URN (Uniform Resource Name)
What is a URN (Uniform Resource Name)?
A URN (Uniform Resource Name) is a permanent identifier for internet resources and employs the urn scheme. It's essentially a location-independent string of characters that identifies every resource on the internet, regardless of its form, such as a website or email.
URNs are defined namespaces assigned by a namespace authority, so they remain unique and persistent over time even after the resource they are attached to moves or ceases to exist. For example, unlike a URL (Uniform Resource Locator), which becomes invalid when data is moved to a different location, the URN remains constant when objects and resources move.
The structure of a Uniform Resource Name
A URN is rendered in URI (Uniform Resource Identifier) syntax. The first part of the syntax signifies the name of the resource, followed by information that is separated by a colon:
urn:<nid>:<nss></nss></nid>
The following three items are included in a URN syntax:
- The leading scheme. The leading scheme is the urn:, which is case-sensitive.
- Namespace identifier (NID). The NID is the namespace identifier and can include letters, digits and dashes.
- Namespace-specific string (NSS). The NID is followed by the NSS, whose representation depends on the specified namespace and may contain American Standard Code for Information Interchange letters and digits, certain punctuation and special characters.
To ensure the global uniqueness of URN namespaces, their persistent identifiers (NIDs) are required to be registered with the Internet Assigned Numbers Authority.
Although different resource types can be specified through a URN, it's typically used in media formats such as libraries and journals, where they're used to clearly identify book numbers, serial numbers and other content.
Examples of a Uniform Resource Name
A URN contains information about how to fetch a resource from its location.
The following are examples of a URN.
Example 1
urn:efg://wxyz
Here, efg:// is the namespace identifier and can be an accessible directory for all encyclopedias and dictionaries on the internet, whereas wxyz is the NSS.
Example 2
urn:isbn:0143039431
Here, the URN is used to identify a 2006 version of The Grapes of Wrath by its International Standard Book Number (ISBN).
Example 3
urn:issn:1476-4687
Here, the scientific journal called Nature is identified by its International Standard Serial Number (ISSN).
Differences and similarities among URN, URI and URL
In the 1990s, URNs were conceptualized to be included in the information architecture for the internet. The other parts of this architecture included the URLs and the URCs (Uniform Resource Characteristics), which is a metadata framework.
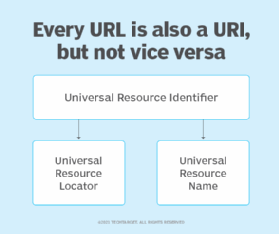
All three -- URI, URL, and URN -- are used to identify resources and names on the internet, but there is a subtle difference between them. Both Request for Comments 1737 and RFC 2141 distinguish URNs from URLs.
The following are the main characteristics of a URN, URL and URI.
URN
- A URN identifies a resource by its name and always begins with the prefix urn: -- for example:
- urn:isbn:0143039431 identifies a book by its ISBN.
- urn:uuid:6e8bc430-9c3a-11d9-9669-0800200c9a66 is a globally unique identifier.
- urn:publishing:book is an Extensible Markup Language namespace that identifies the document as a type of book.
- Both the URN and URL share certain similarities and are subcategories of the URI.
- URNs can identify ideas and concepts and aren't restricted to identifying documents. However, when it does identify a document, it can be translated into a URL by a hostname resolver, and the document can be downloaded from the URL.
- URNs are interoperable with existing standard identifier systems, like ISSN, which is an eight-digit code used to identify newspapers, magazines, journals and periodicals on all print and electronic media.
URL
- A URL contains both the location of the resource that needs to be fetched and the protocol required for retrieving it, such as Hypertext Transfer Protocol (HTTP) or File Transfer Protocol (FTP) -- for example:
- http://example.com/mypage.html.
- ftp://example.com/download.zip.
- mailto:[email protected].
- file:///home/user/file.txt.
- http://example.com/resource?foo=bar#fragment.
- /other/link.html (a relative URL that is only relevant in the context of another URL).
- URLs are addresses assigned to web servers and other media that allow access to the internet.
- URLs always begin with a protocol, such as HTTP, and typically contain information, including the network hostname and often a document path, such as /foo/mypage.html.
- URLs may have fragment identifiers and query parameters.
- URLs are most commonly used to reference webpages but can also be used for file transfer, email, database access and other applications.
URI
- A URI is a string that is used to identify a resource, as opposed to URLs and URNs that are used for locating it.
- URIs encompass both URLs, URNs and other ways to identify a resource.
- A data URI, such as data: Hello%20World, is a good example of a URI, as it's neither a URL nor a URN because it contains the data. It neither names it nor describes how to locate it over the network.
A domain name system server is used for resolving hostnames to IP addresses. Learn how to troubleshoot name resolution on different operating systems, including Windows, Linux and macOS.
