Build, operate, transfer (BOT)
What is build, operate, transfer (BOT)?
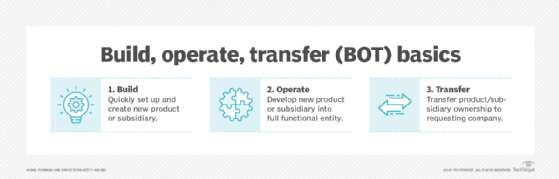
Build, operate, transfer (BOT) is a project management technique where a company hires a third-party firm to create a new subsidiary or product. At the end of the project, the entire subsidiary, including personnel and intellectual property, is transferred to the original requester. The BOT model is good for software development projects outside the company’s core competencies or to quickly create a team in a country where they don’t already have a presence. Design, build, operate, transfer (DBOT) is the same structure as BOT.
Build, own, operate, transfer (BOOT) is similar, except the contractor continues to own the newly formed product or organization for many years before transferring ownership. BOOT is more prevalent for public infrastructure projects with government contacts. Another project management technique called build, own, operate results in project ownership not being transferred to the requestor at the end of the contract.
Build, operate, transfer for IT
The BOT project model is a good option when a company needs to quickly create a new product or subsidiary that is outside their existing scope of operations. An outside contracting company handles the process of leasing office space and equipment, hiring and training workers, and fulfilling regulatory compliance for the new subsidiary. At the end of the contract, ownership is completely transferred to the project requestor.
Build, operate, transfer software development
In a BOT software development, the contracted company handles the end-to-end development of a product. Once the product is finished the requesting company will take ownership of it, any required infrastructure and some personnel to maintain it. Good projects for BOT are a website or application.
Build, operate, transfer for subsidiaries in new countries
Many companies may be looking to open new offices or subsidiaries in new countries. As technical skills become more common, developing countries can offer highly skilled workers at more competitive rates than in developed countries. For instance, it may be possible to open a new office for a software development division in a developing country for the same amount of hiring a few U.S.-based workers for a similar role. Eastern Europe, India and South-East Asia are popular areas to open an office in because the workforce is trained for computer work, but the costs of office space and salaries are low.
Many companies may shy away from opening an office in these areas due to the difficulty in getting started. There may be legal or registration requirements to open an office. Cultural differences also need to be considered for the candidate selection and hiring process. The BOT process offers a way to get over these initial hurdles in getting set up in a new country.
In a BOT project, an outside company that already does business in the target country is contracted to create the new subsidiary. This company will already have knowledge of the conditions in the country and have relationships to quickly find the needed material and personnel. The requesting company will be involved in the process so that their company culture and quality standards are followed.
In the build phase, they create the subsidiary. This involves legally registering the company and setting up bank accounts and documentation. They can then lease office space and equipment. They will then select candidates for leadership roles and begin hiring workers for the subsidiary.
In the operate phase, the fledgling subsidiary is developed into a fully functional organization. Office workers, human resources and accounting personnel are hired to make it self-sufficient. The support structure is put in place to ensure that it can operate on its own and that it meets the requirements of the contracting company.
In the transfer phase, ownership of the subsidiary is transferred to the requesting company. All its capital and personnel are transferred. It will now be fully part of the requesting company and ready to immediately begin operations. It can also handle any necessary local expansion.
Build, operate, transfer vs. outsourcing
The BOT model is an alternative to outsourcing. In outsourcing, the requesting company hires another company to fill a role, such as managing IT infrastructure or handling phone calls. They may be based in another country. The hired company ultimately controls the quality of the service and how the details of the work are handled. A service-level agreement will often define how the two companies work with each other. Because the contracted company is only incentivized to meet the contractual requirements, it can sometimes result in poor project performance.
By contrast, at the end of the BOT process, the quality of the work is ensured. Before ownership of the subsidiary is transferred, there will have been opportunity for the teams to work together. The requestor will know that their standards were met. After they take ownership, any new issues can be handled as an internal matter instead of using back-and-forth discussions or contract negotiation with another company.
Build, own, operate, transfer
In a BOOT project, the contracted company maintains ownership of the subsidiary for many years to decades to recoup the costs of the build. After the contacted period is over, ownership is then transferred. BOOT is mainly used by governments for large infrastructure projects. A BOOT is a public-private partnership.
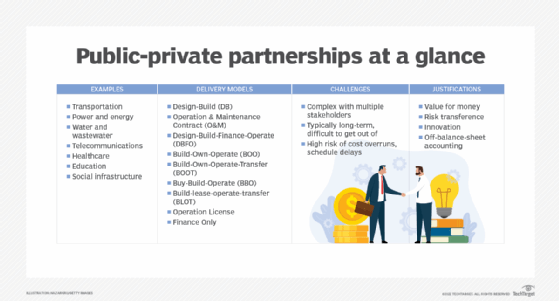
For example, a water treatment plant or power plant may cost many millions of dollars -- much more than a small government may have in its budget. Instead of paying to build it, they instead create a BOOT contract for a private company to build and operate the plant. While the plant is in operation, the company gets the profit from the fees collected from the users of the service, which pays for the construction cost. At the end of the contract, the company makes a profit, and the government provides a vital service.
Learn the differences between project vs. program vs. portfolio management.
