiges of what might become a healthcare metaverse, in which VR could operate alongside other technologies such as blockchain and digital twins.
VR bolsters corporate training
Other corporate VR use cases include training for high-complexity scenarios, such as astronaut preparation, institutional knowledge transfer to record workers' knowledge before they retire, empathy lessons for customer service employees and soft skills training.
As for the latter, VR can benefit soft skills training in a couple of ways. VR, for one, can result in faster class completion rates, according to PwC research. The consultancy's study found its participants completed VR-based soft skills training as much as four times faster than classroom sessions. The same study noted participants were up to 275% more confident in the soft skills they developed through VR training.
The greater assurance stems not only from VR's so-called immersive learning techniques, but also from the ability of learners to repeatedly practice skills in a comfortable setting. Indeed, training will likely emerge as a prominent metaverse deliverable, given the ability to virtualize scenarios too expensive or arduous to recreate in the physical world.
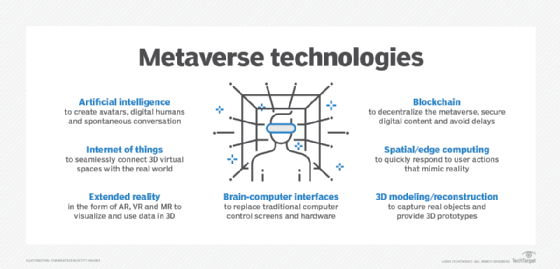
Other metaverse technologies
Several other technologies, in addition to VR and AR, play a role in shaping the metaverse. A definitive list, however, has yet to crystallize. Industry watchers shy away from codifying the technologies that will power the metaverse. This is in part because the metaverse is evolving and partly because many of the tools driving the metaverse are themselves made up of multiple technologies.
Gartner, for example, has described metaverse technologies in terms of "tech themes," which include spatial computing, digital humans, shared experiences, gaming and tokenized assets. Forrester Research characterizes metaverse tools as "enablers of 3D development environments." What's certain: Professionals skilled in 3D modeling and IoT for developing digital twins are among the talent companies will need to recruit for.
That being said, the following technologies are generally expected to have the biggest impact on metaverse development over the next decade:
- Artificial intelligence.
- IoT.
- Extended reality, including VR, AR and mixed reality.
- Brain-computer interfaces.
- 3D modeling and reconstruction.
- Spatial and edge computing.
- Blockchain.
How does the metaverse fit into Web 3.0?
The terms metaverse and Web 3.0 are often used interchangeably, but they represent distinct concepts. Web 3.0, or Web3, refers to a vision of the internet characterized by the following features:
- Decentralization.
- Blockchain integration.
- Interoperability.
- Digital ownership.
- Cross-platform compatibility.
Web 3.0 aims to decentralize the internet by moving away from centralized servers and platforms controlled by a few large companies, giving users greater control over their digital assets and interactions. Blockchain is a key technology, providing the infrastructure for decentralized applications and digital currencies. Interoperability enables different systems to exchange and use information, while cross-platform compatibility ensures that applications can run on different devices or platforms.
As a fully immersive, interconnected digital universe where users can seamlessly interact with each other and digital objects in real time, the metaverse is expected to occupy a key place in Web 3.0. It relies on many of the same tenets, including greater user control, and likely will deploy many of the same cutting-edge technologies, such as blockchain and AI.
Metaverse companies
As metaverse prospects have waxed and waned amid a fluctuating economy and the rise of generative AI, so have corporate strategies. Here is a sampling of companies, listed alphabetically and with an emphasis on enterprise services, that are commonly regarded by analyst firms such as Gartner and Forrester and other industry watchers as playing a major role in shaping the metaverse, whatever name it goes by or shape it takes.
Apple
Apple's vision of the metaverse currently revolves around its Apple Vision Pro headset. The virtual reality goggles -- or spatial computer, as Apple describes Vision Pro -- became available in February 2024, priced at $3,500 a pair and designed to bring the digital and real worlds closer together by enabling users to immerse themselves in both VR and AR experiences. Early reviews used words like mind-blowing, magic and messy to describe its capabilities.
