Decentralized finance vs. centralized finance: What's the difference?
When it comes to buying and selling cryptocurrency, exchanges follow a centralized or decentralized approach. Learn about the advantages and disadvantages of CeFi and DeFi methods.
Over the last century, the operations of money and financing have largely been centralized functions, overseen by banks, regulatory authorities and governments. The ability to provide funding and facilitate transactions are functions that, in the broader economy, are provided under the oversight of centralized authorities and regulatory entities.
With the emergence of cryptocurrency, practices and operations for finance are being reevaluated and disrupted with innovative and emerging approaches. Unlike fiat currency, cryptocurrency is typically not created by central governments, and the ongoing operations of cryptocurrency systems are not under government control.
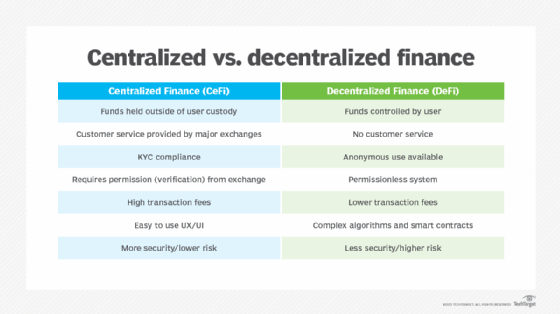
There are two prevailing approaches to managing the trading and transactions of cryptocurrency: centralized finance (CeFi) and decentralized finance (DeFi). CeFi has similarity to traditional forms of centralized finance, where banks and exchanges manage currency and transaction flows. DeFi enables peer-to-peer transactions without the need for a centralized exchange. CeFi and DeFi have some similarities, as well as advantages and disadvantages.
What is centralized finance?
CeFi is an approach within the cryptocurrency market to handle the purchase, sale and trading of cryptocurrency tokens through a central exchange.
CeFi is the cryptocurrency market equivalent of how traditional stock brokerages and investment firms handle fiat currency and equity trading in public stock markets. CeFi, unlike fiat currency equity trading, is not as tightly regulated all around the world, though there are regulations across Western economies, including the U.S. and Europe.
CeFi often requires Know Your Customer (KYC) compliance, which confirms a user's identity before they can begin using a centralized exchange. By authenticating the user's identity, KYC seeks to help prevent tax evasion, money laundering and terrorist funding.
In the CeFi model, custody of assets is held by a central exchange that is executing the transactions. As part of the asset management, the CeFi exchange holds the private keys for cryptocurrency wallets that enable access to cryptocurrency tokens on a blockchain. The central exchange is, in part, responsible for the safety, security and timely execution of transactions and properly reporting it all to the users. The central exchange in the CeFi model may charge handling and transaction fees to execute transactions, including buying, selling, trading and converting tokens.
CeFi exchanges are also commonly active in cross-chain bridge operations, enabling users to convert from one cryptocurrency token to another. For many users, a CeFi-based approach is also the first entry point into the cryptocurrency market as CeFi exchanges enable users to purchase cryptocurrency tokens with fiat currency.
The ability to execute transactions on margin, as well as the ability to directly provide loans, are also capabilities that can be associated with the CeFi model.
What are the advantages of CeFi?
There are numerous advantages to the CeFi model:
- Customer service. Customer service is part of what many CeFi cryptocurrency exchanges provide to support users.
- Fiat conversion. CeFi exchanges can enable the conversion of fiat currency to cryptocurrency.
- Cross-chain support. CeFi provides mechanisms for cross-chain exchange across multiple cryptocurrency tokens.
- Margin trading. Some CeFi exchanges enable users to trade with margin accounts, where a portion of the value is loaned with interest to the user.
- Income. CeFi provides the possibility of interest income on assets.
What are the disadvantages of CeFi?
There are several disadvantages to CeFi:
- Custody. Funds are held outside of user custody.
- Regulatory risk. There is a potential risk from regulatory authority compliance.
- Accounting. Accounting and reconciliation are all handled by CeFi, rather than being entirely enabled via code in a smart contract.
Examples of CeFi
Examples of CeFi companies are the following:
- Binance
- Coinbase
- Gemini
- Kraken
- Nexo
What is decentralized finance?
With DeFi, cryptocurrency transactions -- including buying, selling, loans and payments -- can be enabled in a peer-to-peer approach.
DeFi takes a different approach to cryptocurrency trading than its CeFi cousin. With DeFi, there is no centralized exchange that holds custody over assets. Rather, the individual traders hold custody over the assets with control of the private keys. Instead of a central authority that users must rely on to execute transactions, there is a smart contract-based approach that generally runs on top of Ethereum-based blockchains.
While DeFi is all about removing any form of centralized control, it does use decentralized exchanges (DEXs) to help facilitate cryptocurrency operations. DEXs are not intended to act as authorities for executing transactions, but can serve to help enable the flow of transactions. There is a related concept of decentralized apps (dApps), which can also be used to help enable DeFi use cases with smart contract-based applications.
In DeFi, model fees that are often associated with financial services transactions are removed as the model is decentralized without a central authority to charge service fees.
What are the advantages of DeFi?
There are multiple advantages to DeFi:
- Custody. Custody over funds is controlled by the user.
- Permissionless. There is no third-party identity verification needed, enabling what is referred to as a permissionless system.
- Anonymous. DeFi can enable anonymous use of service and financial transactions.
- DApps. DeFi supports new types of applications for financing, including dApps.
- Fees. DeFi offers lower fees than CeFi-based transactions.
What are the disadvantages of DeFi?
There several potential disadvantages to DeFi:
- Complexity. The DeFi model relies on sophisticated algorithms and smart contracts.
- Security. DeFi systems have become a high-priority target for attackers.
- Volatility. Volatility can be an issue as there is no central authority.
- Customer service. There is no customer service since the technology is largely driven by algorithms, not humans.
Examples of DeFi
Examples of DeFi companies include the following:
- 1inch Network
- MakerDAO
- PancakeSwap
- Stargate Finance
- Uniswap
Similarities between centralized and decentralized finance
While there are differences between CeFi and DeFi approaches for cryptocurrency, there are also a fair number of similarities across the two models as well.
Both DeFi and CeFi rely on blockchain technologies as the fundamental basis of operations. With blockchain at the core, the two approaches are both commonly used to deliver a wide range of cryptocurrency-related financial services. Both DeFi and CeFi at their core enable individuals to perform a series of common foundational operations, including the ability to buy, sell and trade cryptocurrencies.
DeFi works off Ethereum smart contracts, which can also find their way into CeFi use cases as well with some authority attached to help set up, manage and operate the contract. While it might be easier for regulators to impose different types of financial compliance on CeFi, it's still likely that profits from CeFi won't escape the notice of government tax authorities either.
There is also a nontrivial amount of security risk associated with both CeFi and DeFi. While DeFi has been more targeted by attackers, there are also ongoing attacks against CeFi. However, with CeFi, the central authorities can and should be taking additional steps to help secure operations.
Certainly, there are some important differences between CeFi and DeFi, but they both have the same core fundamental goal of promoting and enabling the use of cryptocurrency.








