transactional data
What is transactional data?
In computing, transactional data is the information collected from transactions. Ideally, the information includes all the details necessary to define each transaction as a unique event at a specific date and time. For this reason, the data that describes the transaction often includes a unique identifier (UID) and timestamp.
A transaction, in this context, is a sequence of related tasks that are treated as a logical unit of work. Transactional data is usually collected on an ongoing basis as part of an organization's daily business operations. For example, an organization might collect transactional data about its online product sales, credit card purchases or checking account deposits and withdrawals, depending on the nature of the business.
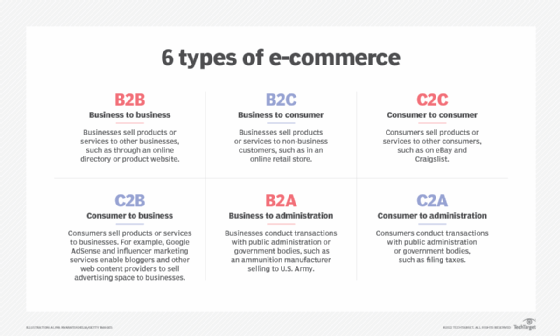
Transactional data is often associated with sales events, but it can include a wide range of financial, logistical or work-related events, including the following activities:
- Customer sales from an e-commerce site.
- A manufacturer's purchase orders for raw materials.
- Shipping status of merchandise as it moves from one shipping point to the next.
- Stock purchases and sales handled by a brokerage firm.
- Employee hours worked on each shift.
- Accident claims from auto insurance customers.
- Payments made on a bank car loan.
- Cryptocurrency purchases through a public blockchain.
How is transactional data managed?
Transactional data is often managed through a relational database management system (DBMS) such as SQL Server or MySQL. Such systems include built-in transactional processing capabilities and are based on the Structured Query Language (SQL), which incorporates transaction capabilities directly into its syntax. Relational database transactions typically adhere to the four ACID properties: atomicity, consistency, isolation and durability.
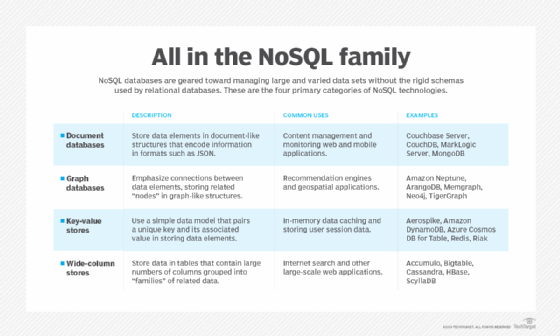
Some NoSQL databases are also used for transactional data and consequently support transactions. For example, MongoDB ensures that an operation on a single document is atomic, and it can handle distributed transactions by providing atomicity for reads and writes to multiple documents. In addition, blockchain technologies are commonly used to record the details of a transaction, which in this case, refers to the transfer of value between two users on a blockchain peer-to-peer network.
Transactional data, master data and reference data
Transactional data can include or refer to master data, reference data or both. Master data is the core data that an organization maintains to support its business processes. It is the functional data that describes the entities at the heart of the business. For example, master data might include information about customers, products, partners, employees, suppliers or store locations.
In contrast, reference data provides information that supports the organization's master and transactional data. It includes less critical information, such as languages, currencies, sales territories, postal codes or similar types of lookup data.
Transactional data often incorporates master or reference data to provide a complete picture of the transaction. For example, if a customer purchases a product online, transactional data for that sale will likely include some type of transaction ID or sales ID, along with a timestamp, purchase amount and other attributes specific to that transaction.
However, the data might also include a customer ID, product ID and store ID, which point to the master data, as well as a currency ID and territory ID, which point to the reference data. Only by including the master and reference data can the transactional data include a complete snapshot of the event so it can be understood. For example, the following figure illustrates what this transaction might look like in a relational database.
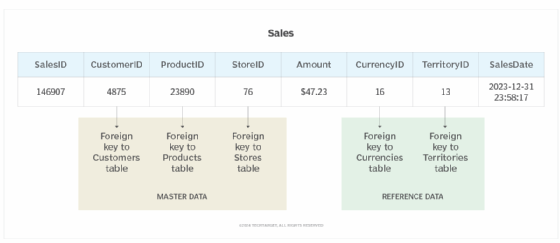
The figure shows the transaction as it appears in the Sales table, which includes one row for each sales transaction. In this case, all the data for this transaction is represented by a single row in the Sales table. (The figure shows only this row, along with the column names.) However, this is a very simple example, and the transactional data might span multiple rows in multiple tables.
In this example, the table includes the CustomerID, ProductID and StoreID columns. Each column references a related table. The three referenced tables -- Customers, Products and Stores -- are considered part of the master data. In a relational database, these types of references are implemented as foreign key relationships.
The Sales table also includes the CurrencyID and TerritoryID columns, which reference the Currencies and Territories tables, respectively. These tables are part of the reference data. However, all the data in this row is considered transactional data because it applies to a specific transaction. By extension, all the rows in the Sales table are also considered transactional data.
Today, the DBMS market is dominated by RDBMS, but NoSQL database systems continue to grow in popularity. Learn how cloud databases are deployed and managed and the benefits of using them. Explore e-commerce trends, tips and traps to avoid and see what IT skills are required for e-commerce. Also, check out this blockchain terminology glossary for beginners.