AWS
The world's largest provider of cloud services and technologies plays a significant role in the development of the metaverse by virtue of its compute, storage, database, networking, AI and blockchain services. As noted by Moor Insights & Strategy principal analyst Anshe Sag, AWS supports many extended reality companies, including Meta, Magic Leap and Nvidia. Use cases in its spatial computing unit include immersive computing -- AR/VR -- for collaboration, commerce, training and the industrial metaverse; digital asset management; and real-world simulation.
Epic Games
Epic Games, makers of the Unreal Engine software for game developers and online game Fortnite, is partnering with The Walt Disney Company on its vision of the metaverse. In February 2024, Disney acquired a $1.5 billion equity stake in the video game developer to build a "persistent universe" for games and entertainment. Disney's investment came less than a year after it closed down its own metaverse division. Disney also announced it will bring Pandora -- The World of Avatar, Disney's 3D experience based on the movie Avatar at its Orlando property, to Disneyland in California.
Google's expertise in technologies such as AR/VR, spatial computing, cloud, AI and machine learning and content creation positions it to play a significant role in the metaverse. Its track record to date on metaverse-adjacent products, however, is underwhelming. The company announced in 2023 that it would no longer sell Google Glass Enterprise Edition, AR smart glasses launched in 2013 that failed to catch on. Several metaverse initiatives are in the works, including Project Starline, a 3D immersive video chat technology.
Meta
"From now on, we will be metaverse-first, not Facebook-first," CEO Mark Zuckerberg wrote in the October 2021 announcement of his company's branding change, singlehandedly making metaverse a household word and creating the impression that humans would soon be living life in an immersive, persistent three-dimensional virtual reality: Meta would "bring the metaverse to life."
The quest has proved hard, as Meta's Reality Labs division chalked up nearly $30 billion in losses during 2022 and 2023 and its metaverse platforms -- the multiplayer virtual game Horizon Worlds, and Horizon Workrooms, an immersive virtual office space -- got mixed reviews. While Zuckerberg has not abandoned Meta's quest for virtual reality, some industry watchers have noted that he now talks about the metaverse as a blend of physical and digital worlds and, in recent earnings conferences, has emphasized Meta's work on AI chatbots and assistants.
Microsoft
The company's involvement in the development of the metaverse spans various divisions and products. They include Microsoft's mixed reality HoloLens headset, Microsoft Mesh immersive workplace platform and Xbox Cloud Gaming apps, recently made available on Meta's VR headsets. Microsoft's Azure cloud and blockchain services, as well as its AI and ML capabilities, are used to enhance metaverse experiences. However, the emphasis on AI at the company's October 2023 Ignite conference and multiple layoffs at Microsoft's industrial metaverse operations led to speculation that it might be pulling back from immersive technologies.
Nvidia
Nvidia Omniverse, launched in 2022 and purpose-built for developing applications in the metaverse, has been heralded as shaping the future of 3D and the metaverse itself. By integrating 3D design, spatial computing and physics-based workflows, the real-time platform enables the creation of digital twins for factories, warehouses, products and other infrastructure. It also streamlines the creation of 3D-related media for entertainment and product demos and enterprise media content, which in turn can be rendered on computers, smartphones and extended reality devices.
Gartner lays out 4 strategic metaverse planning assumptions
By 2024: At least 70% of large cities will use digital twins to assess the environmental readiness of infrastructure investments.
By 2027: A majority of B2C enterprise CMOs will have a dedicated budget for digital humans in metaverse experiences.
By 2028: 30% of B2B virtual reality pureplay providers that do not participate in a cloud marketplace will exit the business or be acquired.
By 2030: 20% of metaverse users in developed markets will have experienced at least a basic metasuit when interacting with one or more metaverses for work or social purposes.
Source: "Emerging Tech: Product and Business Innovators in the Metaverse," Tuong Nguyen et al, June 2023.
How will the metaverse affect the future: utopian or dystopian?
Skeptics of the metaverse view it as merely an extension of the digital experiences we have today but not transformative -- and potentially something worse: a magnifier of current social media ills, including disinformation campaigns, addictive behavior and tendencies toward violence.
