What is quantum technology? Use cases and future implications
Quantum technology is a field of physics dedicated to developing new and innovative technologies based on the principles of quantum mechanics. Quantum mechanics are the laws of physics that apply to subatomic particles, which were first explored in the 1920s by physicists Niels Bohr, Werner Heisenberg and Erwin Schrödinger.
Quantum technology principles are already incorporated into established technologies such as nuclear power and cell phone semiconductors. Now, the field is focused on using unique quantum properties in emerging applications. These include quantum computing, quantum communication and quantum sensing, all aimed at achieving capabilities that surpass what classical technologies do.
How does quantum technology work?
Quantum technology harnesses the unique features of quantum mechanics to perform tasks in fundamentally new ways. Unlike classical technologies, which rely on binary states of 0s and 1s, quantum technologies exploit quantum phenomena, such as superposition, entanglement and quantum tunneling, to perform tasks that are impossible for classical systems to do. Quantum technology is significantly more expensive than classical technology.
Here are the key concepts of quantum computing that highlight how it works:
- Superposition. Unlike classical bits, which can only be 0 or 1, quantum bits -- also known as qubits -- can exist in multiple states simultaneously. This capability enables quantum computers to process vast amounts of information in parallel, enhancing their computational power.
- Entanglement. In this quantum phenomenon, two or more qubits become linked in a way that they share the same fate, no matter how far apart they are. Measuring the state of one entangled qubit instantaneously determines the state of the other. Entanglement is used to create powerful correlations for computation and secure communication.
- Interference. Quantum systems can interfere with one another, amplifying correct paths and canceling out wrong ones. This property of quantum algorithms is used to find outcomes more efficiently than with classical algorithms.
- Quantum sensing. Quantum sensing uses quantum mechanics principles to measure physical quantities with extreme precision. For example, quantum sensors can detect minute changes in magnetic and electric fields, which is useful in applications such as medical imaging and navigation systems.
- Quantum communication. Quantum communication uses quantum entanglement to establish secure communication channels. One notable application is quantum key distribution (QKD), which ensures that any attempt to intercept a message will disturb the quantum state of the system, thereby alerting both the sender and the receiver to the intrusion. This makes quantum communication secure and protects against eavesdropping.
Investments in quantum technology
Developing and executing quantum technology is expensive. It requires highly specialized and often custom-built hardware to maintain the extreme temperatures and precise control over quantum states. The complexity of fabricating qubits, the limited pool of expert scientists and engineers, and the ongoing research into quantum algorithms and software all contribute to the high costs associated with this field.
However, quantum technology is becoming a strategic priority for businesses and governments around the globe. Acknowledging its transformative potential, significant investments are being directed toward quantum research, development and commercialization. Public funding initiatives from various governments include the following:
- United States. The U.S. has committed substantial resources to quantum initiatives. The 2022 CHIPS Act allocated about $174 billion to various scientific projects, including quantum computing, materials science and biotechnology. The National Quantum Initiative (NQI) Act of 2018 provided a $1 billion annual budget dedicated to quantum research, fostering innovation and collaboration across federal agencies and private sectors. In 2024, Congress allocated $968 million to the NQI. Furthermore, the Department of Energy announced $65 million in funding for quantum computing research projects in September 2024.
- United Kingdom. The U.K. government announced a £121 million boost for quantum technology in April 2025, which is specifically aimed at tackling fraud, preventing money laundering and driving economic growth. In 2024, the U.K. allocated £106 million for five quantum research hubs focusing on areas such as quantum sensors for disease diagnosis, secure quantum internet and quantum-based navigation systems.
- European Union. Under the EuroHPC initiative, the first European quantum computers will be hosted across six sites in the EU: Czechia, Germany, Spain, France, Italy and Poland. The total planned investment for this initiative is more than €100 million, with participation from 17 European countries.
- Germany. Germany unveiled a €3 billion action plan in 2023 to develop a universal quantum computer by 2026.
- China. China has established itself as a significant player in quantum technology by investing over $15 billion in government funding. This surpasses the investments made by both the U.S. and the EU. This commitment highlights China's strategic focus on research and development in quantum technology. China is also launching a government-backed fund of $138 billion to support emerging technologies, including quantum computing.
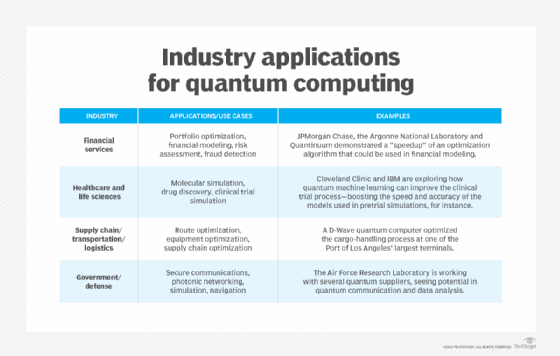
Use cases for quantum technologies
Quantum technology offers a range of possible use cases across various fields. Here are some key use cases and applications of quantum technology.
