contingency plan
What is a contingency plan?
A contingency plan is a course of action designed to help an organization respond effectively to a significant future incident, event or situation that may or may not happen.
A contingency plan is sometimes referred to as "Plan B" or a backup plan because it can also be used as an alternative action if expected results fail to materialize. Contingency planning is a component of business continuity (BC), disaster recovery (DR) and risk management.
Contingency planning and technology DR plan development are closely related concepts. The National Institute of Standards and Technology (NIST) standard for IT disaster recovery planning includes contingency in its title.
Over the years, the contingency planning process has been connected to other types of business-readiness plans based on standards developed around the world. These standards address issues related to BC, incident response (IR), cybersecurity, continuity of operations, critical infrastructure, crisis communications, emergency response, natural disaster response and organizational resilience.
Organizational resilience has evolved over the past couple decades, and some experts view it as an umbrella term for contingency plans and the other plan types discussed here.
Example of a contingency plan
A contingency plan can focus on one specific part of an organization's operations. For example, it can be the measures taken to back up all critical data. Another example would be work-from-home provisions put in place in case a facility is out of commission.
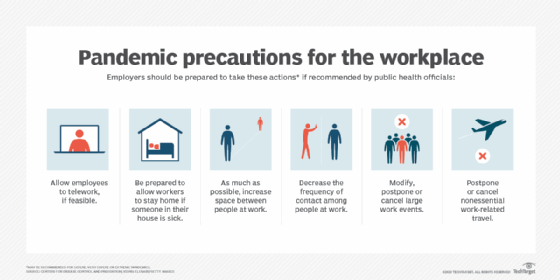
The COVID-19 pandemic demonstrated to many organizations the importance of having comprehensive contingency plans in place across an organization prior to an unplanned event. Companies with adequate plans were able to react faster when the pandemic started to escalate.
7 steps of a contingency plan
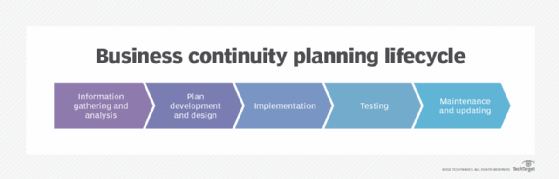
Contingency planning standards include a framework and structure for plan design and development. The plan structure is a repeatable format that simplifies the development of contingency and other plans.
A popular IT contingency plan model is defined in NIST SP 800-34 Rev. 1 (2010), "Contingency Planning Guide for Federal Information Systems." In includes the following seven steps:
- Contingency planning policy statement. This policy provides the outline and authorization to develop a contingency plan.
- Business impact analysis. BIA identifies and prioritizes the systems that are important to an organization's business functions.
- Preventive controls. Proactive measures that prevent system outages and disruptions can ensure system availability and reduce costs related to contingency measures and lifecycle.
- Contingency strategies. Thorough recovery strategies ensure that a system may be recovered fast and completely after a disruption.
- Contingency plan. This is the action plan. It contains the guidance and procedures for dealing with a damaged or unavailable system. These detailed plans are tailored to the system's security impact level and recovery requirements.
- Testing, training and exercises. Plan testing validates recovery capabilities, training prepares recovery personnel for plan activation and exercising the plan identifies planning gaps. Combined, these activities improve plan effectiveness and overall organization preparedness.
- Plan maintenance. The plan should be updated regularly to remain current with system enhancements and organizational changes.
Free, downloadable templates for BC and DR planning
A free business continuity template and guide
Other elements of a contingency plan
In accordance with current domestic and international standards, the following activities are also recommended for contingency plan development:
- Risk assessment. This step examines internal and external risks, threats and vulnerabilities to the organization and its technology infrastructure. It also looks at the likelihood of reoccurrence, the severity and potential impact to the organization, as well as the financial and operational effects. Best practice contingency planning includes performing a BIA and risk assessment to identify key risks and preventive measures and strategies to deal with them.
- Awareness training. Information about contingency plans and the other plan types is disseminated to employees, company leaders, customers and external stakeholders.
- Review and auditing. This ensures that the plan is examined periodically to check its consistency with current business and technology practices, as well as the accuracy of contact data. Periodic audits ensure alignment with relevant controls, standards and applicable regulations.
- Continuous improvement. Regularly revisiting the plan can help ensure that it meets the operational needs of the organization.
Business continuity vs. business contingency plans
The terms business continuity and business contingency are often used interchangeably. However, they differ in the following ways.
Business contingency. A business contingency plan is activated soon after the initial event occurs and the IR team has made its initial assessments and determinations. The contingency plan is used to get specific team members involved in mitigation efforts. These people make short-term decisions regarding how the incident can be managed and resolved.
Business continuity. If contingency planning activities are insufficient to restore business operations, it may be necessary to declare a disaster and launch a longer-term business continuity plan as well as a technology disaster recovery plan. BC plans are designed to facilitate the recovery and resumption of business activities to as close to normal operations as possible.
Benefits of contingency plans
When a disruptive or negative event occurs, contingency plans provide a structure for assessment and actions to recover from such unexpected events. The faster the recovery, the less potential there is for damage to occur to the organization and its employees. Speed in recovery also helps maintain a company's financial status, competitive position and reputation.
Learn more about business continuity and disaster recovery in this comprehensive guide.