In contrast, most business leaders remain optimistic about the metaverse's future despite the hype slowdown, according to a Protiviti-Oxford University survey conducted from January to March 2023. Two-thirds of the 250 executives polled believe Web3 and the metaverse will significantly impact the economy and their business success over the next decade. Advertising and marketing are key entry points for metaverse use: 79% of the respondents said they planned to use it for customer engagement.
North American executives were markedly more enthusiastic about the metaverse than their European and Asia-Pacific counterparts, with a whopping 85% stating its importance for future success, compared to 57% in Asia-Pacific and 46% in Europe. Moreover, nearly two-thirds (65%) of North American executives polled said they already had a metaverse strategy, in contrast to 32% in Europe and 27% in Asia-Pacific.
How should businesses prepare for the metaverse?
Creating successful metaverse work environments will require far more than grafting existing office spaces and protocols onto virtual spaces. Indeed, early research suggests that simply translating existing offices into a 3D virtual equivalent can reduce productivity and even cause nausea and motion sickness. VR motion sickness can happen when an end user's brain receives conflicting signals about self-movement in a digital environment. Businesses eager to apply virtual reality to their marketing and products should be hiring and training people who "can think in 3D," said Andrew Cornwall, a senior analyst at Forrester.
Businesses should also prepare to deal with user experience issues such as the so-called screen door effect, which hinders the use of VR headsets by causing a mesh appearance that resembles looking through a screen door. Selecting a headset with higher resolution and dpi display can minimize this effect.
Still, like the internet in the 1990s, the metaverse represents an opportunity to "shrink the world," said Andrew Hawken, co-founder of Mesmerise, a VR technology vendor. Done right, metaverse technologies in the workplace could increase teleworker camaraderie, improve collaboration, speed up training, reduce the need for office space and make work a happier place in general. However, the metaverse will also eliminate jobs, requiring companies to reskill workers, said Frank Diana, managing partner and principal futurist at Tata Consultancy Services.
Metaverse challenges
No matter what form the metaverse takes, cybersecurity challenges and privacy challenges loom as major concerns. The current lack of privacy regulations for the metaverse presents many risks for businesses and users, including the following:
- Misapplication of current privacy regulations, such as GDPR.
- Intrusive and extensive data collection.
- Issues concerning data rights and ownership.
- Exploitation of minors.
- User-to-user privacy.
One of the most serious ethical issues related to the use of VR and other extended reality technologies centers on the exposure of individual mental models. The concern is that XR software can tap into the subconscious thought processes of a person by monitoring eye movements and other involuntary reactions, revealing inner thoughts that can influence decisions. This insight enables the software to make highly accurate predictions about human decision-making, raising concerns about potential misuse by companies. Ethicists point out that mental models could also be used as public training data.
Businesses will need to be proactive in creating a viable data privacy policy tailored to their organization and to work with the major metaverse platform owners and standards organizations to establish security and privacy safeguards. In addition, consumers will need to make an effort to understand the security and data privacy policies of both the businesses they frequent and the metaverse platforms on which those businesses reside.
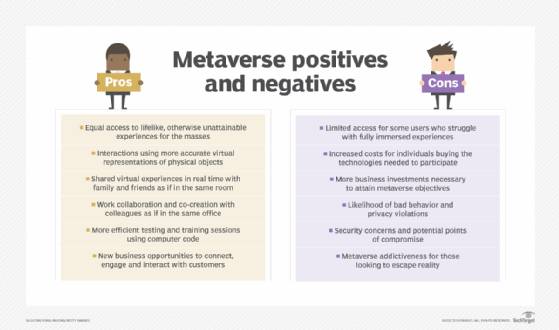
What will the metaverse mean for the average user? TechTarget interviewed analysts, consultants, business executives and researchers on metaverse pros and cons. On the positive side, an immersive metaverse enables humans to go where they were never able to go before, including outer space. Online social connections can also become much richer. On the other hand, the bad behavior witnessed on social platforms has the potential to be magnified in a virtual world, and metaverse usage could be addictive to some people.
Linda Tucci is an executive industry editor at TechTarget Editorial. A technology writer for 20 years, she focuses on the CIO role, business transformation and AI technologies.
John Moore is a writer for TechTarget Editorial covering the CIO role, economic trends and the IT services industry.
Technology writer David Needle contributed to this article.