1. Healthcare and drug discovery
Quantum computing's ability to simulate complex molecular interactions is rapidly advancing healthcare uses. It has the potential to transform the following four key areas in healthcare and medicine:
- Acceleration of drug discovery and development. Quantum computing is poised to speed up the identification of promising drug candidates and to predict their effectiveness by simulating molecular interactions with great precision. Industry leaders, such as Google and IBM, are pursuing quantum-powered drug research to accelerate the development of treatments and cures for complex diseases.
- Accuracy in medical imaging. The use of quantum-enhanced machine learning (ML) for analyzing medical images, such as MRI and CT scans, can significantly improve accuracy in detecting abnormalities. This capability is revolutionizing early, precise diagnoses, especially in the case of diseases such as cancer.
- Personalized treatment plans. Quantum algorithms can analyze vast genetic and clinical data sets, opening the door to personalized treatment plans designed around an individual's genetic makeup. This advance promises more precise therapies and shorter trial-and-error processes often associated with prescribing treatments.
- Epidemiological disease modeling. Quantum computers can enhance the modeling of disease spread to aid public health officials in data-driven responses. Traditional models often struggle with the many variables involved, such as infection rates, demographic data and human behavior. Parallel processing lets quantum computing simultaneously analyze these factors, leading to better predictions. For example, researchers use quantum algorithms that are similar to the statistical physics Ising model to simulate infection spread and offer insights into disease propagation.
2. Enhancements in AI
Quantum technology can handle the computational challenges of training advanced AI models. Quantum computers use qubits, which can exist in multiple states simultaneously, letting them process vast amounts of data in parallel. This enables certain computations to be performed exponentially faster than classical computers. For instance, Google's Sycamore processor completed a task in 200 seconds that would take a supercomputer 10,000 years. Such advancements can significantly reduce training times for complex AI models, improving real-time decision-making in autonomous vehicles and personalized recommendations, for example.
Quantum computing can also improve ML algorithms, enabling more efficient data processing and optimization. For example, Grover's algorithm can search unstructured databases faster than classical algorithms, accelerating data mining and pattern recognition tasks. Quantum ML techniques, such as quantum neural networks, use quantum principles to solve ML problems more efficiently.
3. Supply chain and logistics
Quantum computing can analyze large data sets and explore multiple possibilities simultaneously, leading to optimized supply chains and logistics. This includes finding the most efficient routes, improving warehouse management and enhancing demand forecasting for better inventory control. Additionally, quantum sensors deliver more accurate real-time data on environmental conditions, the status of goods and equipment performance, enabling proactive maintenance and reducing disruptions.
Quantum communication also promises more secure data transfer across the supply chain by using principles such as quantum entanglement and QKD, which make it virtually impossible to intercept or tamper with information without detection. This ensures end-to-end encryption, enabling companies to confidently share sensitive data, such as inventory levels, shipping routes and supplier contracts.
4. Financial modeling and portfolio optimization
Quantum technology can quickly solve complex, multidimensional problems, marking a significant advancement in financial modeling and portfolio optimization.
Portfolio optimization requires balancing returns against risk while considering market volatility and other constraints. Quantum algorithms, such as the quantum approximate optimization algorithm (QAOA), excel at these complex optimization problems. They enable swift evaluation of countless portfolio scenarios and the potential for more precise investment strategies.
Quantum computing also enhances risk analysis through accelerated Monte Carlo simulations, providing a more thorough understanding of potential market outcomes.
5. Traffic optimization and smart cities
Quantum technology enables the real-time, data-driven decision-making needed to enhance traffic optimization and smart city infrastructure. It can process vast data sets and solve complex optimization problems in ways that will transform urban mobility.
Many organizations are building quantum computers to solve similar problems. For instance, Volkswagen has a pilot project in Lisbon that uses a D-Wave quantum computer to optimize routes for nine buses during peak traffic times. This approach reduced passenger wait times and improved traffic flow. Similarly, Ford and Microsoft have collaborated to apply quantum-inspired algorithms to manage traffic congestion in Seattle, processing numerous route variations simultaneously to direct thousands of vehicles more efficiently.
6. Weather forecasting and climate modeling
Quantum algorithms, such as the QAOA, have the potential to solve complex problems related to atmospheric modeling and improve weather forecasting and modeling.
