What is email (electronic mail)?
Email (electronic mail) is the exchange of computer-stored messages from one user to one or more recipients via the internet. Emails are a fast, inexpensive and accessible way to communicate for business or personal use. Users can send emails from anywhere as long as they have an internet connection, which is typically provided by an internet service provider.
Email is exchanged across computer networks, primarily the internet, but it can also be exchanged between both public and private networks, such as a local area network. Email can be distributed to lists of people as well as to individuals. A shared distribution list can be managed using an email reflector. Some mailing lists enable users to subscribe by sending a request to the mailing list administrator. A mailing list that's administered automatically is called a list server.
The TCP/IP suite of protocols provides a flexible email system that's built on basic protocols, including Simple Mail Transfer Protocol (SMTP) for sending mail, and Post Office Protocol 3 (POP3) for receiving mail. Alternatively, the Internet Message Access Protocol (IMAP) can be used for receiving mail, as it enables access to email from any device, anywhere. With POP3, the email message is downloaded from the email service and stored on the requesting device and can only be accessed using the same device.
Email messages are usually encoded in American Standard Code for Information Interchange (ASCII) format. However, users can also send non-text files -- such as graphic images and sound files -- as file attachments. Email was one of the first activities performed over the internet and is still the most popular use. A large percentage of the total traffic over the internet is email.
Differences between email and webmail
Today, the term email is often used to include both browser-based electronic mail, such as Gmail and AOL Mail, and non-browser-based electronic mail accessed through an email client such as Microsoft Outlook for Office 365. However, in the past, email was defined as a non-browser program that required a dedicated email server with the client software installed on the computer.
The advantages of using non-browser email include easier integration with business software platforms, enhanced security and lack of advertisements. However, in order for the email to be accessed, it requires an email client be installed directly onto the computer. Although many email clients are free, others are available for a minimal charge.
The biggest advantage of webmail is that it's free to use, can be accessed from anywhere and is hosted in the cloud, which automatically synchronizes the email to all devices, including desktop computers, tablets or smartphones.
The main components of an email message
A mail message transfer agent is software that transfers emails between the computers of a sender and a recipient. No two email addresses can be identical, as each complete address must be unique.
Typically, an email message consists of two main components: header and body.
Header
Each email message comes with a header that's structured into various fields. These fields contain important information regarding the sender and the recipient(s). However, the content of the email header varies, depending on the email system being used.
Typically, an email header contains the following information:
- Subject. This provides a summary of the message topic and is displayed in a separate line above the message body. For example, a subject line might say "Company mission statement" or "Employee Stock Purchase Plan."
- Sender (From). This field is the sender's email address. A display name can also be shown instead if it's associated with the email address. Most email clients fill out this field automatically.
- Date and time received (On). This field shows the local time and date when the message was composed. It's a mandatory header field that's filled automatically by most email clients.
- Reply-to. If a user clicks on the Reply button, this field automatically populates the message with the sender's email address, which now becomes the "recipient."
- Recipient (To). This field shows the first and last name of the email recipient, as configured by the sender.
- Recipient email address. This is the email address of the recipient or where the message was sent.
- Carbon copy (CC). The carbon copy field includes the email addresses of the people who need to receive the email but aren't expected to reply. When a person presses Reply All, all of the CC addresses receive the response.
- Blind carbon copy (BCC). If a sender doesn't want their recipient to find out who else received the email, they could use the BCC field to enter those addresses. The addresses in the BCC list don't receive responses when someone presses Reply All.
- Attachments. This field contains any files that are attached to the message.
Body
This is the content of the email. It may contain anything the user wishes to send, including text, videos or file attachments. Depending on the email client used, the email body can be formatted in either plain text or HTML. While plain text messages can't contain special formatting or multimedia elements, HTML emails enable special formatting and inclusion of multimedia options within the body of the message. The message body may also include signatures or automatically generated text that the sender's email system inserts.
Uses of email
The following are the most common use cases for email:
- Individual or group communications. Email is a beneficial way to communicate with individuals or small groups of friends or colleagues. It enables users to easily send and receive documents, images, links and other files. It also gives users the flexibility to communicate with others on their own schedule.
- Notifications, reminders and follow-ups. Individuals, small groups or organizations can send follow-up emails after appointments, meetings or interviews, or to remind participants of approaching events, due dates and time-sensitive activities. Calendars with the ability to add appointments and events are integrated into most email platforms. These features help users with time management by visualizing the fixed amount of time they have in a day. This enables users to prioritize their decisions and time.
- Conveying information to a large group of people. Companies can use email to convey information to a large number of employees, customers and potential customers. Email is frequently used for newsletters, where mailing list subscribers are sent specific, promoted content from a company and direct email marketing campaigns, where an advertisement or promotion is sent to a targeted group of customers.
