What is the Cybersecurity Information Sharing Act (CISA)?
The Cybersecurity Information Sharing Act (CISA) allows United States government agencies and nongovernment entities to share information with each other as they investigate cyberattacks. Sharing is voluntary for participating organizations outside the government.
As of 2024, CISA has been enacted to enhance the collaboration between the private sector and government to combat cyberthreats effectively. Currently, several U.S. regulatory frameworks impede sharing.
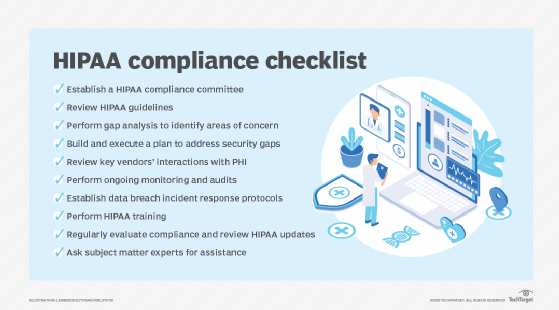
For example, should a hospital in the United States come under attack, hospital administrators could be prevented from sharing information with government agencies because of privacy restrictions in the Health Insurance Portability and Accountability Act (HIPAA).
Under the updated provisions of CISA, regulatory hurdles have been addressed to streamline information sharing while maintaining privacy protections.
Information sharing under CISA
Under CISA, the Director of National Intelligence and the federal departments of Homeland Security, Defense and Justice are required to work together and develop procedures for sharing cybersecurity threat information.
Nonfederal entities will be required to remove personal information before sharing cyber-threat indicators, and the Department of Homeland Security will be required to conduct a privacy review of received information.
CISA concerns and safeguards
Opponents of the legislation worry that the federal government will abuse how uses the information it gathers. As of this writing, the government may only use shared information to do the following:
- Identify a cybersecurity purpose.
- Identify the source of a cybersecurity threat or security vulnerability.
- Identify cybersecurity threats involving the use of an information system by a foreign adversary or terrorist.
- Prevent or mitigate an imminent threat of death, serious bodily harm or serious economic harm, including a terrorist act or the use of a weapon of mass destruction.
- Prevent or mitigate a serious threat to a minor, including sexual exploitation and threats to physical safety.
- Prevent, investigate, disrupt or prosecute an offense arising out of a threat such as serious violent felonies or relating to fraud and identity theft.
In response to privacy concerns, CISA mandates strict oversight and periodic audits to ensure compliance with privacy and civil liberties guidelines.
CISA impact and implementation
The implementation of CISA has led to significant advancements in the detection and prevention of cyberthreats. By fostering a collaborative environment, both government and private entities can benefit from shared intelligence, leading to a more resilient cybersecurity infrastructure.
Cybersecurity has many facets that require a keen and consistent eye for successful implementation. Improve your own cybersecurity implementation using these cybersecurity best practices and tips. Also, data privacy is one of the most challenging areas of IT security many businesses have to contend with. Find out more about the top six data privacy challenges.