These algorithms improve the accuracy of weather predictions. For example, quantum ML methods, such as quantum support vector machines, can efficiently process complex, high-dimensional atmospheric data. These techniques identify intricate patterns that classical forecasting methods might overlook, resulting in more accurate and faster predictions of hurricanes, tornadoes and other severe weather events.
Future implications of quantum technology
Quantum technology is set to revolutionize various industries. According to McKinsey, it could create trillions of dollars in value within the next ten years. Early gains are expected in the chemical, life sciences, finance and transportation sectors.
While some quantum technologies, such as lasers and MRI scanners, are already common, the future holds even more transformative possibilities. The following are some potential future implications of quantum technology:
- Airline network optimization. Various airlines are exploring the use of quantum algorithms to optimize flight planning, fleet allocation and real-time crew scheduling. These tasks involve numerous variables, such as weather conditions, air traffic and regulatory constraints, making them challenging for classical computers to solve efficiently. For example, Lufthansa has partnered with the German Aerospace Center to investigate how quantum computing can improve flight scheduling, crew management and resource allocation. Airbus is also working with IonQ and QC Ware to develop quantum options for optimizing aircraft loading and flight path planning.
- Ultraprecise sensors. Quantum sensors can achieve unprecedented levels of sensitivity and accuracy in measurements, potentially revolutionizing medical imaging, navigation and environmental monitoring. For example, quantum sensors made from defects in diamonds could provide MRI scans with atomic-level precision, leading to earlier and more accurate disease diagnoses. The tiny imperfections in diamonds function as sensitive quantum compasses, able to detect faint magnetic signals from individual atoms or small groups of atoms. These sensors can produce MRI-like scans with much greater detail than traditional MRIs.
- Enhancements in chemistry. Molecules and chemical reactions can be stimulated at the quantum level, enabling researchers to design and discover new molecules with tailored properties. This capability could lead to more efficient catalysts, new drug candidates, advanced materials for batteries and superconductors, and environmentally friendly refrigerants and solvents, among other breakthroughs.
- Economic and workforce implications. The quantum industry is projected to generate significant economic value. This growth will drive demand for skilled workers proficient in quantum technologies, necessitating investment in education and training programs.
When will quantum technology be accessible to organizations?
Quantum technology is already accessible to organizations for adoption and integration into business operations. Below is a timeline outlining what's now available, what to expect in the near future and how adoption is likely to evolve long term.
Current accessibility
Quantum technology is becoming increasingly available, primarily through cloud-based services. Instead of the significant investment required to own and maintain physical quantum computers, businesses and researchers can rent access to quantum processors on demand from companies such as Amazon, Google, IBM and SpinQ.
This quantum-as-a-service model offers several benefits, including cost efficiency, scalability and global accessibility, letting organizations experiment with quantum algorithms and explore potential applications without substantial upfront investment.
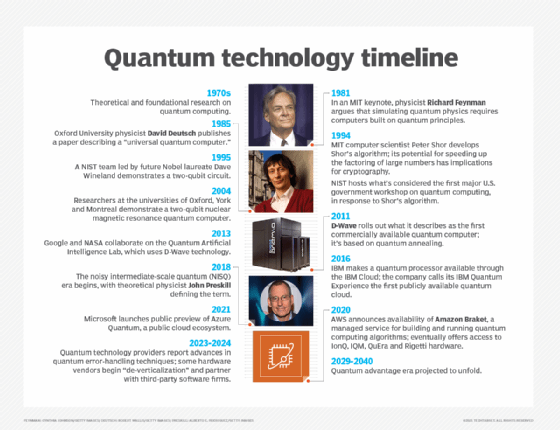
Near-term adoption
In the next five years, organizations are expected to increasingly adopt quantum computing for specific applications, especially in sectors such as pharmaceuticals, chemicals, finance and logistics. Hybrid computing models that combine classical and quantum systems are expected to become more common as well.
Companies are starting to prepare their IT infrastructure for quantum integration, concentrating on areas where quantum computing can provide a competitive advantage.
Long-term outlook
Looking ahead, the development of fault-tolerant quantum computers capable of outperforming classical systems in a range of applications is anticipated. Fully fault-tolerant, universal quantum computers are still in development and several years away from being available. However, early commercial quantum systems, such as quantum annealers, are already being used for optimization problems.
In preparation for this next phase, organizations are building quantum literacy, adopting quantum-safe cybersecurity practices and launching pilot projects to stay ahead in this rapidly evolving market.
Quantum technology is being used to boost optimization and prepare for future cryptography, despite ongoing technical challenges. Examine both the short-term and long-term potential of quantum technology.