- Turning leads into paying customers. Email can also be used to make a potential sale into a completed purchase. For example, a company may create an automated email that's sent to online buyers who keep items in their shopping cart for a specific amount of time. The email may remind the customer that they have products sitting in their cart and encourage them to complete the purchase before the items run out of stock.
- Reviews and surveys. Follow-up emails asking customers to submit a review after making a purchase may include a survey asking them to review the quality of service or the product they've recently received.
Types of B2B emails
Business-to-business (B2B) email marketing is used by businesses that are trying to facilitate the exchange of information, products or services between their organization and others. It differs from business-to-consumer (B2C) email marketing because it focuses on relaying the logic and reasoning behind a specific purchase decision in relation to a business's specific needs, rather than appealing to the emotions of consumers to convince them to buy a product. Some different types of B2B emails include the following:
- Welcome emails are sent to possible buyers after they subscribe to a business's opt-in activities, such as a mailing list, blog or webinar. They often contain additional information that's useful to the new subscriber. Sending a series of welcome emails can help the business establish a relationship with the buyer and improve subscriber loyalty.
- Promotional emails offer some sort of deal to buyers, such as a percentage off the purchase price, a free month of service, or reduced or omitted fees for managed services. This is the most common type of B2B email.
- Lead-nurturing emails are used to educate potential buyers on the offerings and services available in an attempt to make any prospective sale into a completed purchase. Lead-nurturing emails are also known as trigger campaigns, since they're initiated by a potential buyer taking an initial action, such as downloading a free sample or clicking links on a promotional email. Lead-nurturing emails should be short and focused. They should use behavioral data that has been gathered about the lead to target the content and continue engagement with the potential buyer over time.
- Newsletter emails are routinely sent to all mailing list subscribers, either daily, weekly or monthly. They contain selected content that the company has recently published. These emails provide businesses with the opportunity to convey important information to their clientele through a single source. Newsletters may incorporate headlines or captions of industry-related news with links to the full articles, event invitations, company blog posts and content offers.
- Onboarding emails -- also known as post-sale emails -- are often used to strengthen customer loyalty. These emails can be used to familiarize buyers with the provided services or educate them on how to use their newly purchased products. These emails often include advice on how to use and manage the new products or services. Onboarding emails can help clients simplify user adoption when faced with large-scale service deployments.
Advantages of email
Email is a fast, reliable and portable way of communicating with others. The following are some common benefits of using email for both personal and professional purposes:
- Cost-effectiveness. There are various free email services available to individuals and organizations. Once a user is online, there are no additional charges for the service.
- Flexibility. Email provides users with a nonurgent communication process that enables them to send a response when it's convenient for them. This also encourages users to communicate regardless of their different schedules or time zones.
- Easy access. If the user has access to the internet, then email can be accessed from anywhere at any time.
- Speed and simplicity. Emails are quick and easy to compose, with information and contacts readily available. They can also be exchanged quickly with minimal lag time.
- Mass delivery. Email makes it possible and easy to send one message to large groups of people.
- Message filtering. Email enables users to filter and categorize their messages. This can prevent the visibility of unwanted emails, such as spam and junk mail, while also making it easier to find specific messages when they're needed.
- Message storage and retrieval. Email exchanges can be saved and searched for easy retrieval. This enables users to keep important conversations, confirmations or instructions in their records and quickly retrieve them if necessary.

Examples of email attacks
Email is the most common vector for cyber attacks. Methods include spamming, phishing, spoofing, spear-phishing, business email compromise and ransomware. According to a list of cybersecurity threats compiled by TechJury, about 91% of cyber attacks launch with a phishing email.
The following are some common methods of using email to conduct cyber attacks:
- Spamming. Email spam, also known as junk email, is unsolicited bulk messages sent through email. The use of spam has been growing in popularity since the early 1990s and is a problem faced by most email users. Recipients of spam often have had their email addresses obtained by spambots, which are automated programs that crawl the internet looking for email addresses. Spammers use spambots to create email distribution lists. A spammer typically sends an email to millions of email addresses, with the expectation that only a small number will respond or interact with the message.
- Phishing. This is a form of fraud in which an attacker masquerades as a reputable entity or person in email or other communication channels. The attacker uses phishing emails to distribute malicious links or attachments that can perform a variety of functions, including extracting login credentials or account information from victims.
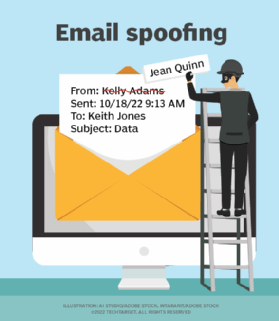
- Spoofing. Email spoofing is the forgery of an email header so that the message appears to have originated from someone or somewhere other than the actual source. Email spoofing is a popular tactic used in phishing and spam campaigns because people are more likely to open an email when they think it has been sent by a legitimate or familiar source. The goal of email spoofing is to get recipients to open, and possibly even respond to, a solicitation.
