
Getty Images/iStockphoto
NFT wash trading explained
NFT popularity grew with the rise of cryptocurrency. But scams -- such as wash trading -- also increased, presenting new problems for businesses and consumers.
NFT popularity soared in 2021, but with its popularity came new types of scams -- such as NFT wash trading.
Nonfungible tokens (NFTs) are blockchain-based assets that are one-of-a-kind and cannot be interchanged. NFTs prove ownership on a digital ledger system and are bought and sold online in specialized marketplaces. Like the high-end art world, NFTs are subjective, and value is based on demand.
NFT popularity skyrocketed with Chainalysis' NFT Market Report, stating $44.2 billion of cryptocurrency was sent between two Ethereum smart contracts in the NFT marketplace in 2021, which increased by more than $106 million from 2020.
Wash trading is just another scam to mislead the market and for thieves to steal money.
NFTs explained
NFTs are unique, cryptographic assets and are different from cryptocurrency and digital currency. They represent real-world collectible items such as trading cards, artwork, videos, music, real estate and photos.
NFTs have certificates of authenticity, which means they can't be replaced. Each NFT is on a decentralized platform using blockchain technology. NFTs can also be used to represent an individual or business's property rights, identities and domain name ownership. Because of the blockchain, NFTs cannot be copied or destroyed, so they can be used for several business applications -- including supply chain, proof of ownership of product or service, and collectibles for loyalty.
What is NFT wash trading?
NFT wash trading is a type of scam. Wash trading is a misleading act to drive up the price of NFTs by the buyer and seller. The buyer and seller can sell the piece back and forth to drive up the cost, but only publicly report the first sale. In the next exchange, the money and NFT are returned to the original seller at the same time. Most of the time, the buyer and seller are the same bad actor.
When the asset is sold, it goes to a new cryptocurrency wallet that the original owner also controls. NFTs are easy to link with the trading platform because users simply connect their wallets -- sometimes without needing to identify themselves.
The price of NFTs then increases because future buyers feel it is in demand with all the sales. Cryptocurrency is valued the same way -- by demand.
Blockchain analysis is one way to check the sale of NFTs to look for those that are self-financed for wash trading.
Learn more about avoiding NFT scams.
How does NFT wash trading work?
For example, an investor has $1 million vested in Ethereum. The investor mints or creates a new NFT on the blockchain, then sells this NFT to themself for $1 million by sending it to another cryptocurrency wallet they own.
The NFT is now worth $1 million from its past sale listed publicly on the blockchain, which is an online ledger of all transactions.
Even if the investor sells this NFT to another person at a large discount, the wash trader nets the entire amount of the sale since they bought and sold it to themself.
Examples of NFT wash trading
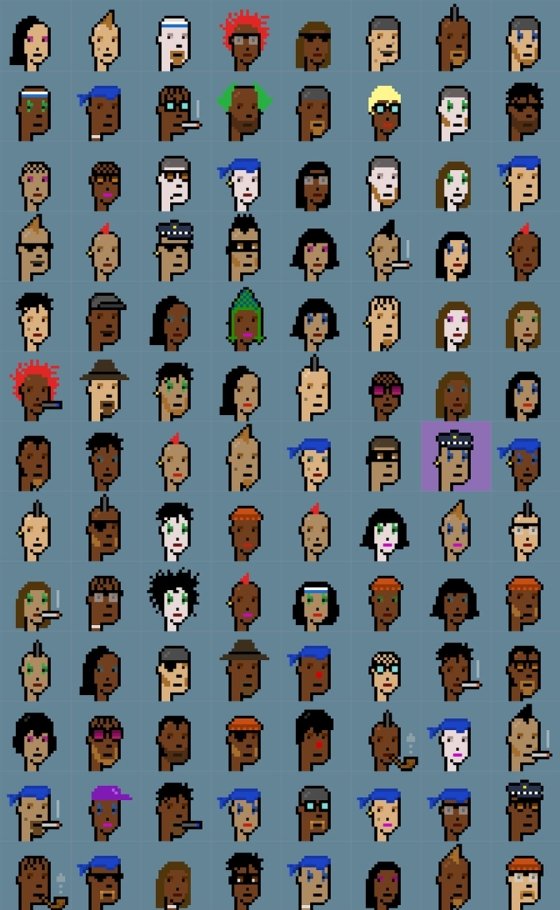
One real-life notable example of NFT wash trading was that of the CryptoPunk 9998. This NFT sold on Oct. 28, 2021, for 124,457 ETH -- worth around $532 million at the time of sale. The ether used for purchasing this NFT was transferred to the seller, and then it was transferred back to the buyer, paying off the loan. This type of loan is called a flash loan.
The seller then listed the NFT on the market for $250,000 Ether-- worth about $1.01 billion at the time. Prior to the wash trade and flash loan, the CryptoPunk 9998 NFT was worth $300,000 to $400,000.
Is wash trading illegal?
Technically, NFT wash trading is illegal and a form of NFT scam. The Commodity Futures Trading Commission charged a Coinbase employee with wash trading on their platform and providing misleading information.
However, the issue with NFT wash trading is that these assets have not been clearly defined by jurisdictions as either a financial security or a commodity, which makes it difficult to regulate. The sanctioning body must also prove intent to mislead and price gouge. Wash trading is highly unethical and is thought of in the same regard as insider trading.
Using NFTs for money laundering
Money laundering in the art world is nothing new. Art pieces are easy to move and have subjective prices. Criminals can purchase art with illegally gained money and sell the art later -- laundering the money and removing the connection to the original criminal activity. NFTs offer a different avenue for criminals to exploit.
Cybercriminals laundered about $8.6 billion in cryptocurrency in 2021, which is a 30% increase over 2020, according to a Chainalysis report. However, since blockchain technology clearly shows ownership, it can be easier to track down criminal activity.
Because of NFTs' subjective values, they can be used for self-laundering. Criminals use self-laundering to create an NFT and purchase it for themselves with tainted money. The ledger lists the sale to make it a valuable good. The criminal then sells the NFT to an unrelated party to receive money in return that appears legitimate.
With NFT money laundering, transfers are stored on the blockchain, so it is possible to track abuse. The activity needs to be monitored by marketplaces, law enforcement agencies and regulators.








