What is a disk image?
A disk image is a compressed file that contains a copy of the entire contents of a computer's hard drive or other storage media, such as optical discs or solid-state drives. The disk image represents the content exactly as it is on the original storage device, including both data and structure information.
A disk image is a byte-by-byte, sector-by-sector copy of the content on the original source drive. These images provide a single reference of a machine configured for an organization's computing environment.

How does a disk image work?
A disk image includes files and file folders, boot files, directories, file allocation tables, operating system (OS) attributes, slack space and unused storage capacity. Disk imaging software makes an image of a completely configured system. Because of its large size, a disk image file is compressed and stored on a secondary storage device or in cloud storage. Hard drive disk images can be saved as a virtual hard disk.
A disk image provides a single, consistent source for all computers in a group or organization on which the information on it is installed. It also can be mounted so that users can view it on their desktop as though it were an external drive. Authorized users have access to all file folders within a mounted disk image.
For enhanced security, the contents of a disk image file can be encrypted and password protected, much like any other computer system drive or device. There are many file formats used for disk images, which are identified by specific three-letter file extensions.
How are disk images used?
Disk images serve a variety of use cases, including the following:
- Computer forensics.
- Copying CDs and DVDs.
- Creating portable versions of a user's system.
- Data protection.
- Disaster recovery.
- Disk cloning or ghost imaging.
- Distribution of applications and OSes.
- Large-scale OS deployment and system migration.
- System backup.
What kinds of disks are included in a disk image?
Several types of storage media can be converted into disk images:
Is a disk image the same thing as an ISO file?
Disk images and International Organization for Standardization (ISO) files are similar, but have different origins. The disk image file format IMG originated to replicate images on floppy disks. IMG disk image files are still in use, but they are often converted to the ISO format to archive the entire contents of optical media as a single file.
ISO is the generally accepted format for disk images and is recognized by most OSes, which typically include native tools for extracting and reading disk image files in ISO format. ISO files make it easier to distribute software for installation through the internet.
In an uncompressed form, there is no discernible difference between an IMG and ISO disk image file. Compressing a disk image conserves storage, but some devices might not be able to read the image. It's possible to convert IMG files to the ISO format and vice versa using special file-conversion software.
Since it represents the contents of a physical drive, a disk image can be safely deleted after its associated application is successfully installed.
How are disk images mounted?
In Microsoft Windows, disk images are mounted and unmounted with the File Explorer tool or the Disc Image Tools tab on the Windows ribbon.
For systems running macOS, programs are distributed in the Apple Disk Image format, identified as DMG files. Variants of the open source Linux file system natively support mounting disk images as virtual disks.
Disk image vs. disk clone vs. golden image
A disk image, disk clone and golden image have similarities in that each produces a replica of all the contents on a drive. However, there are some differences:
- A disk image is a compressed copy of a prepared application environment that allows a granular data restore to occur. Multiple images can be stored per disk and incrementally updated.
- A disk clone is an uncompressed copy of a drive that can be immediately used in a production environment to replace a failing HDD. Cloning is faster than creating a disk image, but only one clone per disk can be stored, and new data can't be added to a clone.
- A golden image is a snapshot of a configured disk, server, system or VM that is used to deploy new instances on a network. Master image and clone image are synonymous terms with golden image.
Are larger files harder to restore?
The size of a disk image can affect the complexity of restoration. Larger disk images that exceed several terabytes can present longer processing times, increased storage requirements and potential hardware limitations. Other important factors that can slow down restoration include the following:
- Read and write speeds. HDDs and some external drives might experience slow transfer rates when restoring large files, whereas SSDs generally offer faster performance.
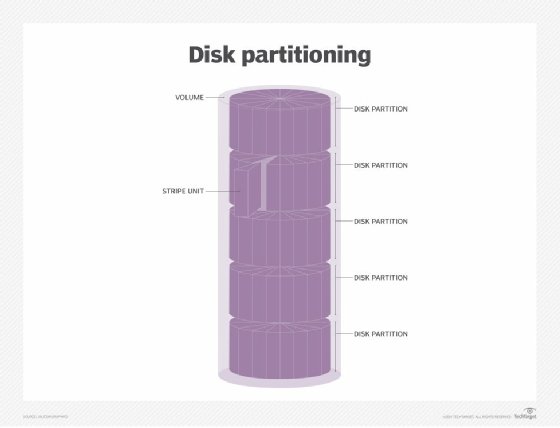
- Partition complexity. Multiple partitions or complex file system structures might require specialized software to ensure proper allocation and formatting.
- Storage capacity. The destination disk must have as much storage space as the backup disk image or else restoration is not possible.
- Optical media constraints. ISO images of large DVDs or Blu-ray discs might require multidisc spanning or specialized software to restore successfully.
Disk imaging pros and cons
Having an available reference machine image makes it easier for organizations to upgrade their computer environment. All computing devices that have had the disk image installed will have uniform configuration settings and programs, saving time when upgrading computers and peripheral components.
On the other hand, a disk image represents a snapshot of a drive at a given point in time. If new machines are added to the environment after the disk image is made, those newer devices might not receive security patches or software updates, delaying their provisioning for production environments.
Disk images are important for restoring files. Learn what you need to know about snapshots vs. backup.