- Spear phishing. Spear-phishing attacks target a specific organization or individual, seeking unauthorized access to sensitive information. Spear-phishing attempts aren't typically initiated by random hackers but are more likely to be conducted by perpetrators out for financial gain, trade secrets or military information.
- Business email compromise (BEC). A BEC is an exploit in which the attacker gains access to a corporate email account and spoofs the owner's identity to defraud the company or its employees, customers or partners of money. In some cases, an attacker simply creates an account with an email address that's similar to one on the corporate network. A BEC is also referred to as a man-in-the-email scam.
- Ransomware. Ransomware is a subset of malware in which the data on a victim's computer is locked, typically by encryption, and payment is demanded before the ransomed data is decrypted and access is returned to the victim. The motive for ransomware attacks is nearly always monetary, and unlike other types of attacks, the victim is usually notified that an exploit has occurred and is given instructions for how to recover from the attack. Payment is often demanded in a virtual currency -- such as bitcoin -- so that the cybercriminal's identity isn't known.
Email security
Email is designed to be an open and accessible platform that enables users to communicate with each other and with people or groups within an organization. As a result, it isn't inherently secure, and email security is vital. Email security describes the various techniques that individuals, organizations and service providers can use to protect sensitive information kept in email communications and accounts from unauthorized access, loss or destruction.
Organizations should implement the following best practices to ensure proper email security:
Password rotations. Individuals can proactively protect their accounts by creating strong passwords and changing them frequently.
Spam filters. Users should also create spam filters and folders to separate potentially malicious emails and junk mail, as well as install and run antivirus and antimalware software on their computers. Service providers should install firewalls and spam-filtering software apps to protect users from unrecognized, malicious or untrustworthy messages.
Secure email gateway. Organizations can protect themselves from threats by setting up an email security gateway. Email gateways process and scan all received emails to prevent attacks from reaching their intended recipients. A multilayered gateway is the best approach, since attacks are becoming increasingly more complicated and sophisticated. Training employees on how to properly use email and how to distinguish malicious messages can also help users avoid threatening mail that the gateway doesn't catch.
Automated email encryption. Automated email encryption software can be used to scan all outgoing messages for potentially sensitive information. If the material is considered sensitive, then the content should be automatically encrypted before it's sent to the intended recipient. This process prevents attackers from gaining access to this information, even if they intercept it. Only recipients with permission to view the email can see the decrypted content.
Access control standards. Email service providers can also improve email security by establishing strong password and access control standards and mechanisms.
Digital signatures and encryption. In addition to organizations using automated encryption software, providers should also use encryption and digital signatures to protect emails in transit and in users' inboxes.
Popular email sites
Some examples of popular, free email websites include the following:
- Gmail is a free email service provided by Google. Gmail also offers paid plans for business users that include extra storage, advanced features and support options. According to Litmus in its "July 2022 Email Client Market Share" update, as of April 2022, Gmail holds 29.5% of the email client market share.
- Microsoft Outlook is available as part of the Microsoft Office suite and offers both free and paid versions. Microsoft Outlook works across several operating systems and devices and provides features such as deleted email recovery and automatic email organization.
- Yahoo Mail was launched in 1997 and is one of the oldest webmail clients available. Yahoo Mail is useful for personal emails and comes in a mobile app version.
- AOL Mail was one of the most popular email services in the past and is now a part of Verizon Communications. It offers an unlimited mailbox size and lets users link their AOL Mail to other email accounts, such as Outlook and Gmail.
- Zoho Mail was launched in 2008 and is part of the Zoho Office Suite. This email client provides great security and affordable plans for both personal and business use. According to a survey conducted by Zoho, it had 15 million users worldwide in 2020.
- ProtonMail offers enhanced security and end-to-end encryption. It also provides features including Proton Calendar and Proton Drive.
- iCloud Mail is a free email address for Apple users and comes preinstalled on Apple devices. As long as a user has an Apple account, they can connect to iCloud mail using their Gmail, Yahoo Mail or AOL email address. ICloud Mail offers each account 5 GB of cloud storage and additional space can be purchased.
Origin of email
Scientists at MIT developed a program called Mailbox that enabled the exchange of messages between time-sharing computers within one lab. In 1971, Raymond Samuel Tomlinson, a developer at Bolt, Beranek and Newman -- now Raytheon BBN Technologies -- executed the first email program on the Advanced Research Projects Agency Network (ARPANET), the precursor to the internet. Tomlinson designed a messaging program for use on the PDP-10 computer consisting of two individual programs, SNDMSG for sending mail and READMAIL for retrieving mail.
Email is the most common point of entry for cybercriminals into a network. Learn about the top 3 email security threats and how to defend against them.